Question: Caesar Cipher is an encryption technique. It is a type of substitution cipher in which each letter in the plaintext is replaced by a
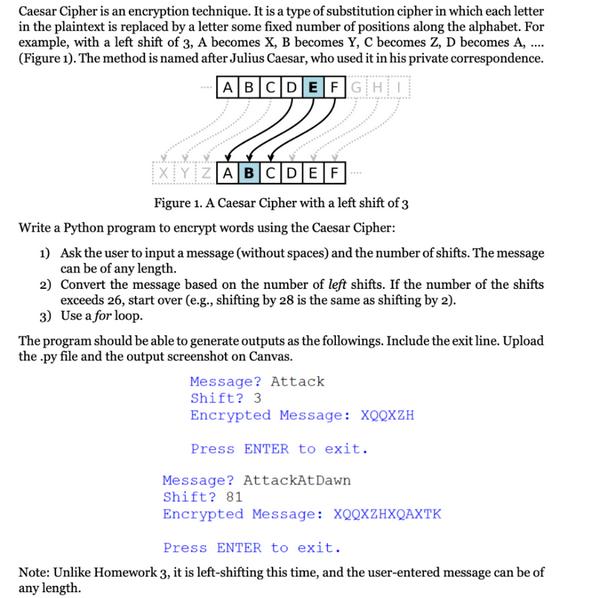
Caesar Cipher is an encryption technique. It is a type of substitution cipher in which each letter in the plaintext is replaced by a letter some fixed number of positions along the alphabet. For example, with a left shift of 3, A becomes X, B becomes Y, C becomes Z, D becomes A, .... (Figure 1). The method is named after Julius Caesar, who used it in his private correspondence. ABCDEFGHI XYZABCDEF Figure 1. A Caesar Cipher with a left shift of 3 Write a Python program to encrypt words using the Caesar Cipher: 1) Ask the user to input a message (without spaces) and the number of shifts. The message can be of any length. 2) Convert the message based on the number of left shifts. If the number of the shifts exceeds 26, start over (e.g., shifting by 28 is the same as shifting by 2). 3) Use a for loop. The program should be able to generate outputs as the followings. Include the exit line. Upload the .py file and the output screenshot on Canvas. Message? Attack Shift? 3 Encrypted Message: XQQXZH Press ENTER to exit. Message? AttackAt Dawn Shift? 81 Encrypted Message: XQQXZHXQAXTK Press ENTER to exit.. Note: Unlike Homework 3, it is left-shifting this time, and the user-entered message can be of any length.
Step by Step Solution
There are 3 Steps involved in it
Here is an example Python program to encrypt words using the Caesar Cipher technique with left shif... View full answer

Get step-by-step solutions from verified subject matter experts


