Question: computer network security questions Help please!!! thanks Authentication/Key Distribution(2+4+2+2) Consider the following protocol for Authentication/Key Distribution: (X and Y are two nodes, A is a
computer network security questions Help please!!! thanks
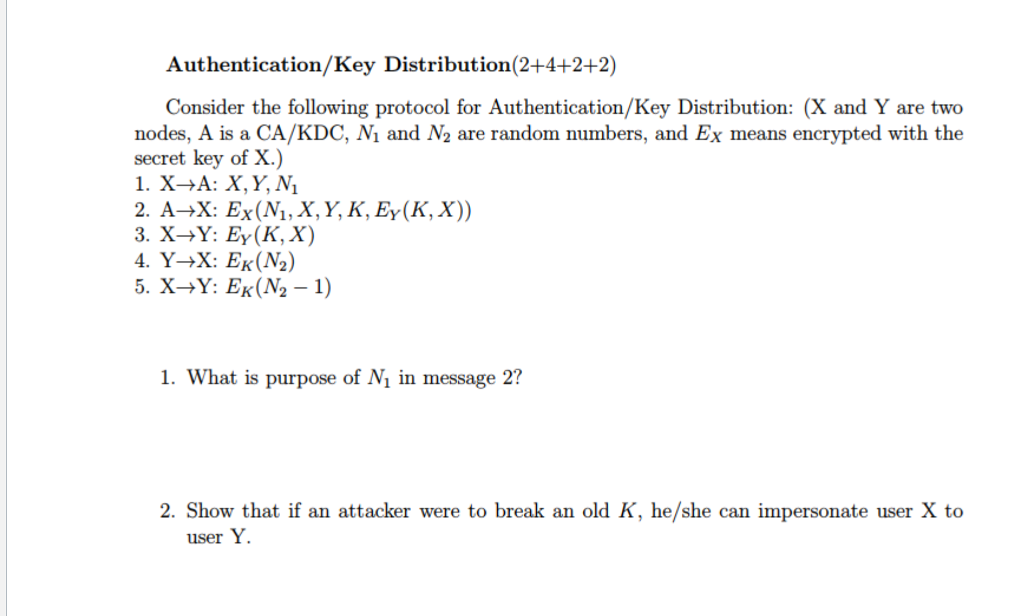
Authentication/Key Distribution(2+4+2+2) Consider the following protocol for Authentication/Key Distribution: (X and Y are two nodes, A is a CA/KDC, Ni and N2 are random numbers, and Ex means encrypted with the secret key of X.) 2. A--X: Ex(N,, X, Y, K, Ey(K, X)) 1. What is purpose of N in message 2? 2. Show that if an attacker were to break an old K, he/she can impersonate user X to user Y
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


