Question: Choose a different technique than command and scripting. It can be any of the techniques that are listed, but it cannot be command and scripting.
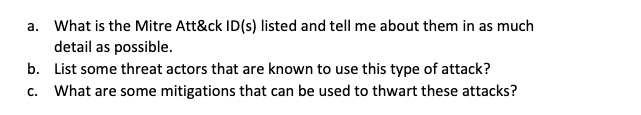
Choose a different technique than command and scripting. It can be any of the techniques that are listed, but it cannot be command and scripting. Answer the questions that are attached on the technique that you choose.
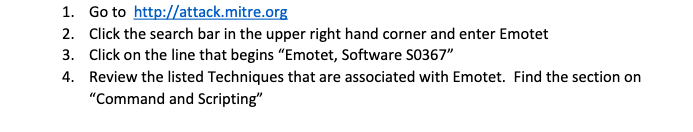
1. Go to http://attack.mitre.org 2. Click the search bar in the upper right hand corner and enter Emotet 3. Click on the line that begins "Emotet, Software S0367" 4. Review the listed Techniques that are associated with Emotet. Find the section on "Command and Scripting" a. What is the Mitre Att\&ck ID(s) listed and tell me about them in as much detail as possible. b. List some threat actors that are known to use this type of attack? c. What are some mitigations that can be used to thwart these attacks? 5. Choose a different technique from the list and answer the same questions from above on this technique
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


