Question: can someone help to answer 3 questions please. Styles Without period With period Without period With period def0879f7513179a64508f10357aa896 7bef8ce365e2ae6696b0e02de7df4f90 84e1783794b6299495b3398c2e008004b421b2b8 47aed104deof93ce24c8bede0016eda422a71782 e0442beld03ae00f840abac89ffe19bc6f55c340052c172449b3bc73e b82063e ae0e453c11d35fa6d67a63fd793a353d3d67350a8e1630bc7cDe3659 8b1516b2
can someone help to answer 3 questions please.
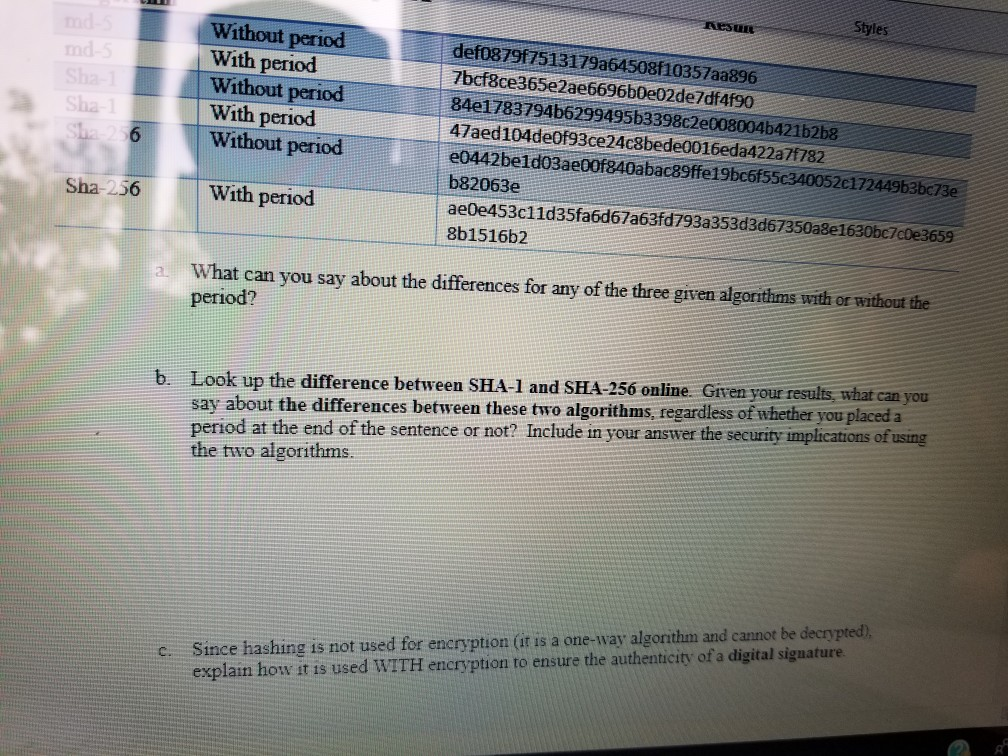
Styles Without period With period Without period With period def0879f7513179a64508f10357aa896 7bef8ce365e2ae6696b0e02de7df4f90 84e1783794b6299495b3398c2e008004b421b2b8 47aed104deof93ce24c8bede0016eda422a71782 e0442beld03ae00f840abac89ffe19bc6f55c340052c172449b3bc73e b82063e ae0e453c11d35fa6d67a63fd793a353d3d67350a8e1630bc7cDe3659 8b1516b2 Sha 6 Without period Sha-256 With period a. What can you say about the differences for any of the three given algorithms with or without the period? b. Look up the difference between SHA-1 and SHA-256 online. Given your results what can you say about the differences between these two algorithms, regardless of whether you placed period at the end of the sentence or not? include in you ansiwer the security implications of using the two algorithms. c. Since hashing is not used for encryption (it is a one-way algorithm and cannot be decrypted) explain how it is used WITH encryption to ensure the authenticity of a digital sigaature
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


