Ann was very keen to know the contents of the report written by her supervisor about...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
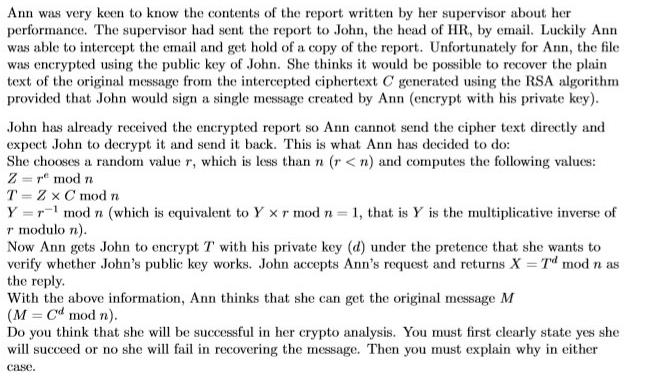
Ann was very keen to know the contents of the report written by her supervisor about her performance. The supervisor had sent the report to John, the head of HR, by email. Luckily Ann was able to intercept the email and get hold of a copy of the report. Unfortunately for Ann, the file was encrypted using the public key of John. She thinks it would be possible to recover the plain text of the original message from the intercepted ciphertext C generated using the RSA algorithm provided that John would sign a single message created by Ann (encrypt with his private key). John has already received the encrypted report so Ann cannot send the cipher text directly and expect John to decrypt it and send it back. This is what Ann has decided to do: She chooses a random value r, which is less than n (r < n) and computes the following values: Z = r" mod n T = Z x C mod n Y =r mod n (which is equivalent to Y xr mod n = 1, that is Y is the multiplicative inverse of r modulo n). Now Ann gets John to encrypt T with his private key (d) under the pretence that she wants to verify whether John's public key works. John accepts Ann's request and returns X Td mod n as the reply. With the above information, Ann thinks that she can get the original message M (M = Cd mod n). Do you think that she will be successful in her crypto analysis. You must first clearly state yes she will succeed or no she will fail in recovering the message. Then you must explain why in either case. Ann was very keen to know the contents of the report written by her supervisor about her performance. The supervisor had sent the report to John, the head of HR, by email. Luckily Ann was able to intercept the email and get hold of a copy of the report. Unfortunately for Ann, the file was encrypted using the public key of John. She thinks it would be possible to recover the plain text of the original message from the intercepted ciphertext C generated using the RSA algorithm provided that John would sign a single message created by Ann (encrypt with his private key). John has already received the encrypted report so Ann cannot send the cipher text directly and expect John to decrypt it and send it back. This is what Ann has decided to do: She chooses a random value r, which is less than n (r < n) and computes the following values: Z = r" mod n T = Z x C mod n Y =r mod n (which is equivalent to Y xr mod n = 1, that is Y is the multiplicative inverse of r modulo n). Now Ann gets John to encrypt T with his private key (d) under the pretence that she wants to verify whether John's public key works. John accepts Ann's request and returns X Td mod n as the reply. With the above information, Ann thinks that she can get the original message M (M = Cd mod n). Do you think that she will be successful in her crypto analysis. You must first clearly state yes she will succeed or no she will fail in recovering the message. Then you must explain why in either case.
Expert Answer:
Answer rating: 100% (QA)
Required solution Answer Yes Ann can retrieve the m... View the full answer

Related Book For 

Posted Date:
Students also viewed these accounting questions
-
It would be possible to calculate a one-way chi-square test on the data in column 1 of Exercise 19.12. What hypothesis would you be testing if you did that? How would that hypothesis differ from the...
-
1. Do you think it would be possible to sum up the resulting values and make a decision based only on the numbers? Support your answer. 2. What factors, other than those in the matrix of weighted...
-
Do you think it would be possible to have an aromatic free radical? Why or why not?
-
Two billiard balls of equal mass undergo a perfectly elastic head-on collision. If one balls initial speed was 2.00m/s, and the others was 3.00m/s in the opposite direction, what will be their speeds...
-
What is the smallest temperature in degrees Celsuis you can have? Kelvin?
-
Write equations showing how 1-phenylethanol (C6H5CHCH3) could be prepared from each of the following starting materials: (a) Bromobenzene (d) Acetophenone (b) Benzaldehyde (e) Benzene (c) Benzyl...
-
Mrs. Clarks Foods was an Iowa company engaged in the business of distributing juice beverages. International Suntrade and Miller & Smith Foods were Canadian companies that acted as brokers...
-
In the spring of 2013 the Caswell Publishing Company established a custom publishing business for its business clients. These clients consisted principally of small- to medium-size companies in Round...
-
Cash Receipt Schemes and Other Asset Misappropriations, identify and describe two big data and data analytic techniques each for detecting skimming, cash larceny, and noncash misappropriations.
-
Cardinal Company is considering a five-year project that would require a $2,975,000 investment in equipment with a useful life of five years and no salvage value . The company's discount rate is 14%....
-
Web Analytics at Quality Alloys Case: Please provide answers for the questions below based on the information provided in the case and the spreadsheet provided Please provide the average number of...
-
Referring to the daily-return graphs for the SPDR S&P 500 ETF Trust (SPY) and the Direxion Daily Junior Gold Miners Index Bull 2X Shares (JNUG) given below: 10 10-1 SPY 10 Empirical Gaussian 10-1...
-
Question 2. Suppose that, in an election with two candidates, there are six voters, 1, 2, 3, 4, 5, and 6, who are all concerned with the same issue. Voter i has a single-peaked preference with a peak...
-
Michael decides to drive because he's excited about his new car, plus, he thinks the firm owes him for having suffered too many poor flights on previous trips. What is the opportunity cost to the...
-
There are two piles, one containing 9 gold coins and the other11 silver coins. The two piles of coins weigh the same. One coin istaken from each pile and put into the other. It is now found thatthe...
-
Hello! I have an idea of what is being asked but want to make sure I am making the right suggestions. I attached the assumptions and the picture of the NPV for each investment. Thank you. 1....
-
This formula applies to Oany object of total surface area A, Kelvin temperature T, and emissivity e O any object of cross-sectional area A, Kelvin temperature T, and emissivity e O any object of...
-
How is use of the word consistent helpful in fraud reports?
-
Describe several advantages of recruiting from internal sources and several advantages of recruiting from external sources.
-
Outline five steps to follow in training a new employee to perform a job.
-
Discuss how career-related myths can inhibit career planning and growth.
-
Starting with Eq. (4.62), derive Eq. (4.63). Data From Equation (4.62) Data From Equation (4.63)
-
You want to design a side looking synthetic aperture ultrasonic radar operating at f0 = 60 KHz and peak power Pt = 2 W. The antenna beam is conical with 3dB beam width 3dB = 5. The maximum gain is...
-
In reference to Figure 4.18, assume a radar height of \(h_{r}=100 \mathrm{~m}\) and a target height of \(h_{t}=500 \mathrm{~m}\). The range is \(R=20 \mathrm{~km}\). (a) Calculate the lengths of the...

Study smarter with the SolutionInn App