Question: An application uses a serialized object from user input. An attacker provides a malicious serialized object. What vulnerability could this be ? Command Injection Path
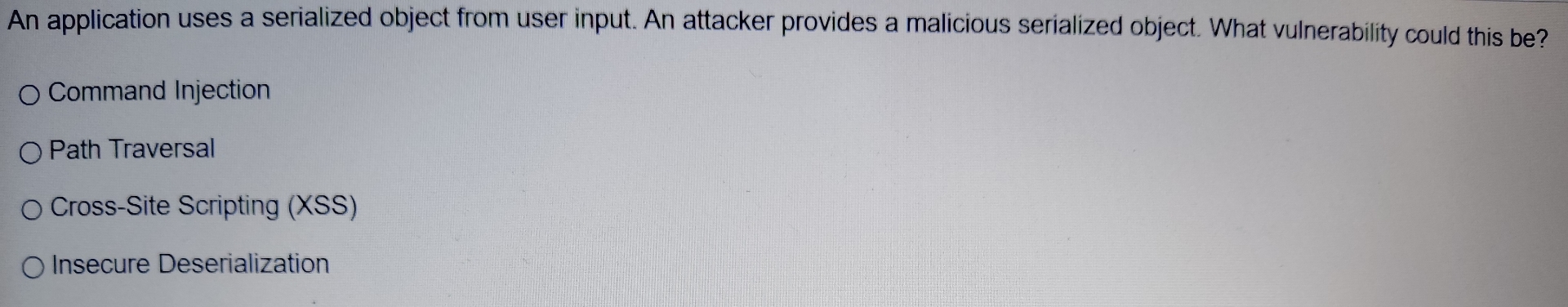
An application uses a serialized object from user input. An attacker provides a malicious serialized object. What vulnerability could this be
Command Injection
Path Traversal
CrossSite Scripting XSS
Insecure Deserialization
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


