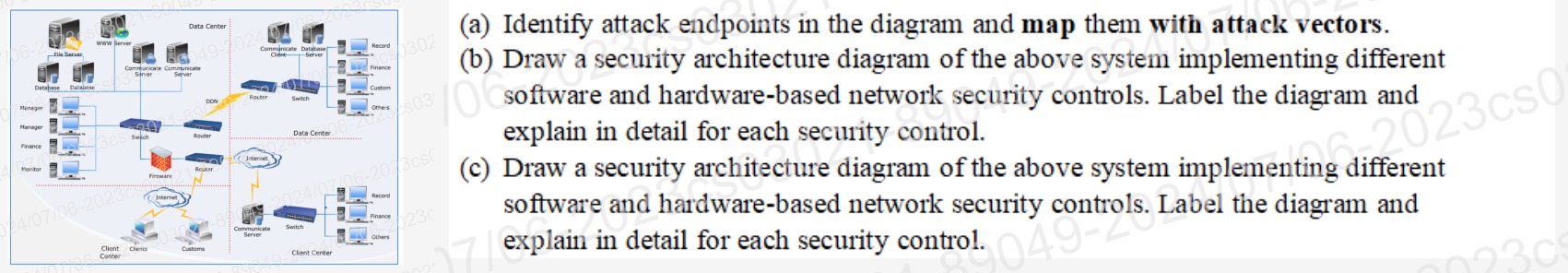
Question: ( a ) Identify attack endpoints in the diagram and map them with attack vectors. ( b ) Draw a security architecture diagram of the
a Identify attack endpoints in the diagram and map them with attack vectors.
b Draw a security architecture diagram of the above system implementing different software and hardwarebased network security controls. Label the diagram and explain in detail for each security control.
c Draw a security architecture diagram of the above system implementing different software and hardwarebased network security controls. Label the diagram and explain in detail for each security control.
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


