As society becomes more reliant on digital technology, there's an ever-growing necessity for strong cybersecurity measures....
Fantastic news! We've Found the answer you've been seeking!
Question:
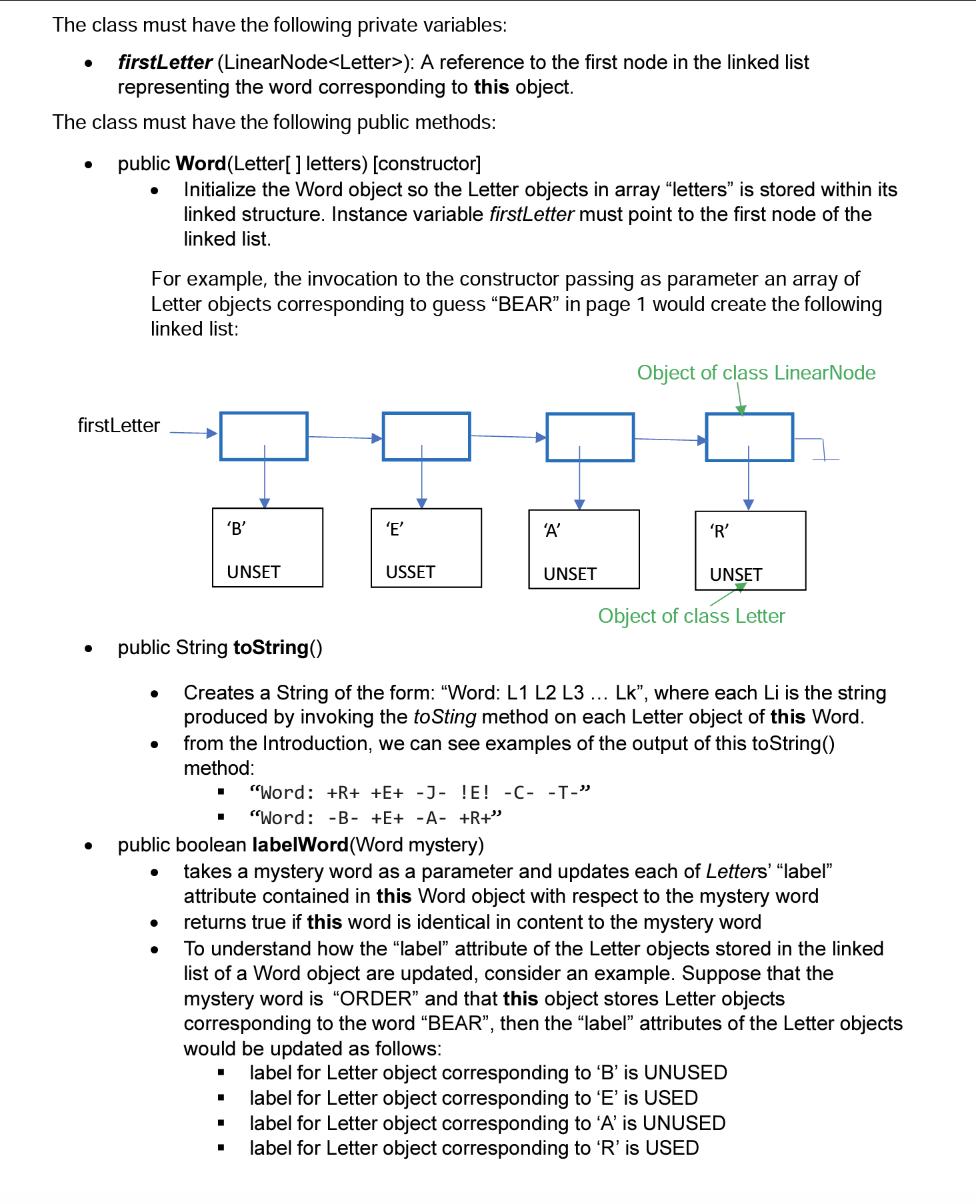



Transcribed Image Text:
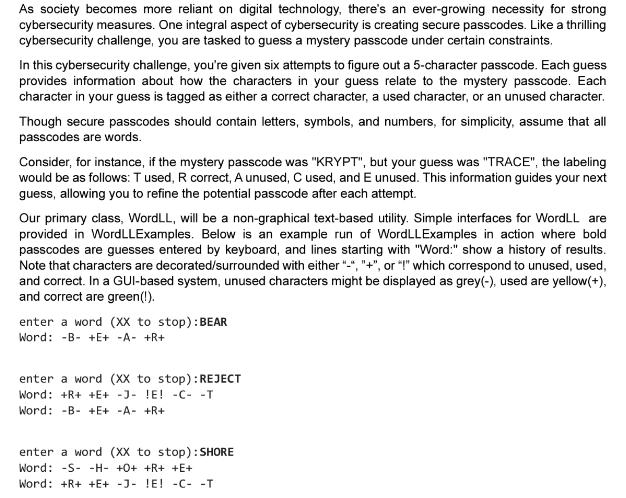
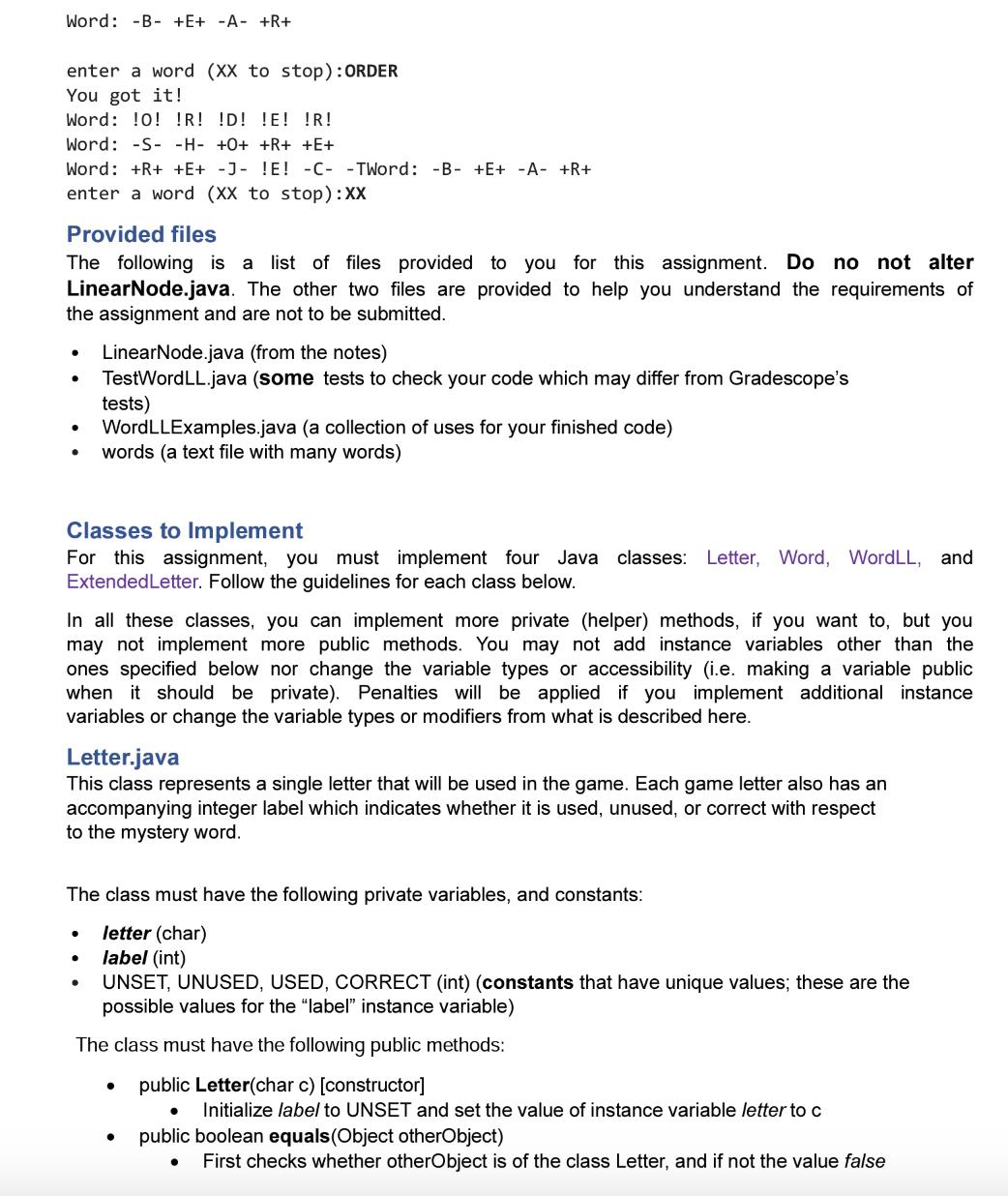
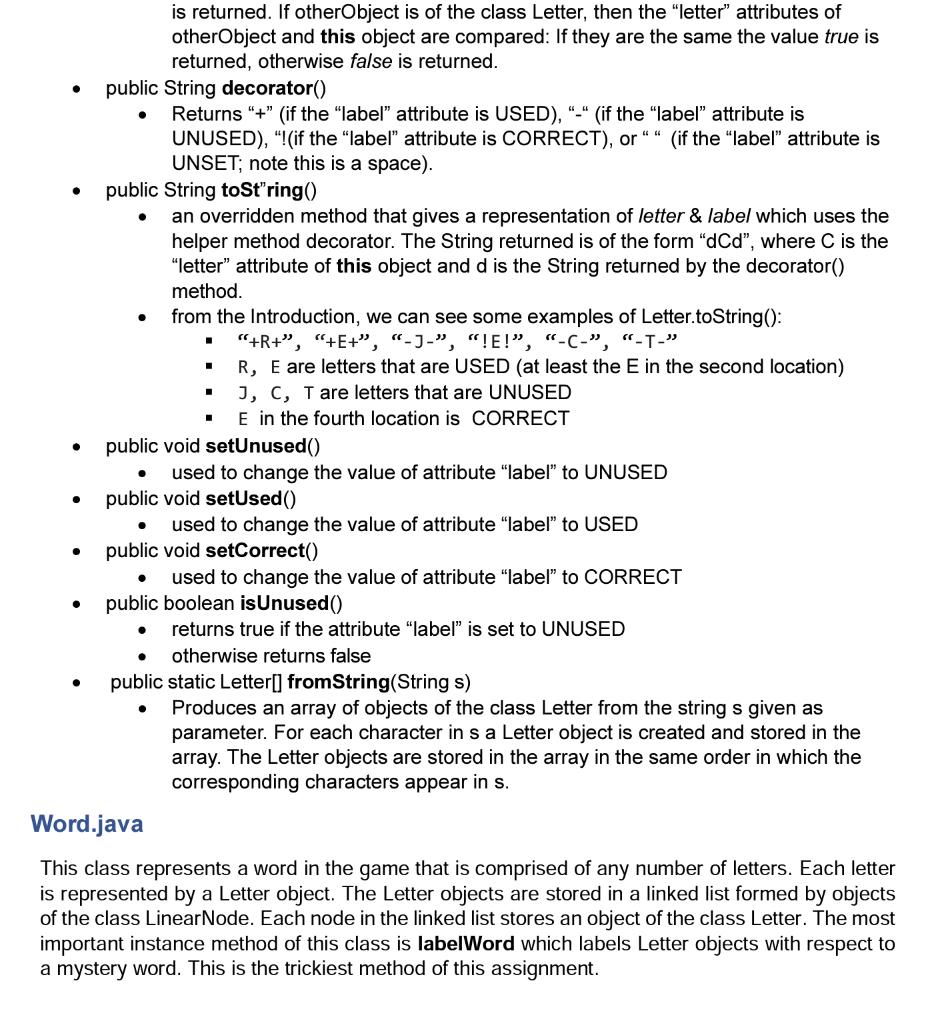
As society becomes more reliant on digital technology, there's an ever-growing necessity for strong cybersecurity measures. One integral aspect of cybersecurity is creating secure passcodes. Like a thrilling cybersecurity challenge, you are tasked to guess a mystery passcode under certain constraints. In this cybersecurity challenge, you're given six attempts to figure out a 5-character passcode. Each guess provides information about how the characters in your guess relate to the mystery passcode. Each character in your guess is tagged as either a correct character, a used character, or an unused character. Though secure passcodes should contain letters, symbols, and numbers, for simplicity, assume that all passcodes are words. Consider, for instance, if the mystery passcode was "KRYPT", but your guess was "TRACE", the labeling would be as follows: Tused, R correct, A unused, C used, and E unused. This information guides your next guess, allowing you to refine the potential passcode after each attempt. Our primary class, WordLL, will be a non-graphical text-based utility. Simple interfaces for WordLL are provided in WordLLExamples. Below is an example run of WordLLExamples in action where bold passcodes are guesses entered by keyboard, and lines starting with "Word:" show a history of results. Note that characters are decorated/surrounded with either "-", "+", or "!" which correspond to unused, used, and correct. In a GUI-based system, unused characters might be displayed as grey(-), used are yellow(+), and correct are green(!). enter a word (XX to stop): BEAR Word: B- +E+ -A- +R+ enter a word (XX to stop): REJECT Word: +R+ +E+ -J- !E! -C- -T Word: B- +E+ -A- +R+ enter a word (XX to stop): SHORE Word: -S- -H- +0+ +R+ +E+ Word: +R+ +E+ -J- !E! -C- -T As society becomes more reliant on digital technology, there's an ever-growing necessity for strong cybersecurity measures. One integral aspect of cybersecurity is creating secure passcodes. Like a thrilling cybersecurity challenge, you are tasked to guess a mystery passcode under certain constraints. In this cybersecurity challenge, you're given six attempts to figure out a 5-character passcode. Each guess provides information about how the characters in your guess relate to the mystery passcode. Each character in your guess is tagged as either a correct character, a used character, or an unused character. Though secure passcodes should contain letters, symbols, and numbers, for simplicity, assume that all passcodes are words. Consider, for instance, if the mystery passcode was "KRYPT", but your guess was "TRACE", the labeling would be as follows: Tused, R correct, A unused, C used, and E unused. This information guides your next guess, allowing you to refine the potential passcode after each attempt. Our primary class, WordLL, will be a non-graphical text-based utility. Simple interfaces for WordLL are provided in WordLLExamples. Below is an example run of WordLLExamples in action where bold passcodes are guesses entered by keyboard, and lines starting with "Word:" show a history of results. Note that characters are decorated/surrounded with either "-", "+", or "!" which correspond to unused, used, and correct. In a GUI-based system, unused characters might be displayed as grey(-), used are yellow(+), and correct are green(!). enter a word (XX to stop): BEAR Word: B- +E+ -A- +R+ enter a word (XX to stop): REJECT Word: +R+ +E+ -J- !E! -C- -T Word: B- +E+ -A- +R+ enter a word (XX to stop): SHORE Word: -S- -H- +0+ +R+ +E+ Word: +R+ +E+ -J- !E! -C- -T
Expert Answer:
Answer rating: 100% (QA)
import javautil public class WordLL private String passcode private int attempts public ... View the full answer

Related Book For 

Smith and Roberson Business Law
ISBN: 978-0538473637
15th Edition
Authors: Richard A. Mann, Barry S. Roberts
Posted Date:
Students also viewed these programming questions
-
List of Accounts Sales Revenue 6 , 3 0 0 , 0 0 0 Income Tax Expense 2 0 % Interest expense 2 1 , 0 0 0 Cost of Goods Sold 4 , 1 0 0 , 0 0 0 Marketing, administrative, and other expenses 1 9 3 , 0 0 0...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
What operational changes would you recommend to Wally to improve performance? Wally Meyer deftly balanced his office keys and a large printout of forecasting data as he wheeled his mountain bike...
-
Let V be the volume of a can of radius r and height h, and let S be its surface area (including the top and bottom). Find r and h that minimize S subject to the constraint V = 54.
-
Show that a wrench can be replaced with two perpendicular forces, one of which is applied at a given point.
-
A very popular toy on the market several years ago was the water rocket. Water (at 10C) was loaded into a plastic rocket and pressurized with a hand pump. The rocket was released and would travel a...
-
Statistical distance between records can be measured in several ways. Consider Euclidean distance, measured as the square root of the sum of the squared differences. For the first two records in...
-
Using the data from Exercise 6.18, compute the equivalent units of production for each of the four departments using the FIFO method. In exercise The following data are for four independent...
-
The following data from the just completed year are taken from the accounting records of Mason Company: Sales Direct labor cost $524,000 $70,000 Raw material purchases $118,000 Selling expenses...
-
Harriet's Hats is a retailer who buys hats from a manufacturer and then sells them in its stores. The following information includes the company's December 31, 20Y8 Balance Sheet and the details of...
-
The tangent line to the graph of y=x^(3) at the point (x,y) has slope 3x^(2). Using this result, find the slope of the curve at the point (3,27). 2 answers
-
calculate these rates: 1. Discharges 1000 Incomplete records 610 Delinquent records 450 Incomplete record rate: Delinquent record rate: 2. Discharges 200 Incomplete records 50 Delinquent records 35...
-
Murphy's Paw, Inc. has credit sales of $100,000 for the month ended May 31. The Accounts Receivable balance is $8,000. Management estimates that 1% of its credit sales will be uncollectible. What is...
-
Given the following functions, use function composition to determine if f(x) and g(x) are inverse functions.. f(z) = 1 and g(x)=x+3 (a) (fog)(2) (b) (go f)(x)= (c) Thus g(x) is not the Inverse...
-
George has 50,000 ijn wages, 20,000 in gambling winning,10000 in alimony income and 5000 in dividend income. What is the amount of george income subject to withholding ?
-
Complete this question by entering your answers in the tabs below. Req A Req B and C Record the transactions in the accounting equation for Year 2. Record the amounts of revenue, expense, and...
-
Equal forces are used to stretch to exactly similar wires of Steel and Copper. The sum of their elongations is 1 cm. Find how much each wire is elongated. Given; Y for Steel = 20 x
-
Write a paper by answer the following question: Should Recycling Be Mandatory?
-
Congress enacted the Truth in Lending Act (TILA), [citation], in order to promote the informed use of credit by consumers. [Citation.] To that end, TILAs disclosure provisions seek to ensure...
-
Larry W. Buck (Buck or appellee) sued his former employer, Frank B. Hall & Co. (Hall or appellant), for damages for defamation of character, * * *. By unanimous verdict, a jury found damages for * *...
-
Schreiner, a cotton farmer, agreed over the telephone to sell 150 bales of cotton to Loeb & Co. Schreiner had sold cotton to Loeb & Co. for the past five years. Written confirmation of the date,...
-
Presented below is selected information related to Tsui Repairs at December 31, 2025. Tsui reports financial information monthly (amounts in thousands). a. Determine the total assets of Tsui Repairs...
-
Explain the career opportunities in accounting.
-
Collins Computer Timeshare entered into the following transactions during May 2025. 1. Purchased computers for R\($20,000\) from Digital Equipment on account. 2. Paid R\($4,000\) cash for May rent on...

Study smarter with the SolutionInn App