A1. What is cyber security operation, describe five KPIs of the cyber security operations capability of...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
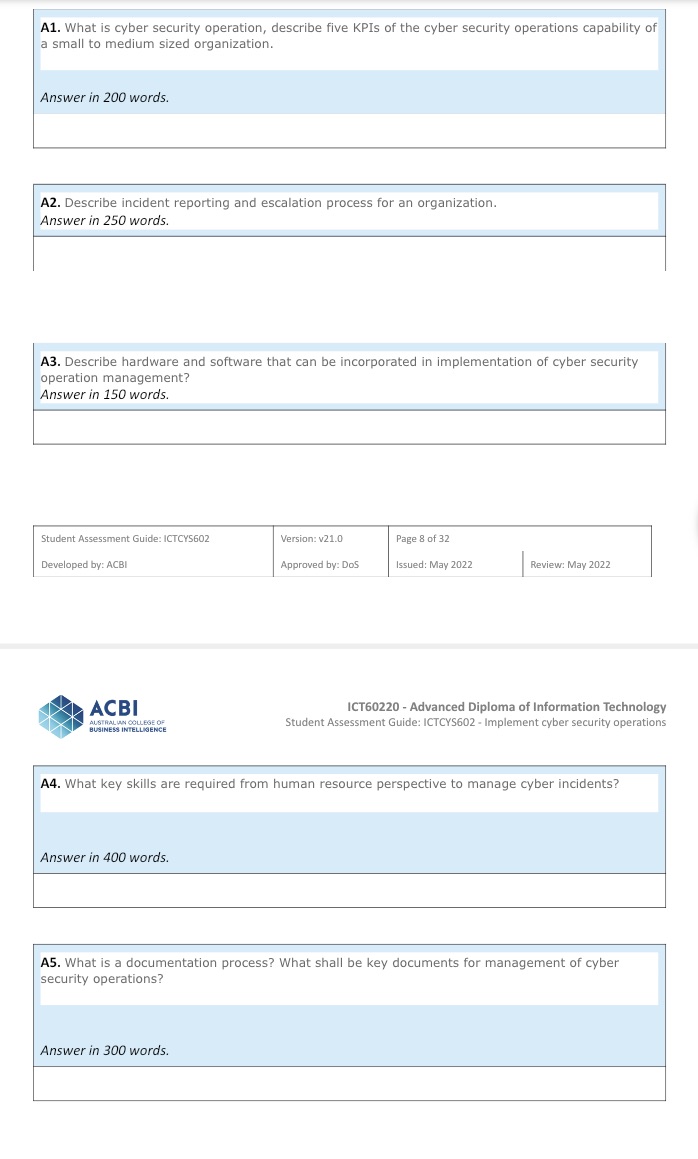
A1. What is cyber security operation, describe five KPIs of the cyber security operations capability of a small to medium sized organization. Answer in 200 words. A2. Describe incident reporting and escalation process for an organization. Answer in 250 words. A3. Describe hardware and software that can be incorporated in implementation of cyber security operation management? Answer in 150 words. Student Assessment Guide: ICTCYS602 Version: v21.0 Page 8 of 32 Developed by: ACBI Approved by: DoS Issued: May 2022 Review: May 2022 ACBI AUSTRALIAN COLLEGE OF BUSINESS INTELLIGENCE ICT60220 - Advanced Diploma of Information Technology Student Assessment Guide: ICTCYS602 - Implement cyber security operations A4. What key skills are required from human resource perspective to manage cyber incidents? Answer in 400 words. A5. What is a documentation process? What shall be key documents for management of cyber security operations? Answer in 300 words. A1. What is cyber security operation, describe five KPIs of the cyber security operations capability of a small to medium sized organization. Answer in 200 words. A2. Describe incident reporting and escalation process for an organization. Answer in 250 words. A3. Describe hardware and software that can be incorporated in implementation of cyber security operation management? Answer in 150 words. Student Assessment Guide: ICTCYS602 Version: v21.0 Page 8 of 32 Developed by: ACBI Approved by: DoS Issued: May 2022 Review: May 2022 ACBI AUSTRALIAN COLLEGE OF BUSINESS INTELLIGENCE ICT60220 - Advanced Diploma of Information Technology Student Assessment Guide: ICTCYS602 - Implement cyber security operations A4. What key skills are required from human resource perspective to manage cyber incidents? Answer in 400 words. A5. What is a documentation process? What shall be key documents for management of cyber security operations? Answer in 300 words.
Expert Answer:

Posted Date:
Students also viewed these computer network questions
-
Discrete probability variables are countable meaning that we can count the number of favorable outcomes. What are permutations and combinations? What role do they play in calculating probabilities?
-
Literature Review Examples Find a peer-reviewed literature review article that you will use as a source in your literature review. In three hundred words provide a critical analysis of the article...
-
You and your team have just been hired by a privately owned company that is considering several strategic options. ITStaffing, Inc. ("ITS" or the "Company") is one of the fastest growing information...
-
We are given a number of darts. Suppose it is known that each time we throw a dart at a target, we have a probability of 1/4 of hitting the target. An experiment consists of throwing three darts at...
-
What is the difference between technical feasibility and operational feasibility?
-
Find the derivative of the function. f(t) = tan(e t ) + e tan t
-
What are business processes? How are they related to information systems? Define business processes and describe the role they play in organizations. Describe the relationship between information...
-
The management of Weimar Inc., a civil engineering design company, is considering an investment in a high-quality blueprint printer with the following cash flows: Required: 1. Determine the payback...
-
2.Research and summarize the Lehman Brothers and Madoff scandals from 2008. What was the Accountant's involvement. What was the result? Include 3 references cited! 4. Research any large recent co...
-
My fallacy is "Begging the Question" and the topic i chose is childhood vaccinations. Can you provide an example of argument that uses my selected fallacy that is "Begging the Question" on the topic...
-
Choose and identify one type of behavioral bias briefly explain why the selected incidence demonstrates behavioral bias. propose a plan to deal with the bias when you doing a client's profile as a...
-
- Elaborate on other application layer protocols that are suitable to IoT and how do they compared to HTTP? - List some other HTTP methods and what they are used for. - How are GET/POST command is...
-
Casey Associates is a recently formed law partnership. Casey Associates operates at capacity and uses a cost-based approach to pricing (billing) each job. Casey currently uses a simple costing...
-
Deliverable A 1-page document (single-spaced, 12pt font, not "front-and-back") that summarizes 2 cyber security attacks from within the past 3 years, including the following information: o Victim of...
-
Bismite Corporation purchases trees from Cheney lumber and processes them up to the split-off point where two products (paper and pencil casings) emerge from the process. The products are then sold...
-
Explain the role of brands in a monopolistic competition market. How can the pricing and profits for a firm in this market structure differ from perfect competition and when will the two market types...
-
On January 2, 20X3, Sheldon Bass, a professional engineer, moved from Calgary to Edmonton to commence employment with Acco Ltd., a large public corporation. Because of his new employment contract,...
-
The Harvey Corporation is considering a change in its cash-only policy. The new terms would be net one period. Based on the following information, determine if Harvey should proceed or not. The...
-
Ogello, Inc., is considering a change in its cash-only sales policy. The new terms of sale would be net one month. Based on the following information, determine if Ogello should proceed or not....
-
La Bartolomeo Systems currently has an allcash credit policy. It is considering making a change in the credit policy by going to terms of net 30 days. Based on the following information, what do you...

Study smarter with the SolutionInn App

