Question: Carry out the determination sort work that involves find Min and trade capacities as examined in address Include a capacity called by primary to execute
Carry out the determination sort work that involves find Min and trade capacities as examined in address Include a capacity called by primary to execute the paired inquiry The arranged exhibit delivered by the sort capacity ought to be passed to the pursuit routine which returns the area in the arranged cluster of the looked for esteem, or - 1 on the off chance that the worth s not in the cluster Add a worth returning capacity that figures the middle of your informational collection. (f.e. principal capacity will show the middle) - Use show Array capacity to show components of the exhibit prior to arranging and in the wake of arranging as expected in the program yield. The capacity ought to show the cluster esteems pleasantly formatted columns Your program ought to yield The absolute number of components read from the document (substantial things in the exhibit) The exhibit as perused from the record The arranged exhibit The number being looked for and the area of that number in the arranged cluster (or an- - - suitable message on the off chance that it isn't in the exhibit)Hitesh Sheth, President and CEO at Vectra, a San Jose, Calif.- based supplier of innovation which applies AI to identify and chase after digital aggressors, makes sense of, "Public utilities, including power and water frameworks, have been prime cyberattack focuses for a really long time. There's an entire Russian digital group, "Vivacious Bear," zeroed in on hacking American energy framework. In the Oldsmar case it's untimely to allocate thought process or spot fault. Notwithstanding, we've seen an adequate number of breaks of the US power framework, water frameworks, and, surprisingly, atomic plants to finish up this: safeguarding these basic offices, and redesigning their digital guards, ought to be a far higher need."
Heather Paunet, Senior Vice President at Untangle, a San Jose, Calif.- based supplier of complete organization security for SMBs, says, "As we start 2021, legislatures, as well as each and every kind of business, keep on having their representatives work from a distance. As IT offices responded rapidly in 2020 to empower every one of their representatives to telecommute, guaranteeing a safe workfrom-home climate took a piece longer to get right. As representatives progressed to remote work, they put their work gadgets onto their home organizations, which wouldn't have every one of the protections set up as their in-office network had."
Paunet adds, "This can set out open doors for agitators to hack into networks and possibly create perilous circumstances. For the situation with Oldsmar's water treatment plant, it was found that somebody approached their PC framework from a distance. With remote access being significantly more typical because of less on-premises laborers, this might not have been seen as fast as it ought to have been. While contemplating remote access, business, everything being equal, and all ventures ought to consider:
Utilization of VPN innovations: give a solid passage, and certifications that are given to representatives to get to inward assets and keep basic frameworks secured.
Legitimate onboarding and offboarding: as workers join and leave an organization, it is vital to guarantee that entrance is possibly given if necessary, and renounced promptly as representatives leave.
Isolation of organization access: guarantee that representatives are just given admittance to the frameworks that they need. Putting various frameworks on various organizations that are just open by the gatherings of workers that need them is critical to guarantee that in the event that a break occurs, less frameworks can be compromised.
Devoted work gadgets: during times, for example, the quick shift to telecommuting in 2020, where numerous representatives wound up getting to frameworks from a distance, giving a committed gadget to workers as opposed to permitting workers to get to the corporate organization from their own gadgets will give IT divisions the most control of their foundation.
Consistent worker preparing: showing representatives how to perceive phishing messages, is similarly basically as significant as setting up defensive frameworks. As security foes track down better approaches to penetrate networks, staying up with the latest will just fortify your organization security.
document should be search.cpp Wre a program that will peruse information from a record. The program will permit the client to determine the filename. Utilize a circle that will check assuming the document is opened accurately, in any case show a mistake message and permit the client to reappear a filename until effective. Peruse the qualities from the record and store into a whole number cluster. The program ought to then provoke the client for a whole number which will be looked for in the cluster utilizing parallel pursuit. Make a point to incorporate the accompanying A sort work should be called before the parallel pursuit.
If it's not too much trouble, read the issue and adhere to the guidance in main.cpp for this program.
Issue: - Plan a theoretical class called Shape: - Private factors twofold x and y, this is x and y position in postscript document - Constructor shape (x, y) that dole out x and y values - work region take no boundaries return twofold const equivalent zero, unadulterated virtual capacity - work draw take ostream document return void and equivalent zero, unadulterated virtual capacity - make take apart ~Shape - Here's a clue: you really want to utilize virtual - Configuration class Circle that acquire class shape capacities - private variable x, y, sweep - Make the accompanying capacities: - Circle constructor that take x, y, sweep, Note that x and y are doled out to Shape(x,y) - for instance constructor_name(double x, twofold y) : Shape(x,y) - draw that take ostream document to compose postscript guidance the capacity bring void back - region take no boundaries and return twofold region of the circle - ~Circle deconstruction - Configuration class Rect that acquire class shape with same capacities as class Circle - private factors are x, y, weight, level - Configuration class FilledRect that acquire class shape with same capacities as class Circle - private factors are x, y, weight, level - Hint for Circle, Rect, and FilledRect: you should utilize supersede catchphrase - e.g.: data_return_type function_name(inputs) override {} - Configuration class Drawing that take all shapes made and save it in vectors. Then use draw work for each Shape to compose test.ps record with postscripts guidelines - it has private factors of type: ofstream and vector - Drawing constructor that take area to open and make new "test.ps" document and compose postscript line in it - void add work that push_back new shapes to vector. It takes "Polymorphism" shape - void draw work take no boundary that circle through all shapes and compose postscript guidance for each shape - void show Area take no boundaries and circle inside vector to run region work for each shape class - void setrgb work take three twofold for red, green, and blue. It composes postscript to change the variety for all shapes - All postscript line to draw shapes are given in main.cpp comments
## Postscript language Actually look at Wiki. for some foundation about Postscript (https://en.wikipedia.org/wiki/PostScript) You can utilize online site to see .ps document (https://products.aspose.app/page/watcher/ps) Postscript line you really want to use to draw shapes are given in the code.
Carry out the determination sort work that involves find Min and trade capacities as examined in address Include a capacity called by primary to execute the paired inquiry The arranged exhibit delivered by the sort capacity ought to be passed to the pursuit routine which returns the area in the arranged cluster of the looked for esteem, or - 1 on the off chance that the worth s not in the cluster Add a worth returning capacity that figures the middle of your informational collection. (f.e. principal capacity will show the middle) - Use show Array capacity to show components of the exhibit prior to arranging and in the wake of arranging as expected in the program yield. The capacity ought to show the cluster esteems pleasantly formatted columns Your program ought to yield The absolute number of components read from the document (substantial things in the exhibit) The exhibit as perused from the record The arranged exhibit The number being looked for and the area of that number in the arranged cluster (or an- - - suitable message on the off chance that it isn't in the exhibit) - The middle of the informational index Assume that the most extreme number of values in the information record wll not surpass 50. Test input record: data.dat
Kindly use C++ for this program.
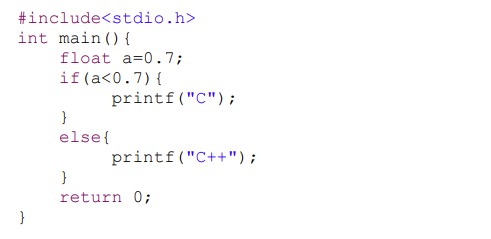
#include int main() { float a=0.7%; if (a
Step by Step Solution
There are 3 Steps involved in it
To implement the provided requirements in C we will need to follow the instructions provided and develop the necessary functions and classes Below is ... View full answer

Get step-by-step solutions from verified subject matter experts


