Question: A man - in - the - mobile and a man - in - the - middle attack have what similar qualities? More than one
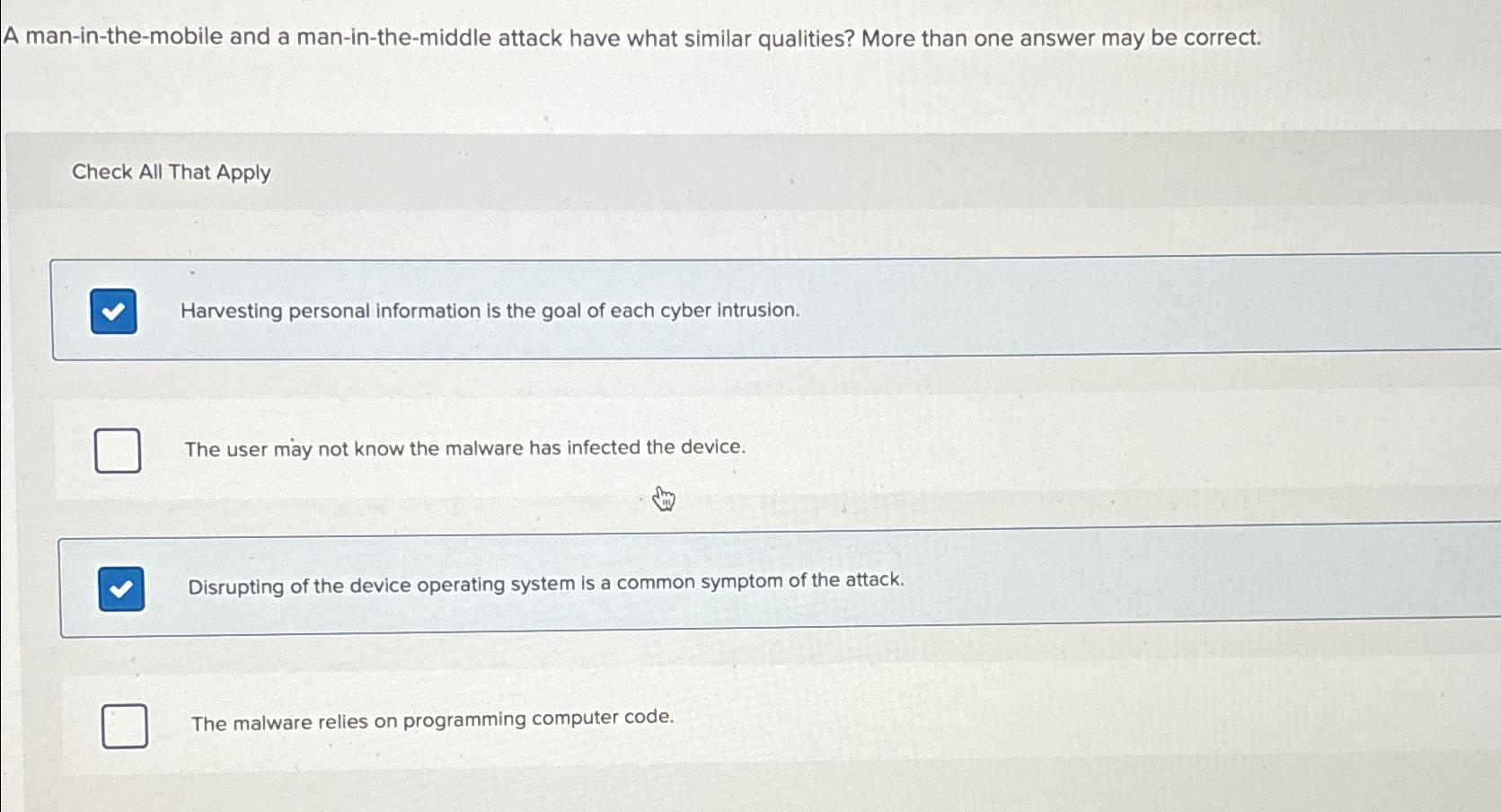
A maninthemobile and a maninthemiddle attack have what similar qualities? More than one answer may be correct.
Check All That Apply
Harvesting personal information is the goal of each cyber intrusion.
The user may not know the malware has infected the device.
Disrupting of the device operating system is a common symptom of the attack.
The malware relies on programming computer code.
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


