Question: Alice needs to authenticate to the web service using port 380 on the host hw2.csec380.fun. In this assignment, you will write several python scripts
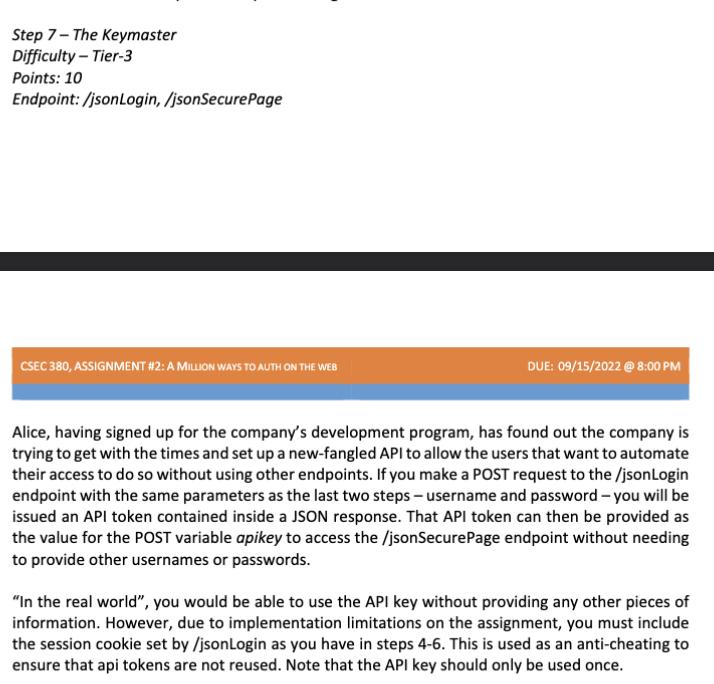
Alice needs to authenticate to the web service using port 380 on the host hw2.csec380.fun. In this assignment, you will write several python scripts that will allow Alice to authenticate to a remote web server using only sockets and strings without many libraries that were usable in previous assignments. Alice's username will always be alice and Alice's password will always be SecretPassword123!. Each step of the assignment will get progressively more challenging. You must submit a different Python script for each step. Each python script must print the last HTTP response your script received in its entirety. With the exception of Step 1 and Step 2, each step is complete when you receive a 200 HTTP response containing the message "Welcome Alice!". Pay close attention to the HTTP responses you receive. The web server has been build to provide error messages - which can sometimes be a little silly - that inform you of common mistakes. All attempts to log in must be automated. Step 7-The Keymaster Difficulty - Tier-3 Points: 10 Endpoint:/jsonLogin, /jsonSecure Page CSEC 380, ASSIGNMENT #2: A MILLION WAYS TO AUTH ON THE WEB DUE: 09/15/2022 @ 8:00 PM Alice, having signed up for the company's development program, has found out the company is trying to get with the times and set up a new-fangled API to allow the users that want to automate their access to do so without using other endpoints. If you make a POST request to the /jsonLogin endpoint with the same parameters as the last two steps - username and password - you will be issued an API token contained inside a JSON response. That API token can then be provided as the value for the POST variable apikey to access the /jsonSecurePage endpoint without needing to provide other usernames or passwords. "In the real world", you would be able to use the API key without providing any other pieces of information. However, due to implementation limitations on the assignment, you must include the session cookie set by /jsonLogin as you have in steps 4-6. This is used as an anti-cheating to ensure that api tokens are not reused. Note that the API key should only be used once.
Step by Step Solution
There are 3 Steps involved in it
Here is the Python script for Step 7 PYTHON import requests url httpshw2csec380fun380jsonLogin data ... View full answer

Get step-by-step solutions from verified subject matter experts


