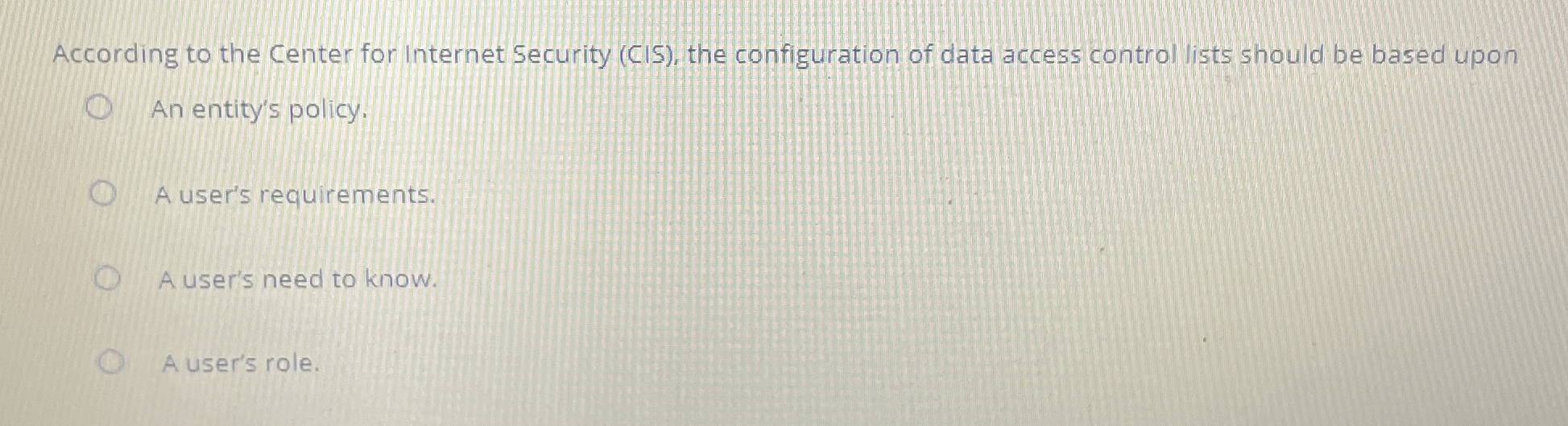
Question: According to the Center for Internet Security ( CIS ) , the configuration of data access control lists should be based upon An entity's policy.
According to the Center for Internet Security CIS the configuration of data access control lists should be based upon
An entity's policy.
A user's requirements.
A user's need to know.
A user's role.
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


