Question: (b) Malware shared code analysis. You are given a dataset of malicious binaries coming from different advanced persistent threat (APT) groups. The task you
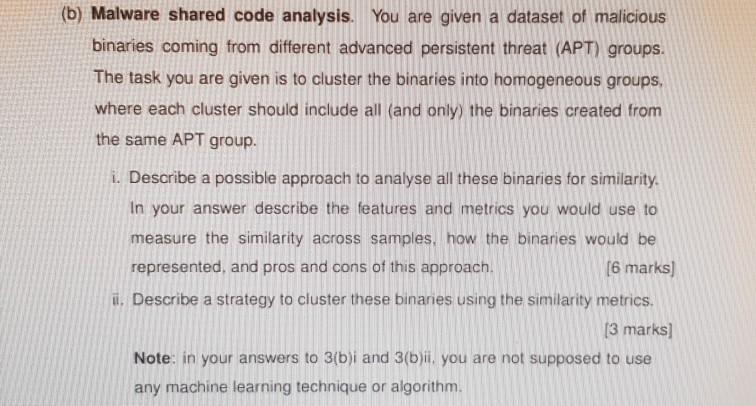
(b) Malware shared code analysis. You are given a dataset of malicious binaries coming from different advanced persistent threat (APT) groups. The task you are given is to cluster the binaries into homogeneous groups, where each cluster should include all (and only) the binaries created from the same APT group. i. Describe a possible approach to analyse all these binaries for similarity. In your answer describe the features and metrics you would use to measure the similarity across samples, how the binaries would be represented, and pros and cons of this approach. (6 marks] i. Describe a strategy to cluster these binaries using the similarity metrics. [3 marks] Note: in your answers to 3(b)i and 3(b)ii. you are not supposed to use any machine learning technique or algorithm.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


