Question: A hypothetical cache memory has 512 bytes of data storage. The physical byte address is 32 bits long in this machine. Assume the cache
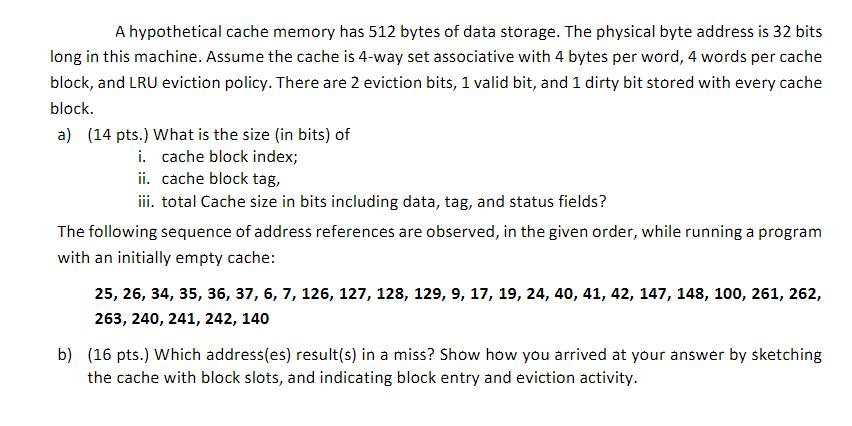
A hypothetical cache memory has 512 bytes of data storage. The physical byte address is 32 bits long in this machine. Assume the cache is 4-way set associative with 4 bytes per word, 4 words per cache block, and LRU eviction policy. There are 2 eviction bits, 1 valid bit, and 1 dirty bit stored with every cache block. a) (14 pts.) What is the size (in bits) of i. cache block index; ii. cache block tag, iii. total Cache size in bits including data, tag, and status fields? The following sequence of address references are observed, in the given order, while running a program with an initially empty cache: 25, 26, 34, 35, 36, 37, 6, 7, 126, 127, 128, 129, 9, 17, 19, 24, 40, 41, 42, 147, 148, 100, 261, 262, 263, 240, 241, 242, 140 b) (16 pts.) Which address(es) result(s) in a miss? Show how you arrived at your answer by sketching the cache with block slots, and indicating block entry and eviction activity.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


