Question: C. Spoofing o d. Elevation of privileges QUESTION 2 Modification of a file that is owned by another user is an example of which component
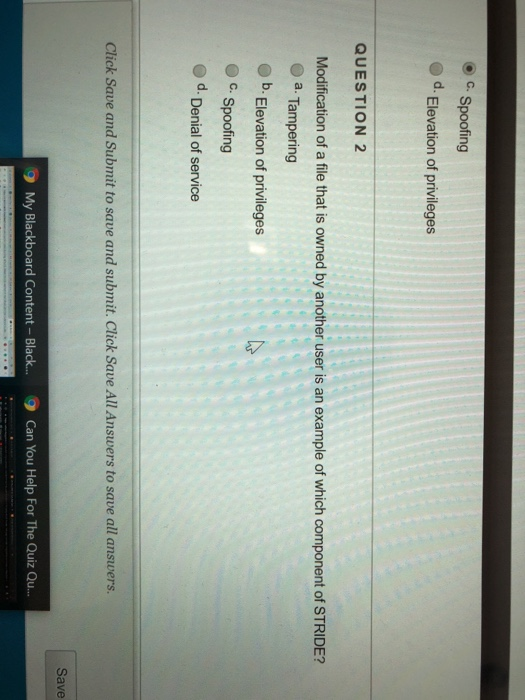
C. Spoofing o d. Elevation of privileges QUESTION 2 Modification of a file that is owned by another user is an example of which component of STRIDE? a. Tampering b. Elevation of privileges c. Spoofing d. Denial of service Click Save and Submit to save and submit. Click Save All Answers to save all answers. Save 9 My Blackboard Content- Black... Can You Help For The Quiz Qu
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


