Question: Consider the element distinctness problem: Given an array A storing n inte- gers, determine whether all the elements in the array are distinct or
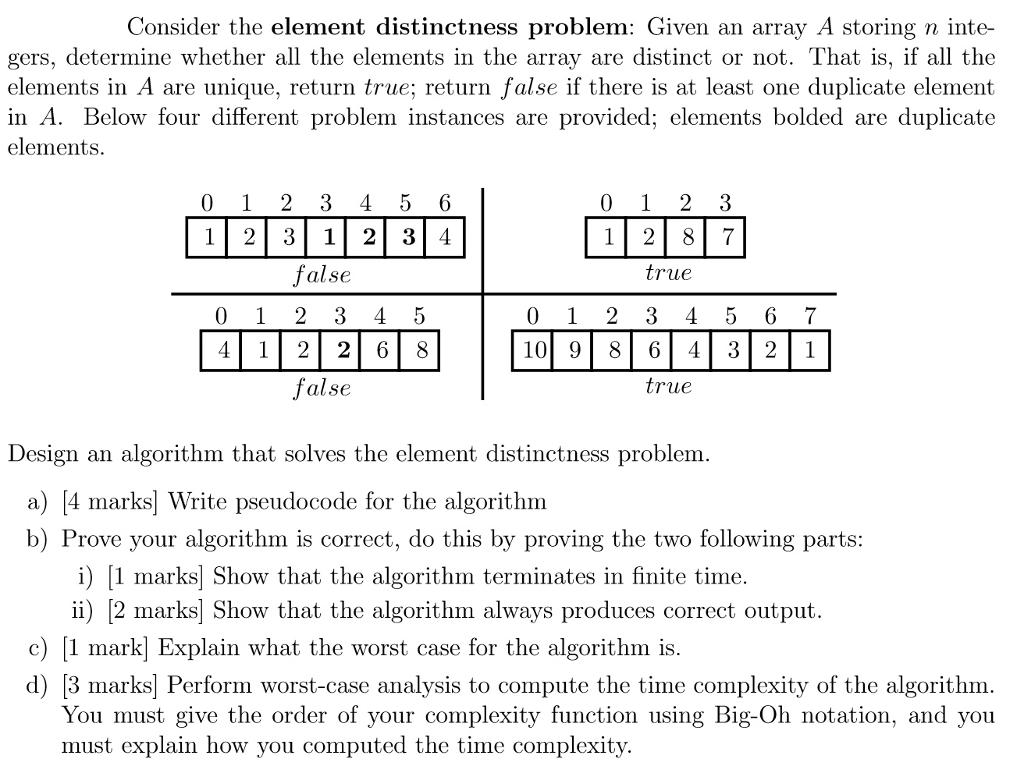
Consider the element distinctness problem: Given an array A storing n inte- gers, determine whether all the elements in the array are distinct or not. That is, if all the elements in A are unique, return true; return false if there is at least one duplicate element in A. Below four different problem instances are provided; elements bolded are duplicate elements. 0 1 0 4 1 2 2 3 1 1 3 1 false 3 2 2 2 false 4 5 6 2 3 4 4 5 6 8 0 1 10 9 0 1 1 2 2 8 2 8 true 3 4 6 4 true 3 7 5 6 7 3 2 1 Design an algorithm that solves the element distinctness problem. a) [4 marks] Write pseudocode for the algorithm b) Prove your algorithm is correct, do this by proving the two following parts: i) [1 marks] Show that the algorithm terminates in finite time. ii) [2 marks] Show that the algorithm always produces correct output. c) [1 mark] Explain what the worst case for the algorithm is. d) [3 marks] Perform worst-case analysis to compute the time complexity of the algorithm. You must give the order of your complexity function using Big-Oh notation, and you must explain how you computed the time complexity.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


