Question: A penetration tester uses an exploited network printer as a base of operations to expand access to vaous waksttons whehof tobdourg BEST describes the tester's
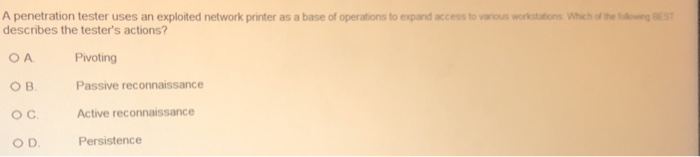
A penetration tester uses an exploited network printer as a base of operations to expand access to vaous waksttons whehof tobdourg BEST describes the tester's actions? OA O B. OC O D Pivoting Passive reconnaissance Active reconnaissance Persistence
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


