Question: Cisco Firewall Rule Case Study' 1. Case Learning Objectives Explain why it is important to configure firewall effectively Create Cisco firewall rules to satisfy
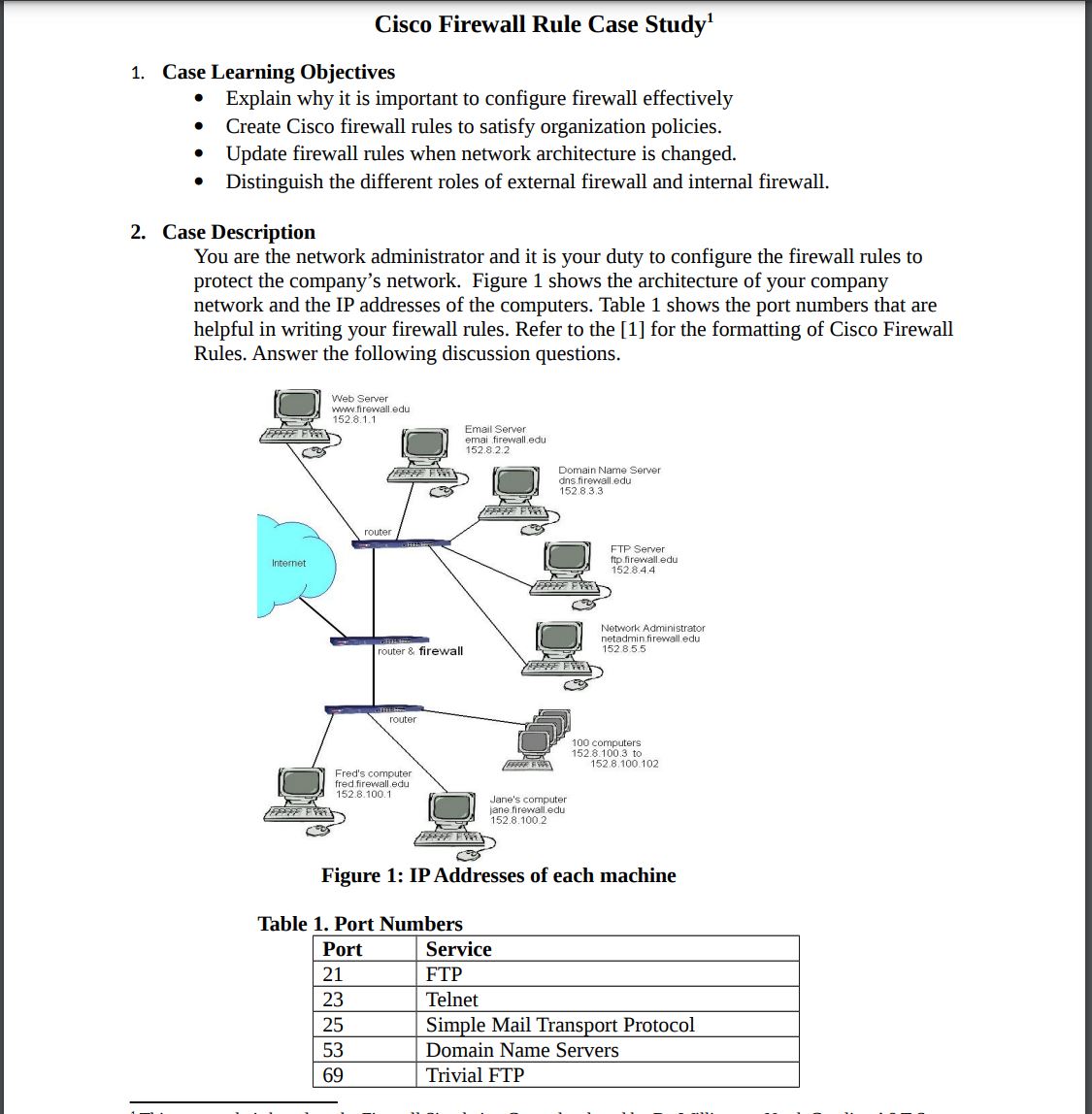
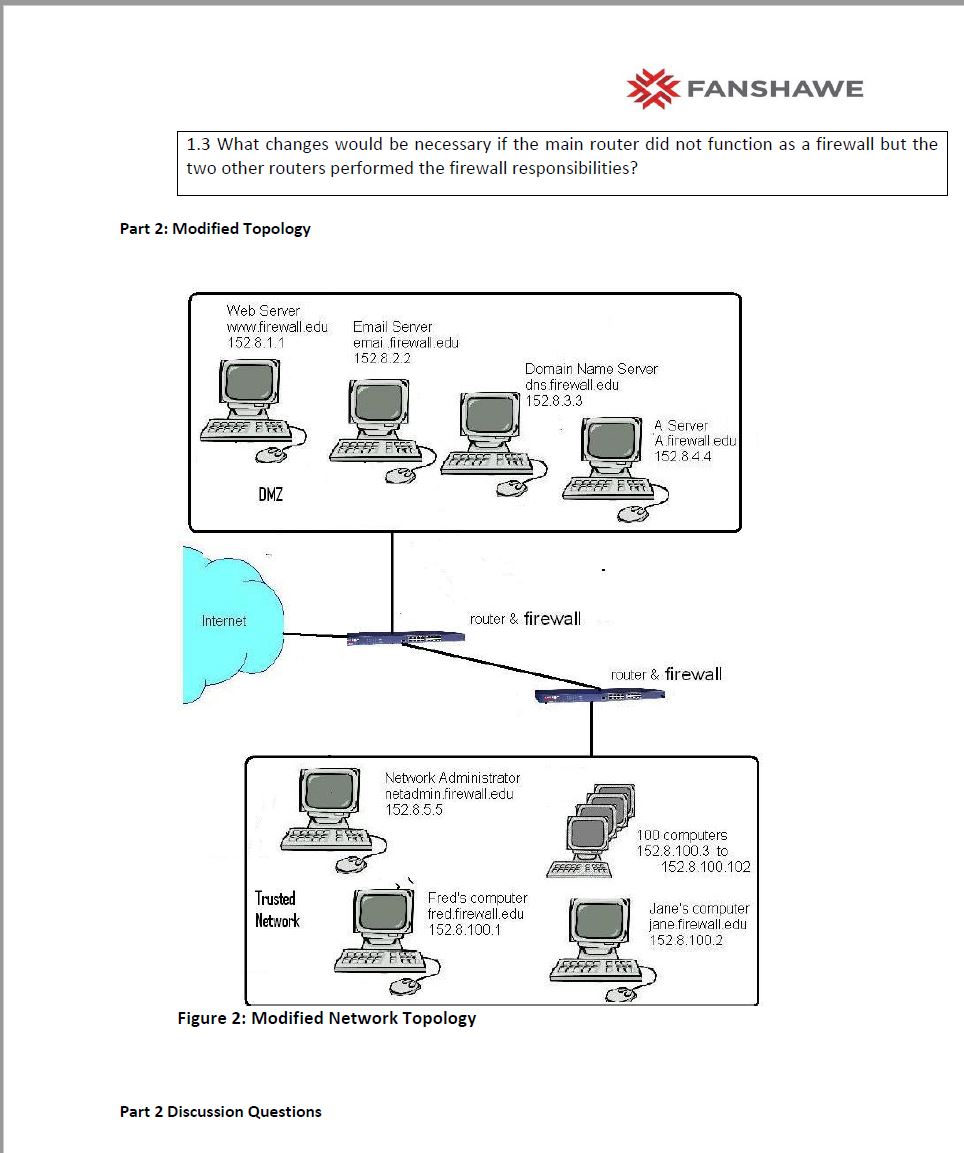
Cisco Firewall Rule Case Study' 1. Case Learning Objectives Explain why it is important to configure firewall effectively Create Cisco firewall rules to satisfy organization policies. Update firewall rules when network architecture is changed. Distinguish the different roles of external firewall and internal firewall. 2. Case Description You are the network administrator and it is your duty to configure the firewall rules to protect the company's network. Figure 1 shows the architecture of your company network and the IP addresses of the computers. Table 1 shows the port numbers that are helpful in writing your firewall rules. Refer to the [1] for the formatting of Cisco Firewall Rules. Answer the following discussion questions. Web Server www.firewall.edu 152.8.1.1 Email Server emai firewall.edu 152.8.2.2 Domain Name Server dns.firewall.edu 152.8.3.3 Internet router FTP Server ftp.firewall.edu 152.8.4.4 router & firewall Network Administrator netadmin firewall.edu 152.8.5.5 router Fred's computer fred firewall.edu 152.8.100.1 Jane's computer jane firewall.edu 152.8.100.2 100 computers 152.8.100.3 to 152.8.100.102 Figure 1: IP Addresses of each machine Table 1. Port Numbers Port Service 21 FTP 23 Telnet 25 Simple Mail Transport Protocol 53 Domain Name Servers 69 Trivial FTP 80 HTTP 110 POP3 client email 123 Network Time Protocol 137-139 143 161 443 445 1863 1214 3389 Microsoft NETBIOS IMAP4 client email Simple Network Maintenance Protocol HTTPS Windows File Sharing MSN Instant messaging Kazaa Windows Remote Desktop Protocol 5190 AOL instant messenger 28800- MSN Gaming Zone 29100 49876 Firewall Simulation 3. Discussion Questions Cisco Firewall Rule Case Description Questions (Put in Word Doc) 1. Write the Cisco-like firewall rules to satisfy the following policy: 1) Allow access to the homepage of your company. 2) Allow the DNS to be accessed. 3) Allow anyone to send email to the employee's company account. 4) Allow employees to access their company email account via POP. 5) Allow the FTP server to be accessed. 6) Disallow anyone to access your SNMP data. 7) Disallow employees to access www.wasteoftime.com 8) Allow anyone to send an AOL instant message to an employee in the company. 9) Allow anyone to send an MSN instant message to an employee in the company. 10) Prohibit Kazaa on all computers. 11) Allow the CEO of the company to access the private Microsoft file share of the network administrator. 12) Disallow others in the company to access the private Microsoft file share of the network administrator. 13) Allow someone at 222.111.000.44 to do a Microsoft remote desktop connection to Jane's computer. *FANSHAWE 1.3 What changes would be necessary if the main router did not function as a firewall but the two other routers performed the firewall responsibilities? Part 2: Modified Topology Web Server www.firewall.edu 1528.1.1 Email Server emai firewall.edu 152 8.2.2 Internet DMZ Trusted Network Domain Name Server dns firewall.edu 152.8.3.3 router & firewall Network Administrator netadmin.firewall.edu 152.8.5.5 A Server A firewall edu 152.84.4 router & firewall Fred's computer fred.firewall.edu 152.8.100.1 100 computers 152.8.100.3 to 152.8.100.102 Jane's computer jane.firewall.edu 152.8.100.2 Figure 2: Modified Network Topology Part 2 Discussion Questions *FANSHAWE 2.1 How would the firewall capabilities change if the firewall was a separate box that came between the routers and the Internet? 2.2 Suppose the network architecture is changed to be as Figure 2. Reconfigure the firewall rules for both firewalls. 2.3 Explain why it is important to configure firewall effectively References This case study is based on the Firewall Simulation Game developed by Dr. Williams at North Carolina A&T State University.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


