Question: (a) (b) (c) Discuss how the Pretty Good Privacy (PGP) system can be used to provide both confidentiality and authentication protection, highlighting the algorithms
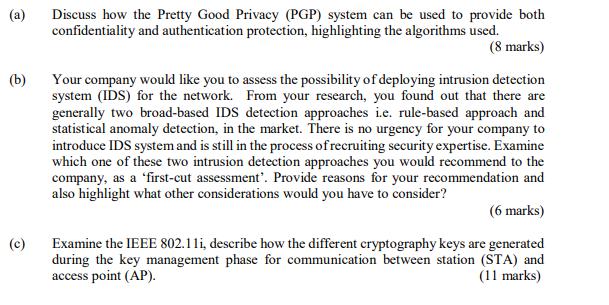
(a) (b) (c) Discuss how the Pretty Good Privacy (PGP) system can be used to provide both confidentiality and authentication protection, highlighting the algorithms used. (8 marks) Your company would like you to assess the possibility of deploying intrusion detection system (IDS) for the network. From your research, you found out that there are generally two broad-based IDS detection approaches i.e. rule-based approach and statistical anomaly detection, in the market. There is no urgency for your company to introduce IDS system and is still in the process of recruiting security expertise. Examine which one of these two intrusion detection approaches you would recommend to the company, as a 'first-cut assessment'. Provide reasons for your recommendation and also highlight what other considerations would you have to consider? (6 marks) Examine the IEEE 802.11i, describe how the different cryptography keys are generated during the key management phase for communication between station (STA) and access point (AP). (11 marks)
Step by Step Solution
There are 3 Steps involved in it
a Pretty Good Privacy PGP for Confidentiality and Authentication PGP is a widely used cryptographic system that provides both confidentiality and authentication through a combination of symmetric and ... View full answer

Get step-by-step solutions from verified subject matter experts


