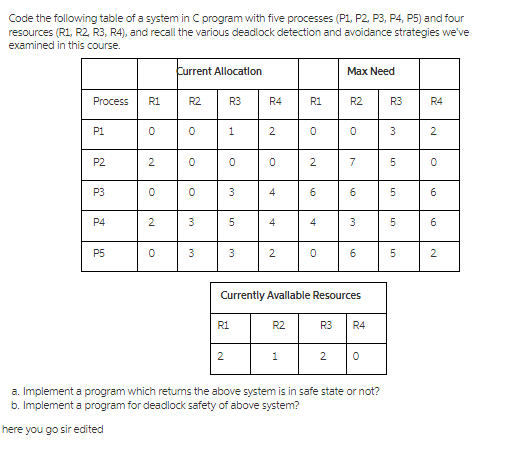
Code the following table of a system in C program with five processes (P1, P2, P3,...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
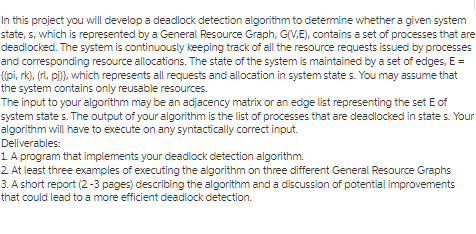
Code the following table of a system in C program with five processes (P1, P2, P3, P4, P5) and four resources (R1, R2, R3, R4), and recall the various deadlock detection and avoidance strategies we've examined in this course. Process P1 P2 P3 P4 P5 R1 0 2 0 2 0 Current Allocation R2 0 0 0 3 3 R3 1 2 0 3 5 3 R1 R4 19 2 0 4 4 2 R2 R1 1 0 2 6 4 0 Max Need R2 0 7 Currently Avallable Resources 6 3 6 R3 R4 2 0 a. Implement a program which returns the above system is in safe state or not? b. Implement a program for deadlock safety of above system? here you go sir edited R3 3 LO 5 5 5 5 R4 2 0 6 6 2 In this project you will develop a deadlock detection algorithm to determine whether a given system state, s, which is represented by a General Resource Graph, G(V.E), contains a set of processes that are deadlocked. The system is continuously keeping track of all the resource requests issued by processes and corresponding resource allocations. The state of the system is maintained by a set of edges, E = {(pi, rk), (rl, pj)}, which represents all requests and allocation in system states. You may assume that the system contains only reusable resources. The input to your algorithm may be an adjacency matrix or an edge list representing the set E of system states. The output of your algorithm is the list of processes that are deadlocked in states. Your algorithm will have to execute on any syntactically correct input. Deliverables: 1. A program that implements your deadlock detection algorithm. 2. At least three examples of executing the algorithm on three different General Resource Graphs 3. A short report (2-3 pages) describing the algorithm and a discussion of potential improvements that could lead to a more efficient deadlock detection. Code the following table of a system in C program with five processes (P1, P2, P3, P4, P5) and four resources (R1, R2, R3, R4), and recall the various deadlock detection and avoidance strategies we've examined in this course. Process P1 P2 P3 P4 P5 R1 0 2 0 2 0 Current Allocation R2 0 0 0 3 3 R3 1 2 0 3 5 3 R1 R4 19 2 0 4 4 2 R2 R1 1 0 2 6 4 0 Max Need R2 0 7 Currently Avallable Resources 6 3 6 R3 R4 2 0 a. Implement a program which returns the above system is in safe state or not? b. Implement a program for deadlock safety of above system? here you go sir edited R3 3 LO 5 5 5 5 R4 2 0 6 6 2 In this project you will develop a deadlock detection algorithm to determine whether a given system state, s, which is represented by a General Resource Graph, G(V.E), contains a set of processes that are deadlocked. The system is continuously keeping track of all the resource requests issued by processes and corresponding resource allocations. The state of the system is maintained by a set of edges, E = {(pi, rk), (rl, pj)}, which represents all requests and allocation in system states. You may assume that the system contains only reusable resources. The input to your algorithm may be an adjacency matrix or an edge list representing the set E of system states. The output of your algorithm is the list of processes that are deadlocked in states. Your algorithm will have to execute on any syntactically correct input. Deliverables: 1. A program that implements your deadlock detection algorithm. 2. At least three examples of executing the algorithm on three different General Resource Graphs 3. A short report (2-3 pages) describing the algorithm and a discussion of potential improvements that could lead to a more efficient deadlock detection.
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
Provide an elevator speech. The elevator speech should be a geared toward academics and the a community of learners, including fellow students, faculty, staff, and support teams. It should be...
-
If a zero of f is i, find the complete factored form of f(x) = x 4 + x 3 + 2x 2 + x + 1.
-
Why is it a good idea to create a "Budgeting Assumptions" tab when creating a master budget in Microsoft Excel?
-
Define the sampling distribution.
-
How does ICT impact communications?
-
Montpelier Lumber Corp. reported the following information. Compute the following for each year, 20092011. 1. Return on equity 2. Times interest earned (ignore income taxes) 3. Earnings per share 4....
-
At a company Christmas party Barney scares John and Holly by putting on a ski mask and telling them to give up their money. John, not realizing it was a prank hits Barney and knocks him out. Seeing...
-
XYZ is a calendar-year corporation that began business on January 1, 2020. For the year, it reported the following information in its current-year audited income statement. Notes with important tax...
-
6. For the apparatus used in this laboratory, the centripetal force is the same for a fixed radius R of rotation. Why is that statement true for this apparatus? (Hint-What provides the centripetal...
-
Fly Fast Ltd operates a small charter plane operation in South West Queensland. The airline provides a fly-in fly-out service to mining operations in this area. Currently Fly Fast operates one plane...
-
How much writing is required by people working in your career area? The best way to learn about on-the-job writing is to talk with someone who has a job similar to the one you hope to have one day....
-
Write a rsum that you could use in your job search. As your instructor directs, a. Write a rsum for the field in which you hope to find a job. b. Write two different rsums for two different job paths...
-
Working individually, in pairs, or in small groups, as your instructor directs, look at six profiles on LinkedIn. You could use those of your classmates, family members, or local businesspeople. ...
-
Careful business writers always document their sources in written reports; however, when the report findings are presented by using PowerPoint, the sources are often omitted. Should information in...
-
(X,-X) Why do we write the estimate b, as 2k Y, where k, = %3D EX,-X in O a. It is easier to prove the biasedness and the minimum variance for b, using the k; properties. O b. Use k, properties to...
-
You work as an operations consultant for a textile company. Your client has a well-established distribution system in the US market. The company has hundreds of stores and four distribution centers....
-
Consider the following solution to the mutual-exclusion problem involving two processes P0 and P1. Assume that the variable turn is initialized to 0. Process P0's code is presented below. /* Other...
-
Can the Count = write(fd, buffer, nbytes); call return any value in count other than nbytes? If so, why?
-
Even when there is plenty of free memory available, and the memory manager does not need to trim working sets, the paging system can still frequently be writing to disk. Why?
-
Discuss the significance of discounting in business decision making.
-
What are the main components of corporate directional strategies?
-
Discuss the advantages of real options over other capital budgeting evaluation techniques.

Study smarter with the SolutionInn App


