Question: An attacker has implemented a persistent rootkit by overwriting the bootloader in the master boot record (sector 0 of the disk) with their own
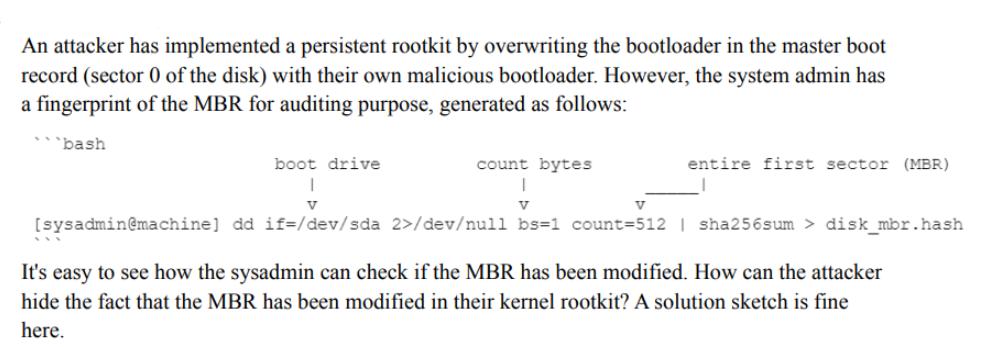
An attacker has implemented a persistent rootkit by overwriting the bootloader in the master boot record (sector 0 of the disk) with their own malicious bootloader. However, the system admin has a fingerprint of the MBR for auditing purpose, generated as follows: bash boot drive count bytes 1 V V [sysadmin@machine] dd if= /dev/sda 2>/dev/null bs=1 count=512 | sha256sum > disk_mbr.hash It's easy to see how the sysadmin can check if the MBR has been modified. How can the attacker hide the fact that the MBR has been modified in their kernel rootkit? A solution sketch is fine here. entire first sector (MBR) V
Step by Step Solution
3.47 Rating (150 Votes )
There are 3 Steps involved in it
The attackers objective is to hide the fact that the MBR has been modified by their kernel rootkit from the system administrator Here is a solution sk... View full answer

Get step-by-step solutions from verified subject matter experts


