Question: b) Imagine starting with an empty binary search tree (BST) whose nodes have characters for keys, and adding the letters in the word FACETIOUSLY
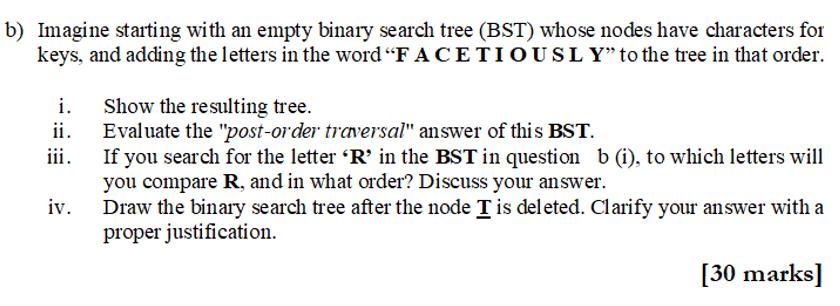
b) Imagine starting with an empty binary search tree (BST) whose nodes have characters for keys, and adding the letters in the word "FACETIOUSLY" to the tree in that order. i. ii. iii. iv. Show the resulting tree. Evaluate the "post-order traversal" answer of this BST. If you search for the letter 'R' in the BST in question b (i), to which letters will you compare R, and in what order? Discuss your answer. Draw the binary search tree after the node T is deleted. Clarify your answer with a proper justification. [30 marks]
Step by Step Solution
There are 3 Steps involved in it
i Resulting Binary Search Tree BST Resulting Binary Search Tree BST F A E Subtree O S Postorder Trav... View full answer

Get step-by-step solutions from verified subject matter experts


