Bonus Activity: The Cookie Jar For this challenge, you'll once again use (cur1), but this time...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
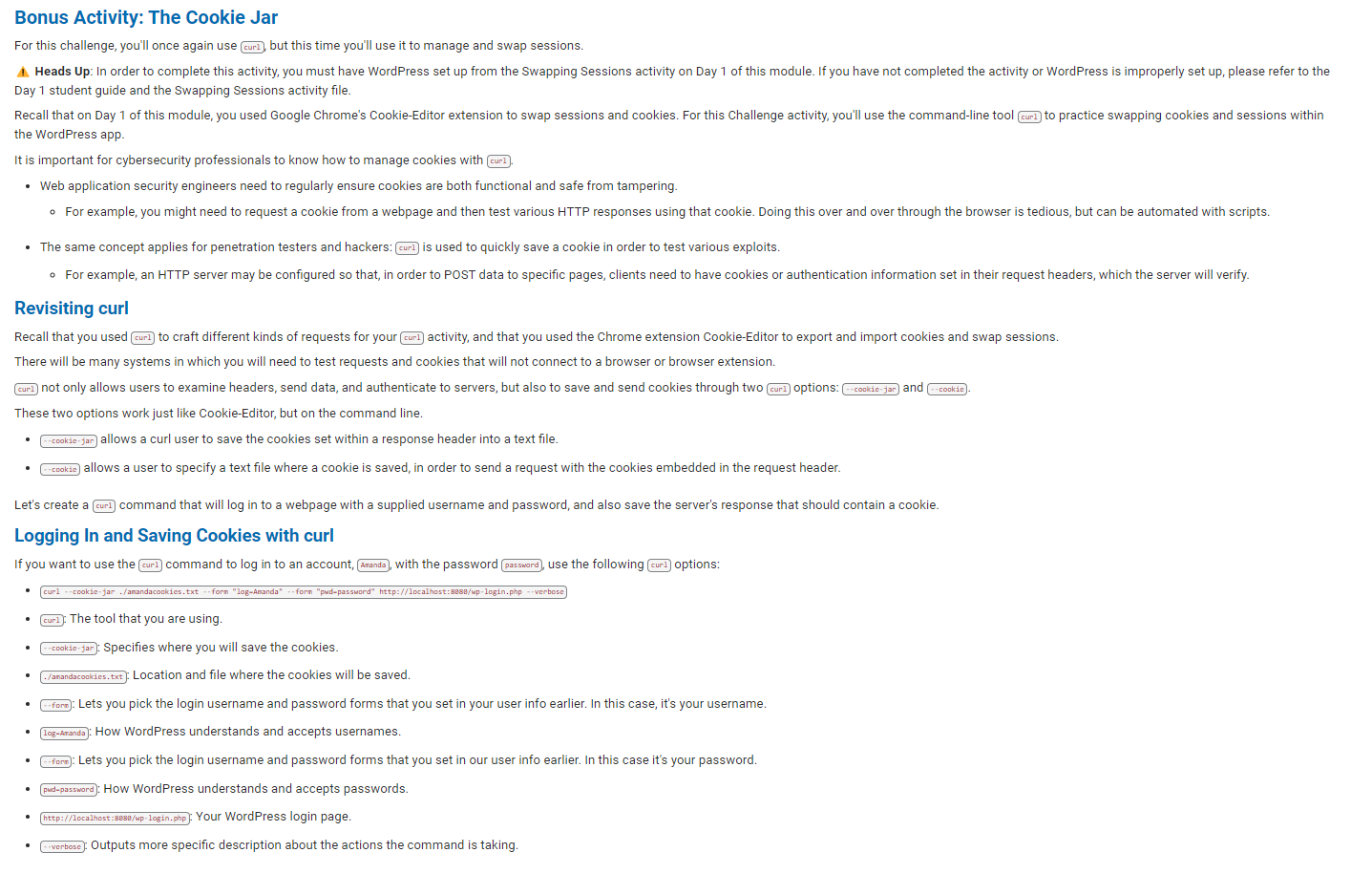
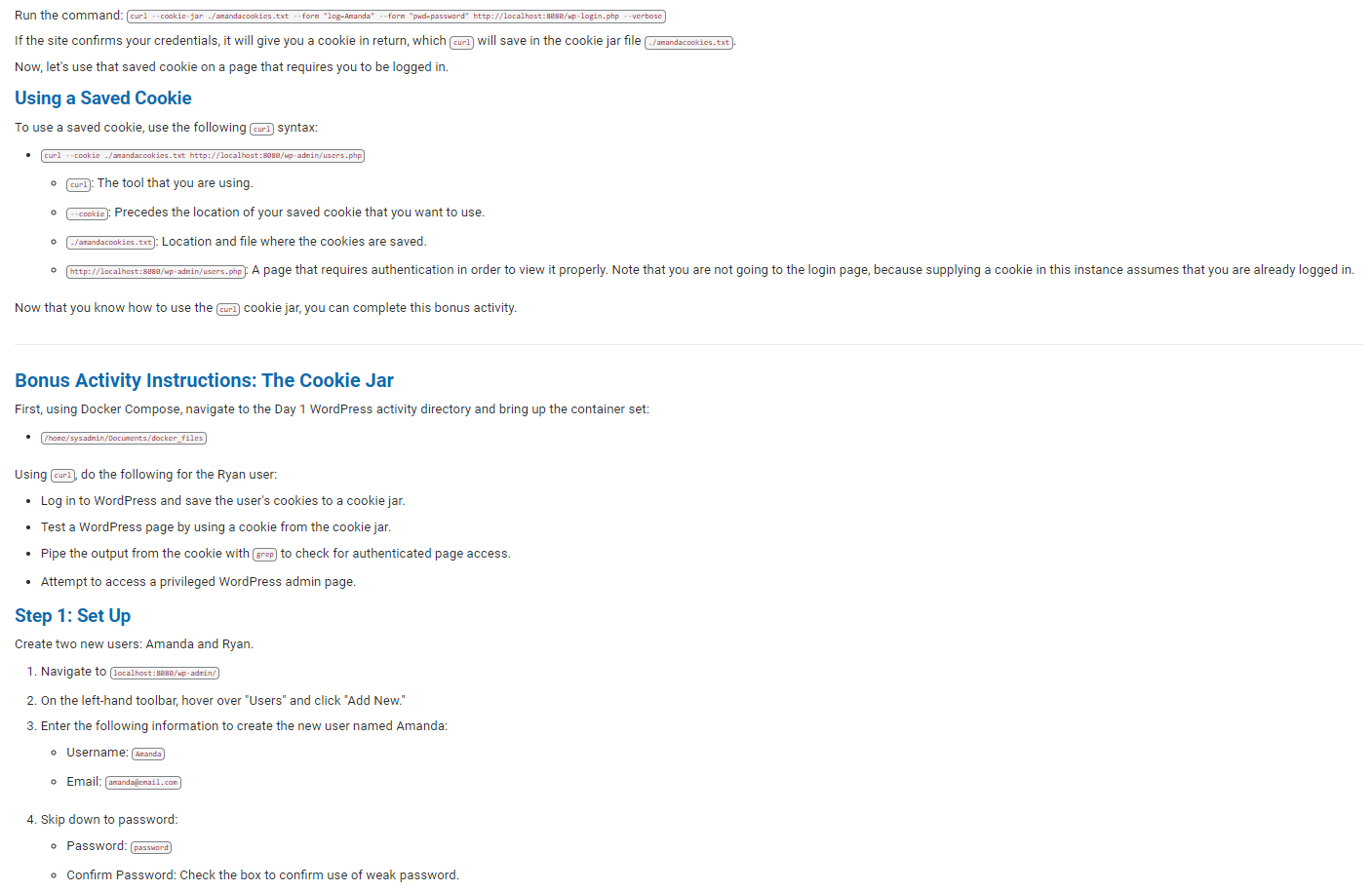
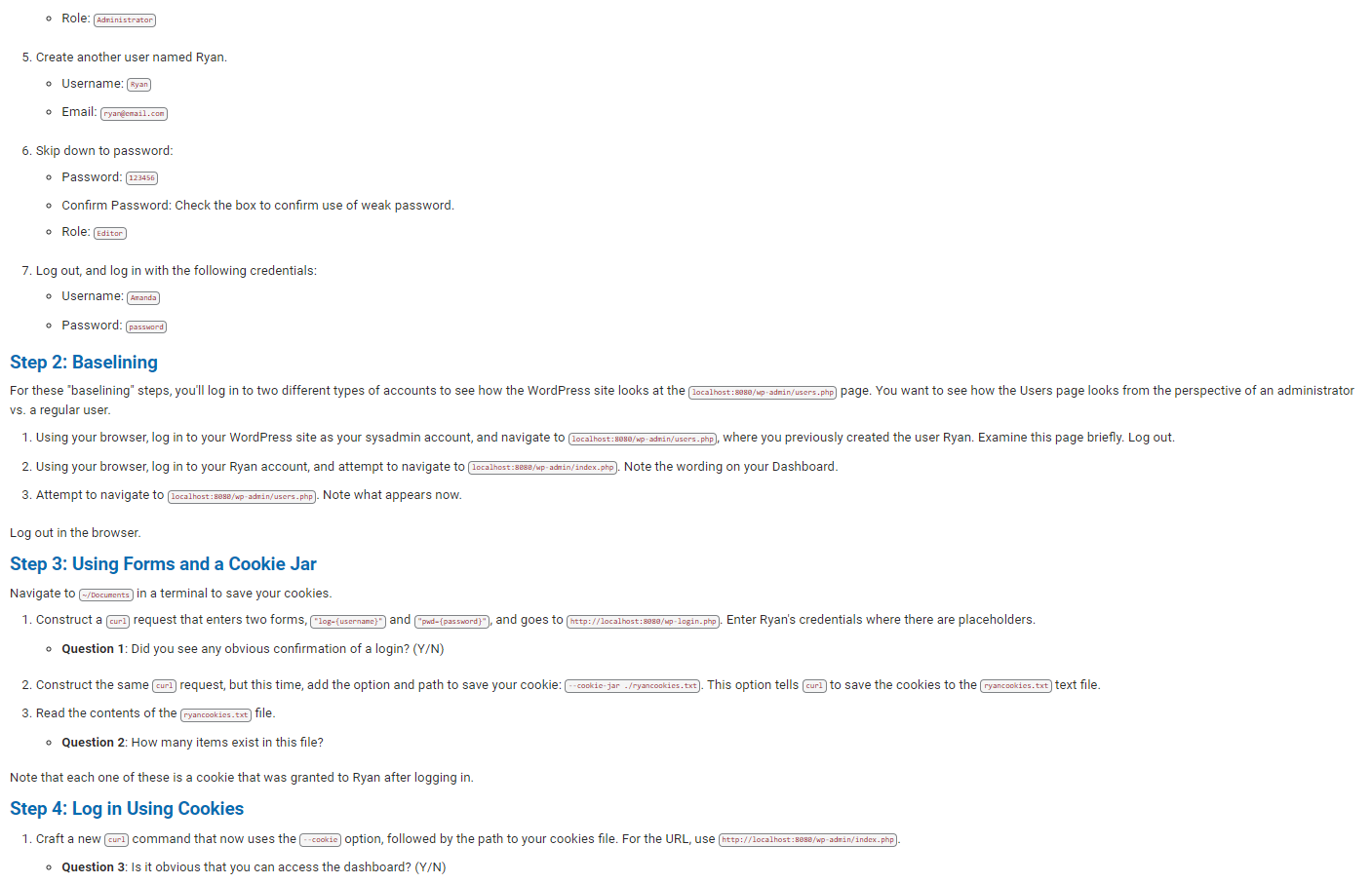
Bonus Activity: The Cookie Jar For this challenge, you'll once again use (cur1), but this time you'll use it to manage and swap sessions. Heads Up: In order to complete this activity, you must have WordPress set up from the Swapping Sessions activity on Day 1 of this module. If you have not completed the activity or WordPress is improperly set up, please refer to the Day 1 student guide and the Swapping Sessions activity file. Recall that on Day 1 of this module, you used Google Chrome's Cookie-Editor extension to swap sessions and cookies. For this Challenge activity, you'll use the command-line tool (curl) to practice swapping cookies and sessions within the WordPress app. It is important for cybersecurity professionals to know how to manage cookies with cur1). Web application security engineers need to regularly ensure cookies are both functional and safe from tampering. For example, you might need to request a cookie from a webpage and then test various HTTP responses using that cookie. Doing this over and over through the browser is tedious, but can be automated with scripts. The same concept applies for penetration testers and hackers: (cur]) is used to quickly save a cookie in order to test various exploits. For example, an HTTP server may be configured so that, in order to POST data to specific pages, clients need to have cookies or authentication information set in their request headers, which the server will verify. Revisiting curl Recall that you used (curl) to craft different kinds of requests for your (cur1) activity, and that you used the Chrome extension Cookie-Editor to export and import cookies and swap sessions. There will be many systems in which you will need to test requests and cookies that will not connect to a browser or browser extension. curl] not only allows users to examine headers, send data, and authenticate to servers, but also to save and send cookies through two cur1) options: -cookie-jar) and --cookie) These two options work just like Cookie-Editor, but on the command line. --cookie-jar) allows a curl user to save the cookies set within a response header into a text file. --cookie) allows a user to specify a text file where a cookie is saved, in order to send a request with the cookies embedded in the request header. Let's create a [cur) command that will log in to a webpage with a supplied username and password, and also save the server's response that should contain a cookie. Logging In and Saving Cookies with curl If you want to use the cur1) command to log in to an account, (Aranda), with the password password), use the following curl] options: curl --cookie-jar ./amandacookies.txt --form "log-Amanda" --form "pwd-password" http://localhost:8888/wp-login.php --verbose . cur1): The tool that you are using. --cookie-jar: Specifies where you will save the cookies. ./anandacookies.txt: Location and file where the cookies will be saved. ---form): Lets you pick the login username and password forms that you set in your user info earlier. In this case, it's your username. log-Aranda): How WordPress understands and accepts usernames. --form): Lets you pick the login username and password forms that you set in our user info earlier. In this case it's your password. pwd-password: How WordPress understands and accepts passwords. http://localhost:8888/wp-login.php): Your WordPress login page. --verbose): Outputs more specific description about the actions the command is taking. Run the command: curl --cookie-jar-/amandacookies.txt -form "log-Amanda" --form "pwd-password" http://localhost:8888/wp-login.php --verbose If the site confirms your credentials, it will give you a cookie in return, which (cur]) will save in the cookie jar file /amandacookies.txt Now, let's use that saved cookie on a page that requires you to be logged in. Using a Saved Cookie To use a saved cookie, use the following curl] syntax: curl cookie./amandacookies.txt http://localhost:8888/up-admin/users.php O (cur1): The tool that you are using. --cookie): Precedes the location of your saved cookie that you want to use. 0 -/arandacookies.txt): Location and file where the cookies are saved. 0 http://localhost:8888/wp-admin/users.php): A page that requires authentication in order to view it properly. Note that you are not going to the login page, because supplying a cookie in this instance assumes that you are already logged in. 0 Now that you know how to use the cur1) cookie jar, you can complete this bonus activity. Bonus Activity Instructions: The Cookie Jar First, using Docker Compose, navigate to the Day 1 WordPress activity directory and bring up the container set: [/home/sysadmin/Documents/docker_files Using curl], do the following for the Ryan user: Log in to WordPress and save the user's cookies to a cookie jar. Test a WordPress page by using a cookie from the cookie jar. Pipe the output from the cookie with grep) to check for authenticated page access. Attempt to access a privileged WordPress admin page. Step 1: Set Up Create two new users: Amanda and Ryan. 1. Navigate to localhost:8888/wp-admin/ 2. On the left-hand toolbar, hover over "Users" and click "Add New." 3. Enter the following information to create the new user named Amanda: Username: Amanda) Email: amanda@email.com 4. Skip down to password: o Password: (password) Confirm Password: Check the box to confirm use of weak password. o Role: Administrator 5. Create another user named Ryan. Username: Ryan o Email: ryan@email.com 6. Skip down to password: o Password: (123456 Confirm Password: Check the box to confirm use of weak password. o Role: [Editor 7. Log out, and log in with the following credentials: Username: Amanda Password: password Step 2: Baselining For these "baselining" steps, you'll log in to two different types of accounts to see how the WordPress site looks at the localhost:8988/up-admin/users.php) page. You want to see how the Users page looks from the perspective of an administrator vs. a regular user. 1. Using your browser, log in to your WordPress site as your sysadmin account, and navigate to localhost:8890/wp-admin/users.php), where you previously created the user Ryan. Examine this page briefly. Log out. 2. Using your browser, log in to your Ryan account, and attempt to navigate to (localhost:8888/wp-admin/index.php). Note the wording on your Dashboard. 3. Attempt to navigate to localhost:8080/wp-admin/users.php). Note what appears now. Log out in the browser. Step 3: Using Forms and a Cookie Jar Navigate to (-/Documents) in a terminal to save your cookies. 1. Construct a (cur) request that enters two forms, "log-{username}") and "pwd-(password)"), and goes to http://localhost:8888/wp-login.php). Enter Ryan's credentials where there are placeholders. Question 1: Did you see any obvious confirmation of a login? (Y/N) 2. Construct the same (cur]) request, but this time, add the option and path to save your cookie: --cookie-jar ./ryancookies.txt). This option tells (curl] to save the cookies to the (ryancookies.txt) text file. 3. Read the contents of the (ryancookies.txt) file. o Question 2: How many items exist in this file? Note that each one of these is a cookie that was granted to Ryan after logging in. Step 4: Log in Using Cookies 1. Craft a new (curl] command that now uses the cookie) option, followed by the path to your cookies file. For the URL, use (http://localhost:8888/wp-admin/index.php Question 3: Is it obvious that you can access the dashboard? (Y/N) Question 3: Is it obvious that you can access the dashboard? (Y/N) 2. Press the up arrow on your keyboard to run the same command, but this time, pipe | grep Dashboard) to the end of your command to return all instances of the word (Dashboard) on the page. Question 4: Look through the output where (Dashboard) is highlighted. Does any of the wording on this page seem familiar? (Y/N) If so, you should be successfully logged in to your Editor's dashboard. Step 5: Test the Users.php Page 1. Finally, write a (cur]) command using the same --cookie ryancookies.txt) option, but attempt to access (http://localhost:8888/wp-admin/users.php Question 5: What happens this time? Submission Guidelines After you complete your Submission File, title it with the following format: < YOUR NAME > < Web Development Challenge > Make sure to set the file permissions so that anyone can view and comment on your document. Submit the URL of your Submission File Google Doc through Canvas. Bonus Activity: The Cookie Jar Question 1: Did you see any obvious confirmation of a login? (Y/N) [Enter answer here] Question 2: How many items exist in this file? [Enter answer here] Question 3: Is it obvious that you can access the dashboard? (Y/N) [Enter answer here] Question 4: Look through the output where Dashboard is highlighted. Does any of the wording on this page seem familiar? (Y/N) If so, you should be successfully logged in to your Editor's dashboard. [Enter answer here] Question 5: What happens this time? [Enter answer here] Bonus Activity: The Cookie Jar For this challenge, you'll once again use (cur1), but this time you'll use it to manage and swap sessions. Heads Up: In order to complete this activity, you must have WordPress set up from the Swapping Sessions activity on Day 1 of this module. If you have not completed the activity or WordPress is improperly set up, please refer to the Day 1 student guide and the Swapping Sessions activity file. Recall that on Day 1 of this module, you used Google Chrome's Cookie-Editor extension to swap sessions and cookies. For this Challenge activity, you'll use the command-line tool (curl) to practice swapping cookies and sessions within the WordPress app. It is important for cybersecurity professionals to know how to manage cookies with cur1). Web application security engineers need to regularly ensure cookies are both functional and safe from tampering. For example, you might need to request a cookie from a webpage and then test various HTTP responses using that cookie. Doing this over and over through the browser is tedious, but can be automated with scripts. The same concept applies for penetration testers and hackers: (cur]) is used to quickly save a cookie in order to test various exploits. For example, an HTTP server may be configured so that, in order to POST data to specific pages, clients need to have cookies or authentication information set in their request headers, which the server will verify. Revisiting curl Recall that you used (curl) to craft different kinds of requests for your (cur1) activity, and that you used the Chrome extension Cookie-Editor to export and import cookies and swap sessions. There will be many systems in which you will need to test requests and cookies that will not connect to a browser or browser extension. curl] not only allows users to examine headers, send data, and authenticate to servers, but also to save and send cookies through two cur1) options: -cookie-jar) and --cookie) These two options work just like Cookie-Editor, but on the command line. --cookie-jar) allows a curl user to save the cookies set within a response header into a text file. --cookie) allows a user to specify a text file where a cookie is saved, in order to send a request with the cookies embedded in the request header. Let's create a [cur) command that will log in to a webpage with a supplied username and password, and also save the server's response that should contain a cookie. Logging In and Saving Cookies with curl If you want to use the cur1) command to log in to an account, (Aranda), with the password password), use the following curl] options: curl --cookie-jar ./amandacookies.txt --form "log-Amanda" --form "pwd-password" http://localhost:8888/wp-login.php --verbose . cur1): The tool that you are using. --cookie-jar: Specifies where you will save the cookies. ./anandacookies.txt: Location and file where the cookies will be saved. ---form): Lets you pick the login username and password forms that you set in your user info earlier. In this case, it's your username. log-Aranda): How WordPress understands and accepts usernames. --form): Lets you pick the login username and password forms that you set in our user info earlier. In this case it's your password. pwd-password: How WordPress understands and accepts passwords. http://localhost:8888/wp-login.php): Your WordPress login page. --verbose): Outputs more specific description about the actions the command is taking. Run the command: curl --cookie-jar-/amandacookies.txt -form "log-Amanda" --form "pwd-password" http://localhost:8888/wp-login.php --verbose If the site confirms your credentials, it will give you a cookie in return, which (cur]) will save in the cookie jar file /amandacookies.txt Now, let's use that saved cookie on a page that requires you to be logged in. Using a Saved Cookie To use a saved cookie, use the following curl] syntax: curl cookie./amandacookies.txt http://localhost:8888/up-admin/users.php O (cur1): The tool that you are using. --cookie): Precedes the location of your saved cookie that you want to use. 0 -/arandacookies.txt): Location and file where the cookies are saved. 0 http://localhost:8888/wp-admin/users.php): A page that requires authentication in order to view it properly. Note that you are not going to the login page, because supplying a cookie in this instance assumes that you are already logged in. 0 Now that you know how to use the cur1) cookie jar, you can complete this bonus activity. Bonus Activity Instructions: The Cookie Jar First, using Docker Compose, navigate to the Day 1 WordPress activity directory and bring up the container set: [/home/sysadmin/Documents/docker_files Using curl], do the following for the Ryan user: Log in to WordPress and save the user's cookies to a cookie jar. Test a WordPress page by using a cookie from the cookie jar. Pipe the output from the cookie with grep) to check for authenticated page access. Attempt to access a privileged WordPress admin page. Step 1: Set Up Create two new users: Amanda and Ryan. 1. Navigate to localhost:8888/wp-admin/ 2. On the left-hand toolbar, hover over "Users" and click "Add New." 3. Enter the following information to create the new user named Amanda: Username: Amanda) Email: amanda@email.com 4. Skip down to password: o Password: (password) Confirm Password: Check the box to confirm use of weak password. o Role: Administrator 5. Create another user named Ryan. Username: Ryan o Email: ryan@email.com 6. Skip down to password: o Password: (123456 Confirm Password: Check the box to confirm use of weak password. o Role: [Editor 7. Log out, and log in with the following credentials: Username: Amanda Password: password Step 2: Baselining For these "baselining" steps, you'll log in to two different types of accounts to see how the WordPress site looks at the localhost:8988/up-admin/users.php) page. You want to see how the Users page looks from the perspective of an administrator vs. a regular user. 1. Using your browser, log in to your WordPress site as your sysadmin account, and navigate to localhost:8890/wp-admin/users.php), where you previously created the user Ryan. Examine this page briefly. Log out. 2. Using your browser, log in to your Ryan account, and attempt to navigate to (localhost:8888/wp-admin/index.php). Note the wording on your Dashboard. 3. Attempt to navigate to localhost:8080/wp-admin/users.php). Note what appears now. Log out in the browser. Step 3: Using Forms and a Cookie Jar Navigate to (-/Documents) in a terminal to save your cookies. 1. Construct a (cur) request that enters two forms, "log-{username}") and "pwd-(password)"), and goes to http://localhost:8888/wp-login.php). Enter Ryan's credentials where there are placeholders. Question 1: Did you see any obvious confirmation of a login? (Y/N) 2. Construct the same (cur]) request, but this time, add the option and path to save your cookie: --cookie-jar ./ryancookies.txt). This option tells (curl] to save the cookies to the (ryancookies.txt) text file. 3. Read the contents of the (ryancookies.txt) file. o Question 2: How many items exist in this file? Note that each one of these is a cookie that was granted to Ryan after logging in. Step 4: Log in Using Cookies 1. Craft a new (curl] command that now uses the cookie) option, followed by the path to your cookies file. For the URL, use (http://localhost:8888/wp-admin/index.php Question 3: Is it obvious that you can access the dashboard? (Y/N) Question 3: Is it obvious that you can access the dashboard? (Y/N) 2. Press the up arrow on your keyboard to run the same command, but this time, pipe | grep Dashboard) to the end of your command to return all instances of the word (Dashboard) on the page. Question 4: Look through the output where (Dashboard) is highlighted. Does any of the wording on this page seem familiar? (Y/N) If so, you should be successfully logged in to your Editor's dashboard. Step 5: Test the Users.php Page 1. Finally, write a (cur]) command using the same --cookie ryancookies.txt) option, but attempt to access (http://localhost:8888/wp-admin/users.php Question 5: What happens this time? Submission Guidelines After you complete your Submission File, title it with the following format: < YOUR NAME > < Web Development Challenge > Make sure to set the file permissions so that anyone can view and comment on your document. Submit the URL of your Submission File Google Doc through Canvas. Bonus Activity: The Cookie Jar Question 1: Did you see any obvious confirmation of a login? (Y/N) [Enter answer here] Question 2: How many items exist in this file? [Enter answer here] Question 3: Is it obvious that you can access the dashboard? (Y/N) [Enter answer here] Question 4: Look through the output where Dashboard is highlighted. Does any of the wording on this page seem familiar? (Y/N) If so, you should be successfully logged in to your Editor's dashboard. [Enter answer here] Question 5: What happens this time? [Enter answer here]
Expert Answer:
Answer rating: 100% (QA)
It seems youve shared images from an exercise or a tutorial related to cybersecurity specifically managing cookies and session management using curl i... View the full answer

Related Book For 

Accounting Information Systems basic concepts and current issues
ISBN: 978-0078025334
3rd edition
Authors: Robert Hurt
Posted Date:
Students also viewed these computer network questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
Suppose that there are two countries, A and B, and two goods, X and Y. Country A has a production possibility frontier (PPF) that is given by the equation X + Y = 100, while country B has a PPF that...
-
The following list contains events that occurred during January 2019 at the local Ford dealer, Malcom Motors: a. California Central University (CCU) signed a contract to purchase a fleet of Ford...
-
1. Create a time-phased assembly chart to determine when the 10 cars can be delivered. 2. What adjustments are needed in inventory levels, lead times, and batch sizes to fill an additional customer...
-
What are some of the disadvantages of using social media?
-
Presented below is information related to Meghani Company. Instructions Compute the ending inventory for Meghani Company for 2013 through 2018 using the dollar-value LIFOmethod. Ending Inventory...
-
Cameron Cookiest produces gourmet cookies, which sell for $16 a basket. Variable costs per basket are $6 and fixed costs are $5,000 per month. If the company expects to sell 1,500 baskets of cookies,...
-
Comparative balance sheets for 2024 and 2023 and a statement of income for 2024 are given below for Metagrobolize Industries. Additional information from the accounting records of Metagrobolize also...
-
Explain, using appropriate terminologies and a FLOW CHART, how expansionary monetary policy can affect the economy. (Draw the flow chart)
-
How does international pension work? what issues need further research when it comes to international pension? Example of international country that use pension?
-
What concerns about project implementation could impact the learning and development of human resources? Explain
-
A hospital has identified nonrandom variations in medical errors. These errors are directly related to patient falls. Draw a flow chart showing under what circumstances a patient might fall. Assume...
-
Look at agencies that offer hope on the various world problems that have been tackled. This is how we consider interventions, as implied by the course title. Find an agency that is battling a problem...
-
As healthcare has evolved so has the concept of a patient or consumer of healthcare. Technology and culture are among the many variables that have affected our concept of a healthcare patient....
-
Find an estimate for yo such that the solution to the initial value problem is guaranteed to satisfy the given inequality. 24. * = xy + arctan(y), y(1) = yo > 1. y(3) < 5. 25. = y? + xy+x + y, y(0) =...
-
Tiger, Inc. signed a lease for equipment on July 1, 2007.The lease is for 10 years (the useful life of the asset).The first of 10 equal annual payments of $500,000 was made on July 1, 2007.The...
-
a. Consider the five generic elements of most accounting information systems. For each element, suggest one way it could be compromised via computer crime. b. Read Protect Small Business by Joseph T....
-
Choose one of the Fortune 100 companies; investigate it on the Internet and through your universitys library. Work with a group of students to prepare a PowerPoint presentation to fulfill the first...
-
Multiple choice questions. 1. A company that reproduces fine works of art, such as the Mona Lisa, would most likely use what kind of production process? a. Hybrid b. Conversion c. Job d. Process 2. A...
-
Assume the same facts as in Problem 42. Further assume that next year, Gary sells the SUV for $20,000. a. How much depreciation expense can Gary deduct as a business deduction with respect to the SUV...
-
Describe how liabilities are reported and analyzed.
-
Assume the same facts as in Problem 29, except that Sally has AGI of \($75,000.\) What is her qualified student loan interest deduction in 2019? Problem 29, In 2019, Sally Morris, a single taxpayer,...

Study smarter with the SolutionInn App