Question: Consider the Rabin-Karp algorithm to look for the pattern baab in the string ababaabaa assuming the alphabet {a, b, c, d}, and the hash
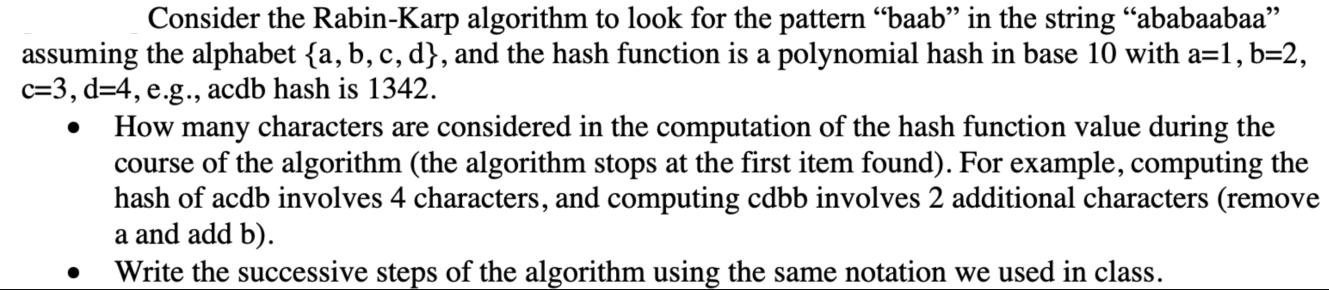
Consider the Rabin-Karp algorithm to look for the pattern "baab" in the string "ababaabaa" assuming the alphabet {a, b, c, d}, and the hash function is a polynomial hash in base 10 with a=1, b=2, c=3, d=4, e.g., acdb hash is 1342. How many characters are considered in the computation of the hash function value during the course of the algorithm (the algorithm stops at the first item found). For example, computing the hash of acdb involves 4 characters, and computing cdbb involves 2 additional characters (remove a and add b). Write the successive steps of the algorithm using the same notation we used in class.
Step by Step Solution
3.35 Rating (158 Votes )
There are 3 Steps involved in it
Given Alphabet a b c d with hash values a1 b2 c3 d4 String abababa Pattern ba Step 1 Initialize vari... View full answer

Get step-by-step solutions from verified subject matter experts


