Question: a) How are fixed passwords used to provide weak authentication? Include a discission of common attacks on fixed password schemes in your answer. [10 marks]
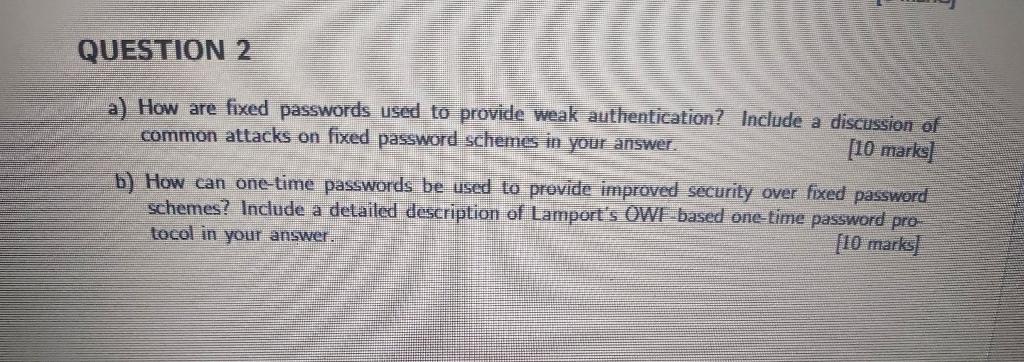
a) How are fixed passwords used to provide weak authentication? Include a discission of common attacks on fixed password schemes in your answer. [10 marks] b) How can one-time passwords be used to provide improved security over fixed password schemes? Include a detailed description of Lamport's. OWI based one-time password protocol in your answer. [10 marks]
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


