a) This question places you in the position of a computer network manager required to develop an
Question:
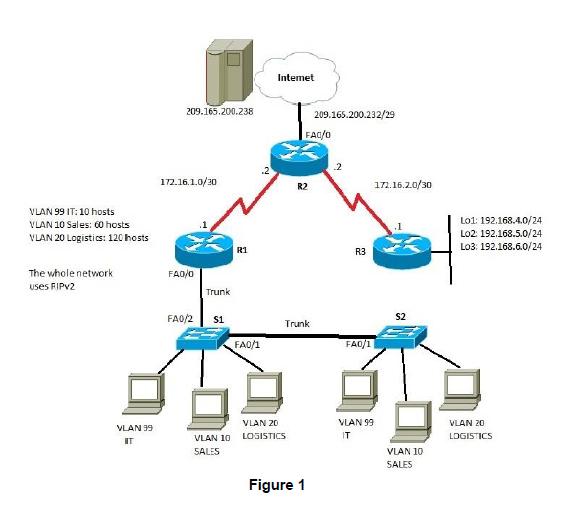
a) This question places you in the position of a computer network manager required to develop an IPv4 addressing scheme for the VLAN part of the topology given in Figure 1, fulfilling all requirements given in the diagram. Your addressing scheme needs to make the most efficient use of IP addresses.
Your base network address for developing the VLAN part of your network is 192.10.10.0/24. Please include a table showing for each subnet its network address, first and last usable host address, broadcast address and subnet mask.
You should then assign addresses to the relevant interfaces on R1's fast ethernet interface, together with the virtual addresses for S1 and S2. Please provide these addresses, together with a brief justification of your addressing approach.
b) The network in Figure 1 uses RIPv2 as its dynamic routing protocol. You are required to streamline the dynamic routing process to avoid unnecessary routing updates. You also need to consider how to provide dynamic updates from R2 to R1 and R2 to R3, advertising access to the Internet. Explain how you would achieve these two requirements? Please provide brief outlines of relevant Cisco IOS commands you would use to implement these requirements.
c) The switched network part in Figure 1 does currently not provide any redundancy. What are the benefits of network redundancy? Which changes to the VLAN part of the network in Figure 1 would you suggest to provide network redundancy? Please provide a network diagram, together with a brief justification of your approach.
d) The network in Figure 1 makes use of a classless IPv4 addressing scheme. Please give an outline of the historical development of IPv4 from a classful to a classless addressing scheme. You should refer to the appropriate RFCs in your answer.
Question 2
a) What is the purpose of 'portfast' and how do you enable it on a CISCO IOS switch?
b) Please explain how port security blocks unauthorized access.
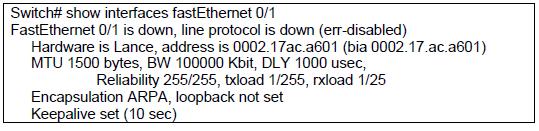
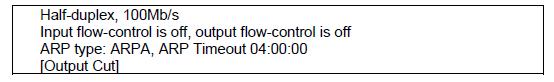
c) You have configured port security on a switch. However, as a network engineer, you have found that the port is no longer active. The terminal shows the following information:

Intermediate Financial Management
ISBN: 978-1111530266
11th edition
Authors: Eugene F. Brigham, Phillip R. Daves