Question: Case Lab Content Using sockats OS module and file permissions Solve the case Setting the Stage for Your First Python Program: The Cuckoo's Egg A
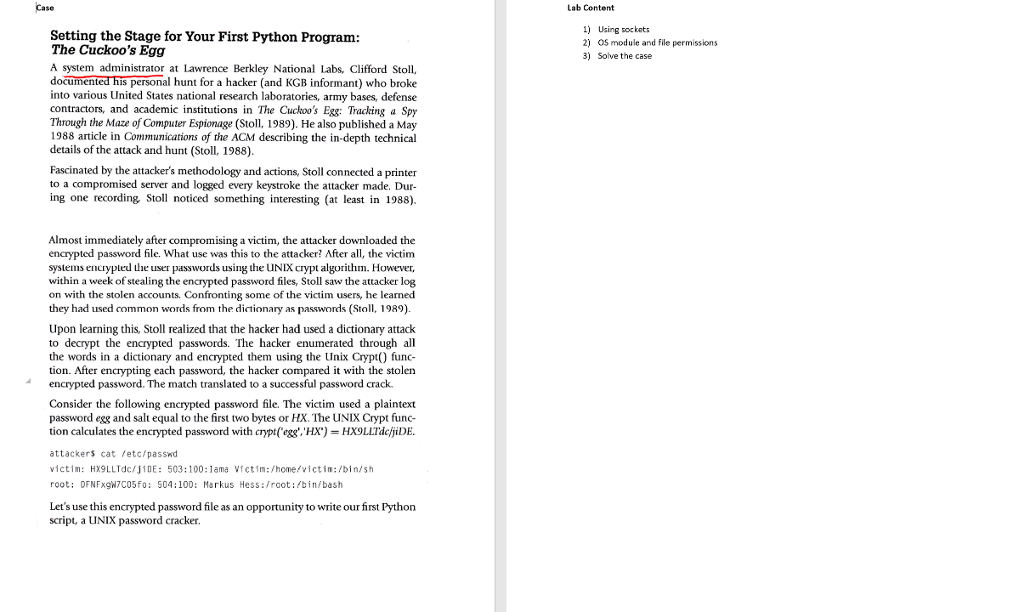
Case Lab Content Using sockats OS module and file permissions Solve the case Setting the Stage for Your First Python Program: The Cuckoo's Egg A system administrator at Lawrence Berkley National Labs, Clifford Stoll, docu into various United States national research laboratories, army bases, defense contractors, and academic institutions in The Cuckoo's Eg&: Tracking a Spy Through the Maze of Computer Espionage (Stoll, 1989). He also published a May 1988 article in Communications of the ACM describing the in-depth technical details of the attack and hunt (Stol, 1988) 2) 3) is personal hunt for a hacker (and KGB informant) who broke Fascinated by the attacker's methodology and actions, Stoll connected a printer to a compromised server and logged every keystroke the attacker made. Dur ing one recording Stoll noticed something interesting (at least in 1988). Almost immediately after compromising a victim, the attacker downloaded the encrypted password file. What use was this to the attacker? After all, the victim systems encrypted user passwords using the UNIX crypt algorithm. However, within a week of stealing the encrypted password files, Stoll saw the attacker log on with the stolen accounts. Confronting some of the victim users, he learned they had used common words from the dictionary as passwords (Stoll, 1989) Upon learning this, Stoll realized that the hacker had used a dictionary attack to decrypt the encrypted passwords. The hacker enumerated through all the words in a dictionary and encrypted them using the Unix Crypt) func tion. After encrypting each password, the hacker compared it with the stolen encrypted password. "The match translated to a successful password crack. Consider the following encrypted password file. The victim used a plaintext password egg and salt equal to the first two bytes or HX. The UNIX Crypt func tion calculates the encrypted password with crypt(egg'.'HX) HX9LLTdcfjiDE attackers cat fetc/passwd victin: HX9LLTdc/IDE: 503:100:1ama Vctim:/home/victim:/bin/sh root: DFNFxgN7C05fo: 504:100: Merkus Hess:/root:/bin bash Let's use this encrypted password file as an opportunity to write our first Python script, a UNIX password cracker
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


