Question: Consider the following servlet implementing a micro-blog entry public class AddMBlogEntry extends HttpServlet ( Public void doPost(HttpServletRequest req.. HttpServletResponse res) Throws ServletExceptoin, IOExceptoin ( //
Consider the following servlet implementing a micro-blog entry
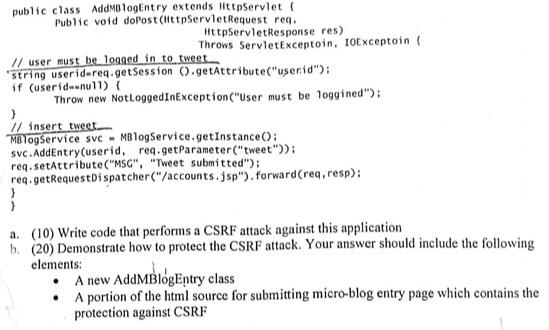
public class AddMBlogEntry extends HttpServlet ( Public void doPost(HttpServletRequest req.. HttpServletResponse res) Throws ServletExceptoin, IOExceptoin ( // user must be logged in to tweet string userid-req.getSession ().getAttribute("userid"); if (userid=null) { Throw new NotLoggedInException ("User must be loggined"); } // insert tweet. MBlogService svc MBlogService.getInstance(): svc.AddEntry(userid, req.getParameter("tweet")); req.setAttribute("MSG", "Tweet submitted"); req.getRequestDispatcher("/accounts.jsp"). forward (req, resp); a. (10) Write code that performs a CSRF attack against this application. b. (20) Demonstrate how to protect the CSRF attack. Your answer should include the following elements: A new AddMBlogEntry class A portion of the html source for submitting micro-blog entry page which contains the protection against CSRF
Step by Step Solution
3.48 Rating (158 Votes )
There are 3 Steps involved in it
AddMBlogEntry class import javaioIOException import javaioNotActive Exception import javaxservletSer... View full answer

Get step-by-step solutions from verified subject matter experts


