An 8 GB RAM module uses 32-bit words. A bidirectional bus transmits data from the memory...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
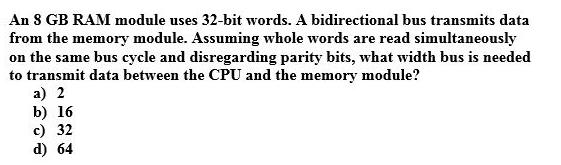
An 8 GB RAM module uses 32-bit words. A bidirectional bus transmits data from the memory module. Assuming whole words are read simultaneously on the same bus cycle and disregarding parity bits, what width bus is needed to transmit data between the CPU and the memory module? a) 2 b) 16 c) 32 d) 64 An 8 GB RAM module uses 32-bit words. A bidirectional bus transmits data from the memory module. Assuming whole words are read simultaneously on the same bus cycle and disregarding parity bits, what width bus is needed to transmit data between the CPU and the memory module? a) 2 b) 16 c) 32 d) 64
Expert Answer:
Answer rating: 100% (QA)
8GB RAM module use 32bit words And the whole words are read simultaneous... View the full answer

Related Book For 

Posted Date:
Students also viewed these operating system questions
-
What minimum bandwidth is needed to transmit a pulse that consists of 100 cycles of a 1.00 MHz oscillation?
-
A DMA module is transferring characters to memory using cycle stealing, from a device transmitting at 9600 bps. The processor is fetching instructions at the rate of 1 million instructions per second...
-
A computer has 4 GB of RAM of which the operating system occupies 512 MB. The processes are all 256 MB (for simplicity) and have the same characteristics. If the goal is 99% CPU utilization, what is...
-
Briefly explain the meaning of the following concepts and terms: greenhouse gases (GHGs), the IPCC, the little ice age, the Keeling graph, telekinetic property of the atmosphere, global weirding,...
-
What are the three major types of negotiated remedies and how do they differ?
-
Plankton Corporations trial balance at December 31, 2015, is presented below: All transactions and adjustments for 2015 have been recorded and reported in the trial balance except for the items...
-
1. Multi-National Marriott Hotels Could Face Consumer Backlash and up to $1 Billion in Regulatory Fines and Litigation Costs for Massive Data Breach Marriott had sustained several cyberattacks prior...
-
Kabana Company, a manufacturer of stereo systems, started its production in October 2012. For the preceding 3 years Kabana had been a retailer of stereo systems. After a thorough survey of stereo...
-
Multiply the first equation by 2. Give the abbreviation of the indicated operation. 2* - 2y = 5 2x+5y = 2 x + The transformed system is y = (Simplify your answers.) 2x + 5y= 2.
-
A cylindrical specimen of aluminum having a diameter of 0.505 in. (12.8 mm) and a gauge length of 2.000 in. (50.800 mm) is pulled in tension. Use the load?elongation characteristics tabulated below...
-
This is a "Virtual Lab". You will be using a free online lab simulation from the University of Colorado Boulder. Go to the following link for the virtual lab:...
-
Which point of view in Debate 1.2 do you find most compelling? Why? What logic or evidence do you find most supportive of that position? Debate 1. 2 DEBATE 1.2 What Does the Future Hold? Is the...
-
Positive and negative feedback loops lie at the core of systematic thinking about the future. As you examine the key forces shaping the future, what examples of positive and negative feedback loops...
-
In primitive societies, the entitlements to use land were frequently possessory rights rather than ownership rights. Those on the land could use it as they wished, but they could not transfer it to...
-
In a well-known legal case, Miller v. Schoene (287 U.S. 272), a classic conflict of property rights was featured. Red cedar trees, used only for ornamental purposes, carried a disease that could...
-
This chapter contains two views of the future. Since the validity of these views cannot be completely tested until the time period covered by the forecast has passed (so that predictions can be...
-
5) a) Consider a processor with two levels of cache with the following properties: L1 Hit rate: 90%, L1 Access (hit): 4 cycles, L2 Hit Rate: 80%, L2 Access (hit): 12 cycles, DRAM Hit Rate: 100%, DRAM...
-
Listed below are common types of current liabilities, contingencies, and commitments: a. Accounts payable b. Bank loans and commercial paper c. Notes payable d. Dividends payable e. Sales and excise...
-
Suppose that a machine has 48-bit virtual addresses and 32-bit physical addresses. (a) If pages are 4 KB, how many entries are in the page table if it has only a single level? Explain. (b) Suppose...
-
Hierarchical file names always start at the top of the tree. Consider, for example, the file name /usr/ast/books/mos2/chap-12 rather than chap-12/mos2/books/ast/usr. In contrast, DNS names start at...
-
In Windows it is easy to implement a facility where threads running in the kernel can temporarily attach to the address space of a different process. Why is this so much harder to implement in user...
-
Why do organizations conduct marketing research?
-
What are some of the issues that should be considered when conducting marketing research?
-
What is the main difference between a full-service and a limited-service supplier?

Study smarter with the SolutionInn App


