Question: Alice and Bob shared an n-bit secret key some time ago. Now they are no longer sure they still have the same key. Thus, they
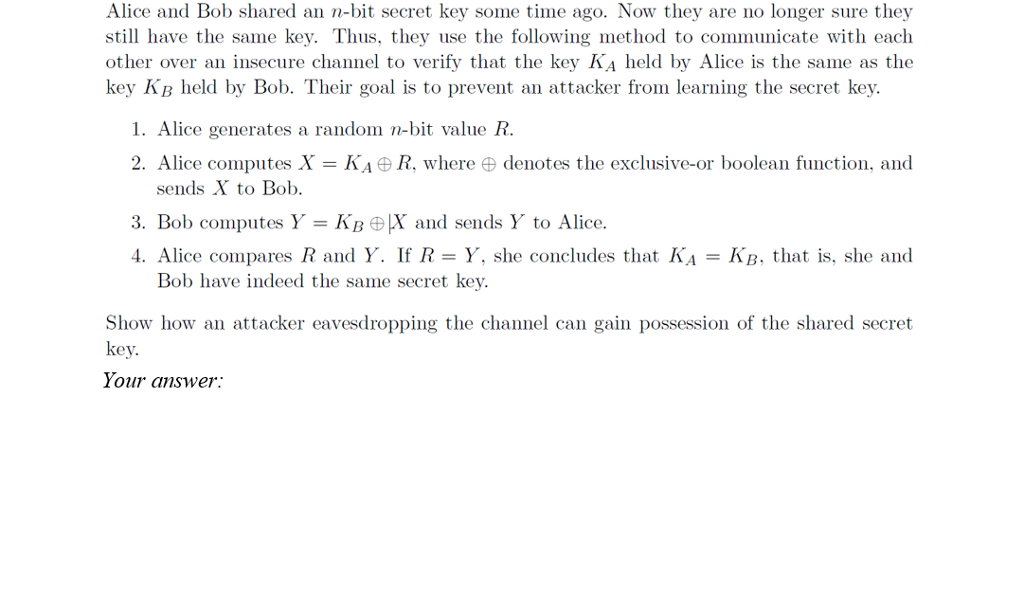
Alice and Bob shared an n-bit secret key some time ago. Now they are no longer sure they still have the same key. Thus, they use the following method to communicate with each other over an insecure channel to verify that the key KA held by Alice is the same as the key Kp held by Bob. Their goal is to prevent an attacker from learning the secret key. 1. Alice generates a random n-bit value R. 2. Alice computes X = KA DR. where denotes the exclusive or boolean function, and sends X to Bob. 3, Bob computes Y = KBK and sends Y to Alice. 4, Alice compares R and Y. If R = Y, she concludes that KA-KB, that is, she and Bob have indeed the same secret key. Show how an attacker eavesdropping the channel can gain possession of the shared secret key. Your
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


