Question: Answer the following questions about the vulnerable code below void test Fune(int a, double b) { char buf(10); //line 1 gets (buf): //line 2 int
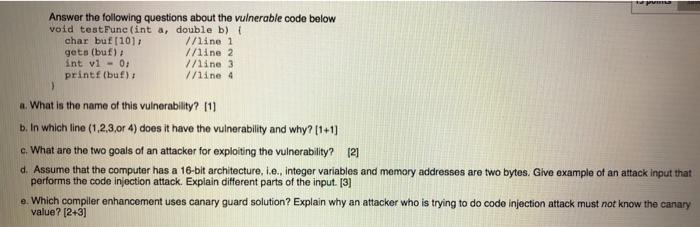
Answer the following questions about the vulnerable code below void test Fune(int a, double b) { char buf(10); //line 1 gets (buf): //line 2 int v1 - 0 //line 3 printf (buf): //line 4 a. What is the name of this vulnerability? 111 b. In which line (1,2,3,or 4) does it have the vulnerability and why? 1+1] c. What are the two goals of an attacker for exploiting the vulnerability? 121 d. Assume that the computer has a 16-bit architecture, i.e. Integer variables and memory addresses are two bytes. Glve example of an attack input that performs the code injection attack. Explain different parts of the input. [3] e. Which compiler enhancement uses canary guard solution? Explain why an attacker who is trying to do code injection attack must not know the canary value? (2+3)
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


