Question: a) State TWO (2) differences between ethics and law. (4 marks) b) List TWO (2) key points on deontological theories of ethics using a
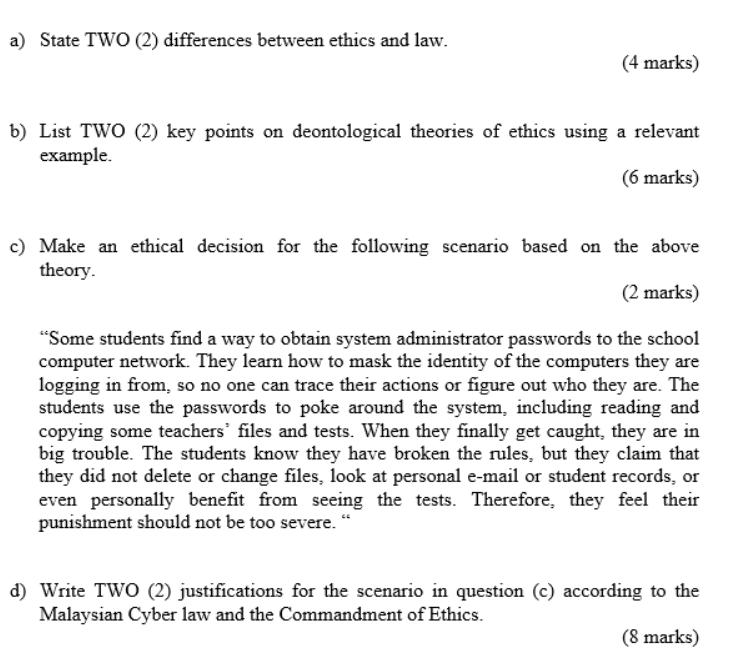
a) State TWO (2) differences between ethics and law. (4 marks) b) List TWO (2) key points on deontological theories of ethics using a relevant example. (6 marks) c) Make an ethical decision for the following scenario based on the above theory. (2 marks) "Some students find a way to obtain system administrator passwords to the school computer network. They learn how to mask the identity of the computers they are logging in from, so no one can trace their actions or figure out who they are. The students use the passwords to poke around the system, including reading and copying some teachers' files and tests. When they finally get caught, they are in big trouble. The students know they have broken the rules, but they claim that they did not delete or change files, look at personal e-mail or student records, or even personally benefit from seeing the tests. Therefore, they feel their punishment should not be too severe. d) Write TWO (2) justifications for the scenario in question (c) according to the Malaysian Cyber law and the Commandment of Ethics. (8 marks)
Step by Step Solution
3.32 Rating (152 Votes )
There are 3 Steps involved in it
The image contains a set of questions related to ethics law and a specific scenario involving the misuse of system administrator passwords by students I will address each question based on the informa... View full answer

Get step-by-step solutions from verified subject matter experts


