Question: Consider using genetic algorithms to solve the TSP shown in figure 6. 1) Define two intermediary tables: One for the students that have enrolled
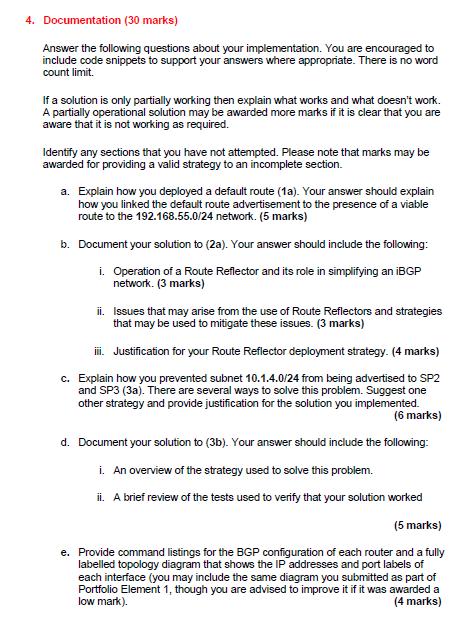
Consider using genetic algorithms to solve the TSP shown in figure 6.
1) Define two intermediary tables: One for the students that have enrolled in a course and the other one for the relationship between instructors and the courses. (Hint: you need to design the database as the third normal form or 3NF). Explain what columns will be present in the intermediary tables.
2) Draw the ER diagram of the 3NF design of the database.

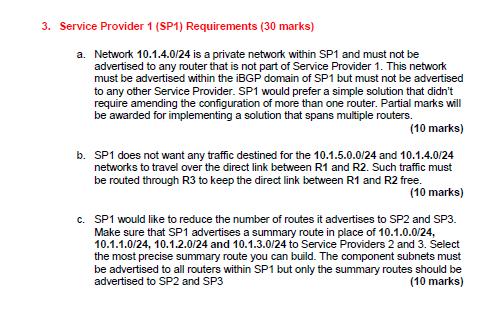
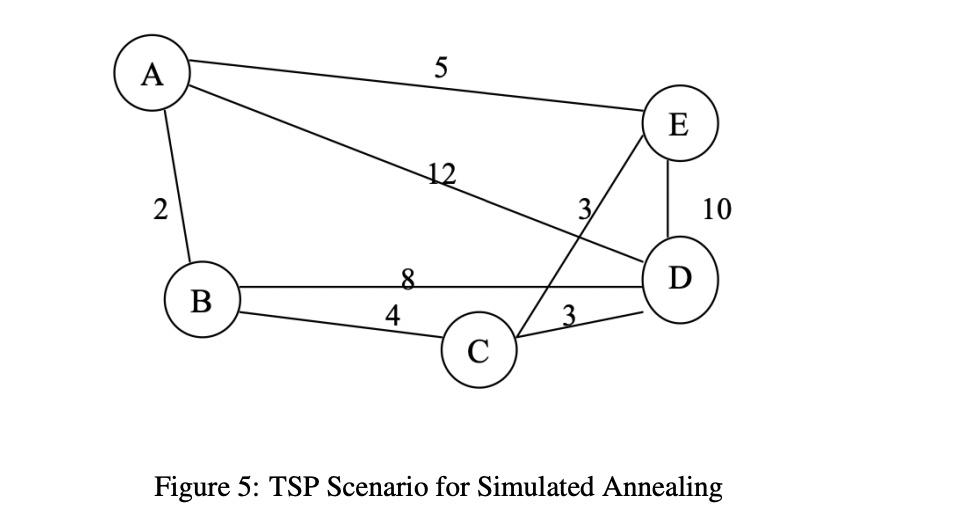
The traveling salesman problem (TSP) is a classic combinatorial problem in operation research and computer science. A concise definition with a graph is as follows: Given a set of vertices V = {vi}, and a set of edges E = {ei j} such that for any i, j, ei j = eji exists if and only if vi and vj are connected. The objective of the problem is to find the shortest path that starts and ends on a specific vertex (the same vertex), and visit each other vertex exactly once. There are many ways to solve TSP, exact solutions can be found by using integer linear programming, like the cutting-plane method. Heuristic and approximation methods include genetic algorithms, and simulated annealing. In this section, we apply Simulated Annealing and Genetic Algorithm to solve small TSP instances.
 Consider using genetic algorithms to solve the TSP shown in figure 6.
Consider using genetic algorithms to solve the TSP shown in figure 6.
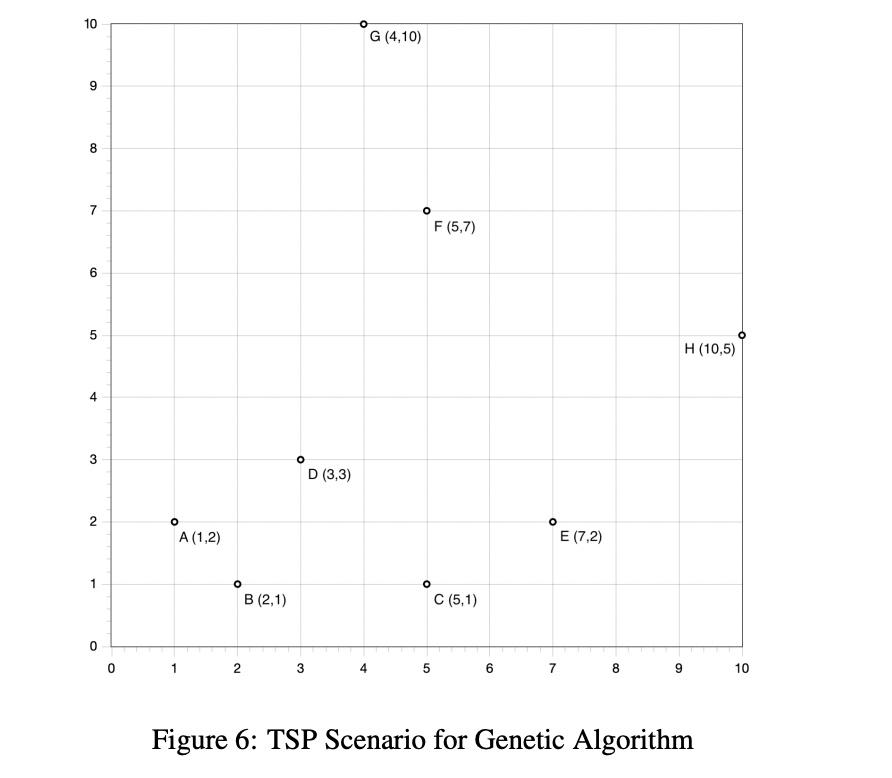
We define the cost of each path as the sum of the squared Euclidean distance between each connected pair in the path. For example, distance between A-B is (1−2)2+(2−1)2=2and the distance of the partial path A-B-C-A is the sum of A-B, B-C and C-A. Let us define the fitness score F as F = 1/cost.
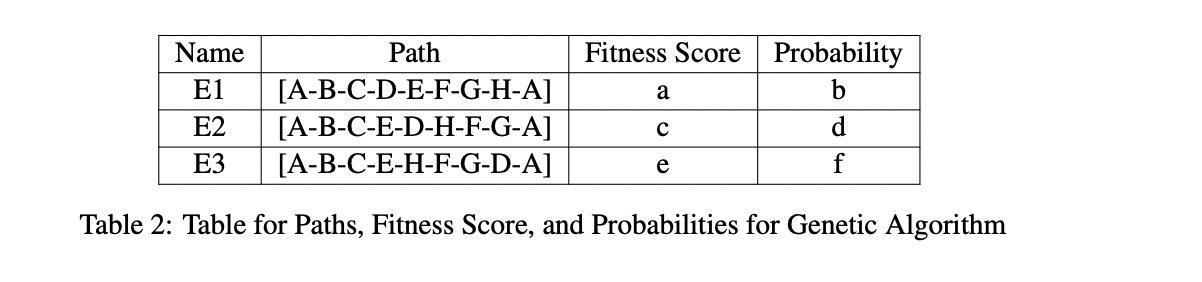
Question: Given the three initial paths, as shown in Table 2, compute the fitness score and its probability. The probability of each path is proportional to the fitness score.
What is the value of a,b,c,d,e,f as shown in the table
For completeness, we describe how a Genetic Algorithm can proceed afterward. We then pick two paths with higher probability (or fitness score), keep 4 initial letters unchanged in the first path route, e.g. "A-B-C-D" in E1. Replace the rest from the second path with the same order. For example, A-B-C-D-E-F-G-H-A and A-B-C-E-D-H-F-G-A would produce A-B-C-D-E-H-F-G-A as one of the off-springs. For the off-spring produced, we mutate the off-spring by permuting the 3rd and 4th index. In the last example, we will produce A-B-D-C-E-H-F-G-A as a mutated off-spring.
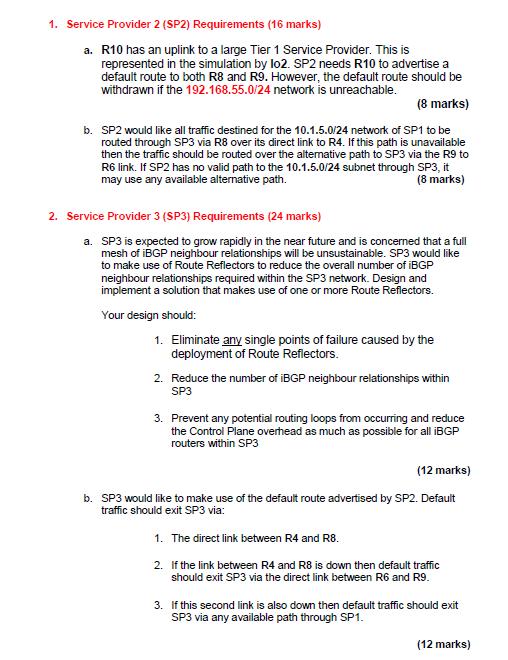
HDLC:
a. (7 points) Two stations communicate via a 2 Mbps satellite link with a
propagation delay of 300 ms. The satellite serves as a relay station
with negligible switching delay. Using HDLC frames of a certain size,
employing a 7 bit sequence number and a 32 bit FCS, the maximum
possible data throughput, i.e. the throughput of data bits carried in
HDLC frames, is observed to be 1.498088125 Mbps. Calculate the size
of the data block (information field size) , in octets, carried in each
HDLC frame. Round up your answer to the next integer before
converting your answer into octets.
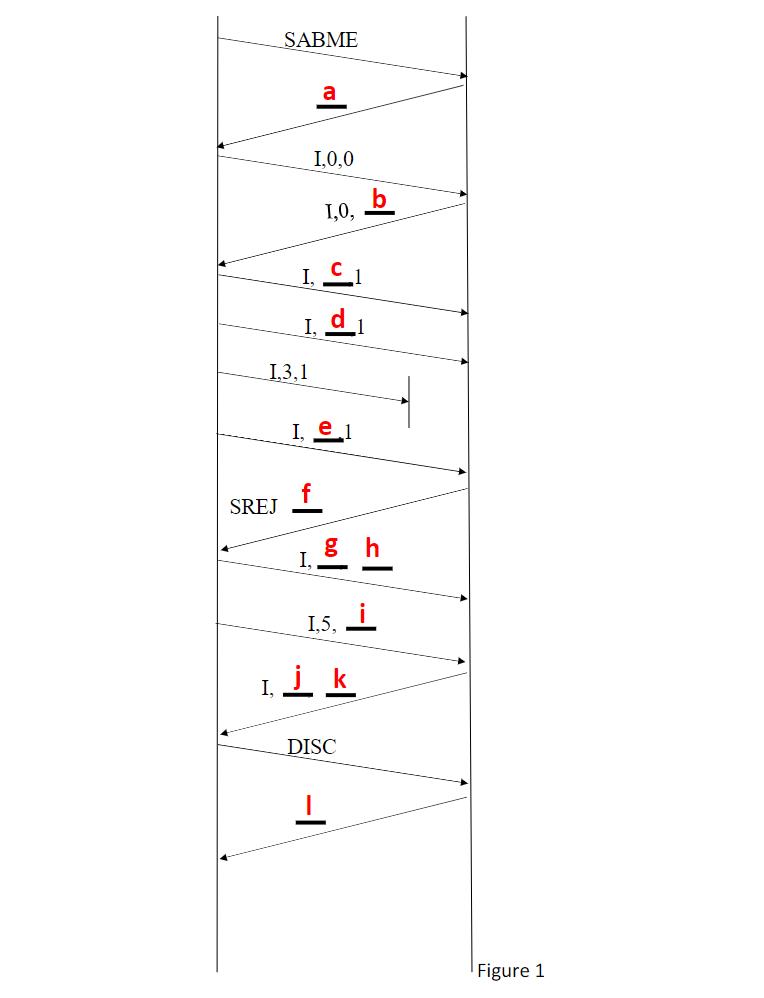
b. Consider an HDLC communication shown below in Figure 1 (next
page).
i. (6 points) Fill in the blanks (underscores with lower case
letters) where you see an underline on the next page. There is
no need to redraw the timing diagram. In your solution packet,
mention the information, which will replace the underlined
lower case letters (shown in red).
ii. (2 points) What kind of ARQ technique is being employed
here?
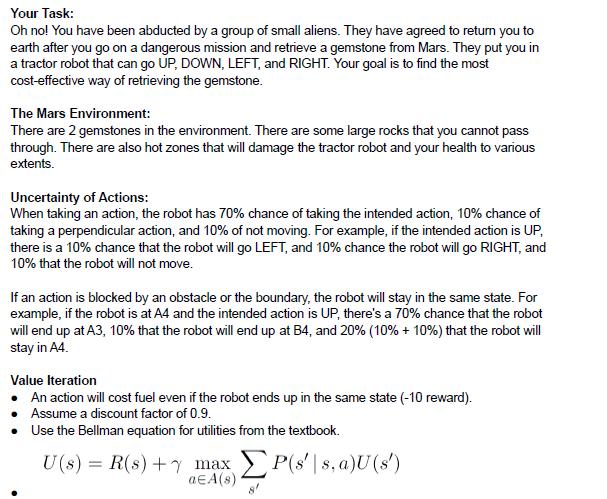
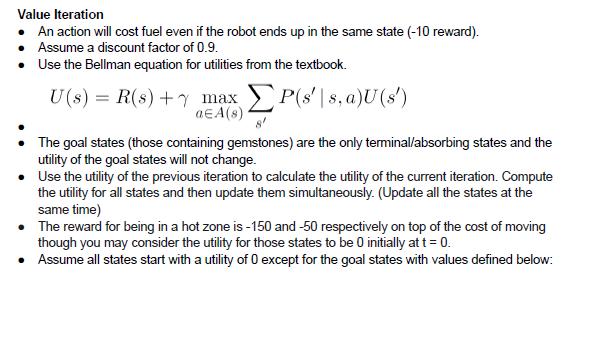
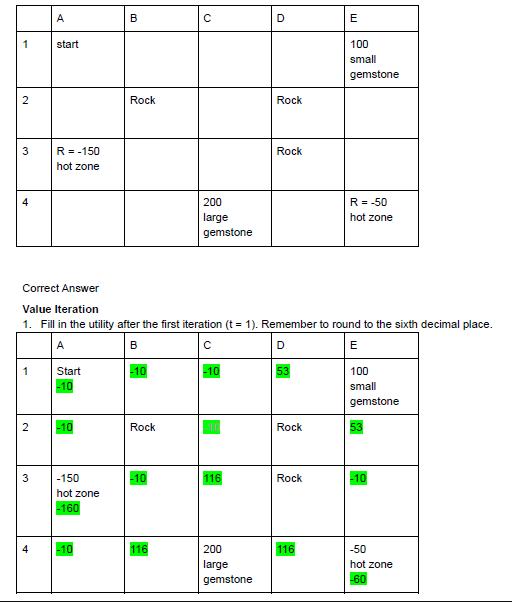
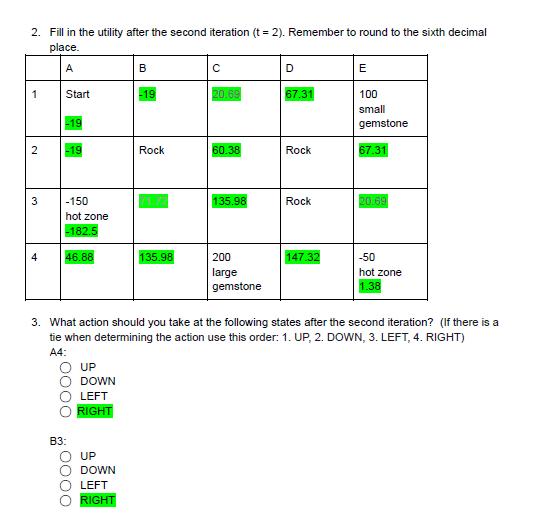
Can any one please given me hand written answer and explain the solution already provided. The answers are highlighted for iteration 1 and 2 but i need help on how to calculate A1, A2,A3,A4,B1,B2,B3,B4,C1,C2,C3,C4,D1,D2,D3,D4,E2,E3
Typed answers are difficult to follow as they are recursive in nature. Please please help ASAP
The incident scenario this time is that an employee was installing a new computer. They were in the process of installing software when they noticed abnormal mouse activity on the computer. At that point, they walked away from the computer and called you for help. Treat this like an incident at a corporation, although the computer is not joined to a domain.
I am expecting that at a minimum you are able to tell the story of what happened during the incident. What was the initial infection vector, what happened next? Are there any persistence mechanisms in play? Are there any IP addresses associated with the attacker? And if so, what are they?
You should list 5 Indicators of Compromise that you gleaned from the evidence that are worth searching for enterprise wide to make sure no other systems are infected. These will be best displayedinatablefortheIOCsection. TheseIOCswillbedevelopedwhenyoufind artifacts related to the investigation. A timeline should also be put into the report like last time.
You will also need to develop 10 investigative questions that you would ask during the course of this investigation.
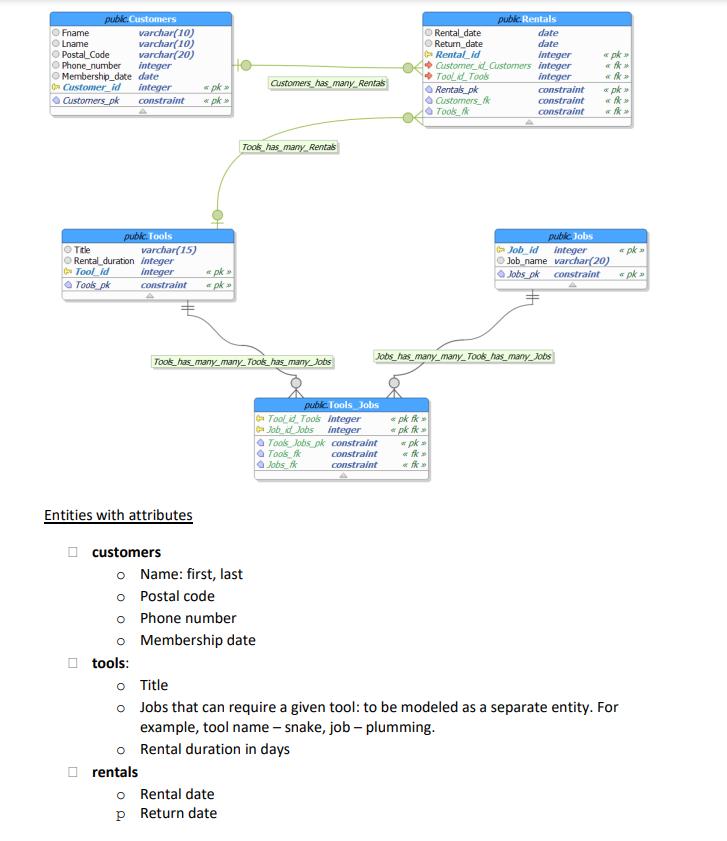
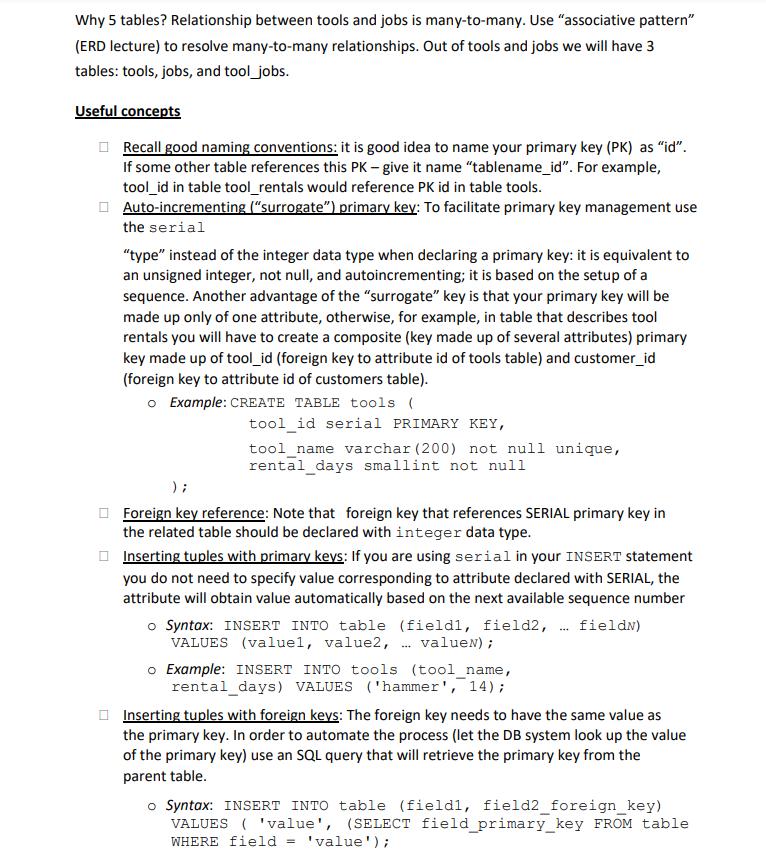
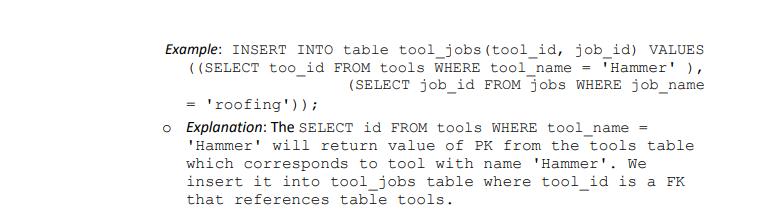
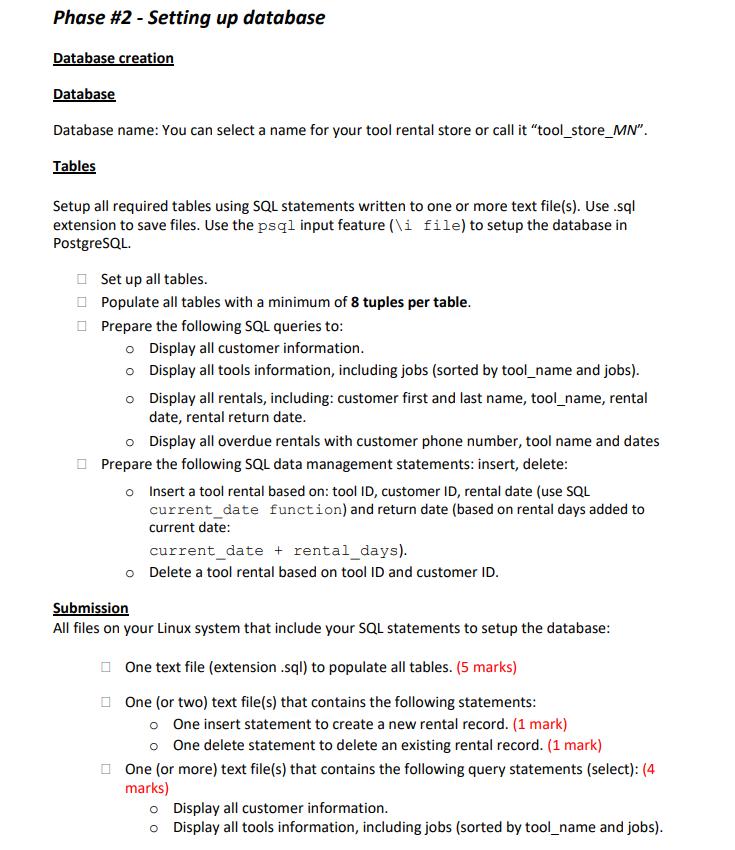
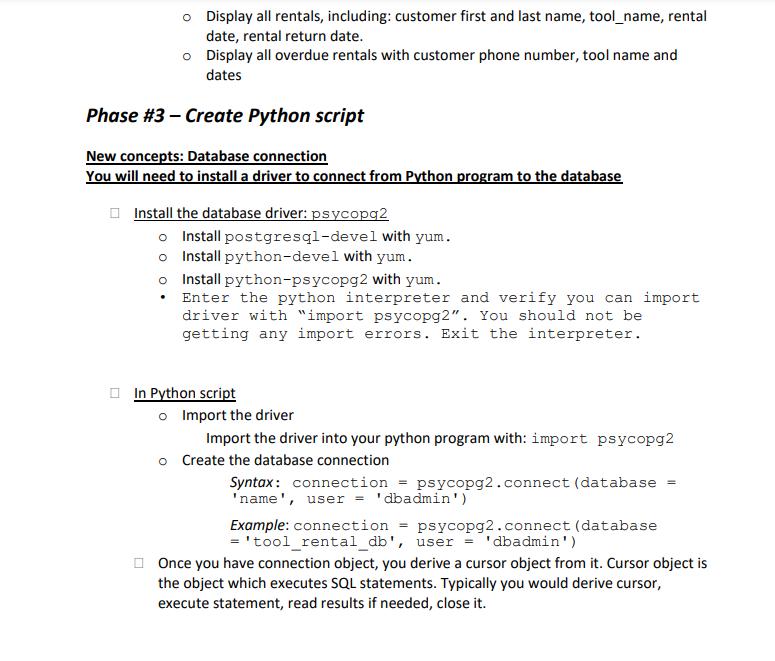
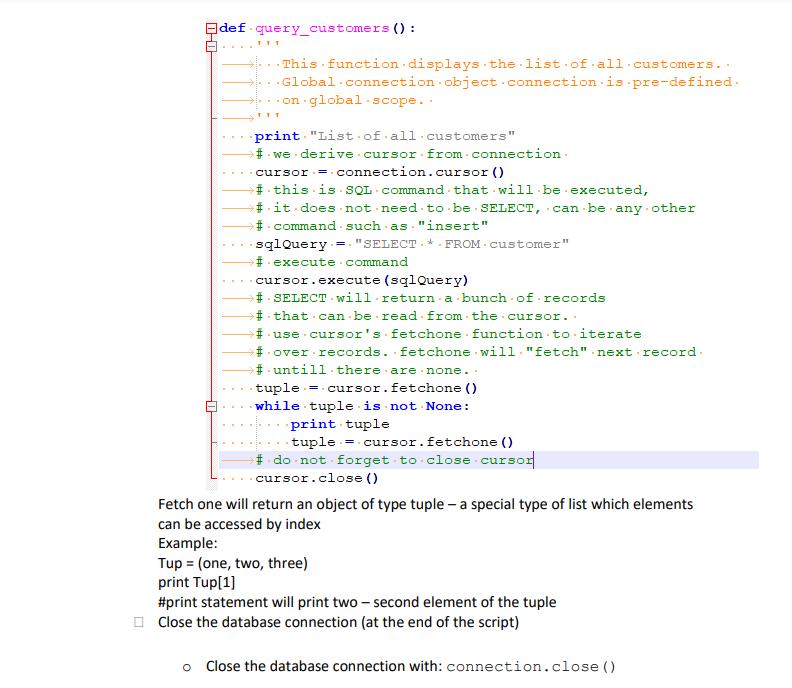
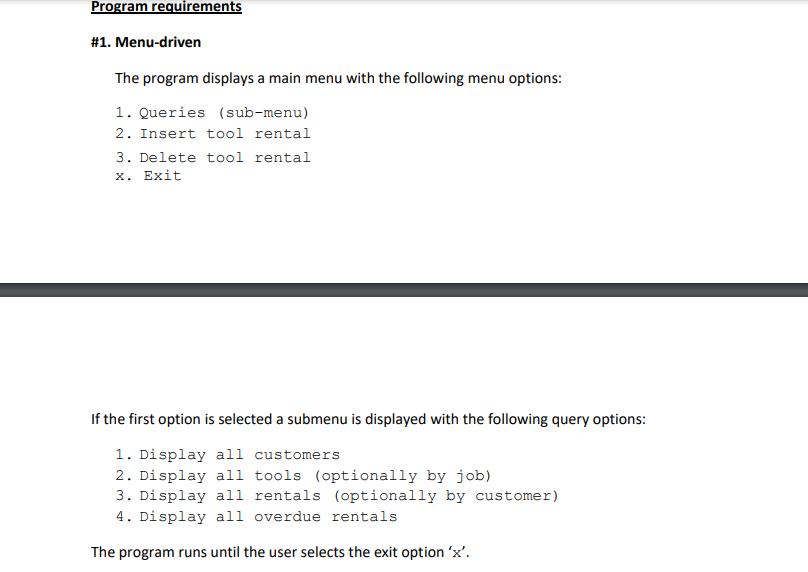
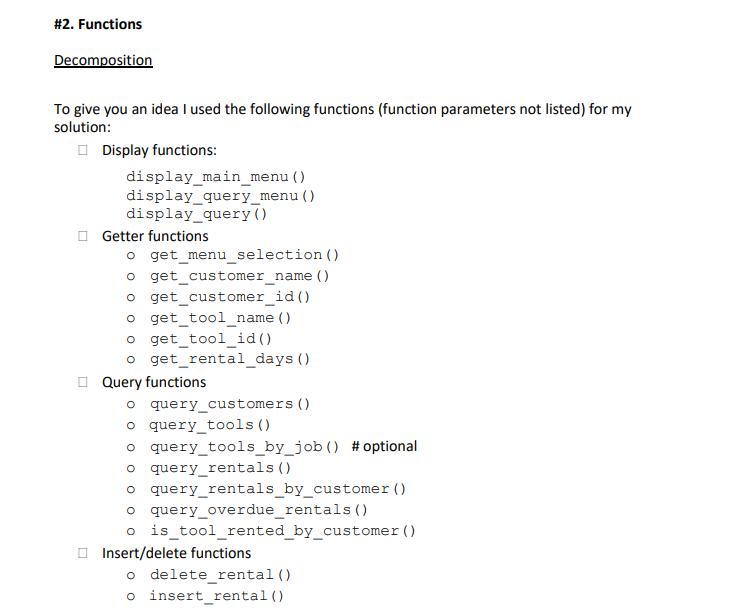
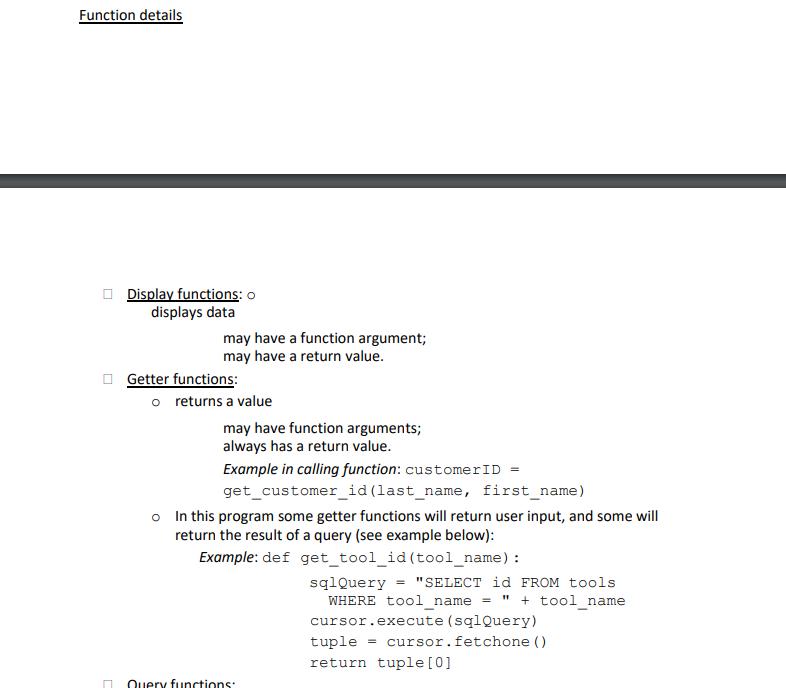
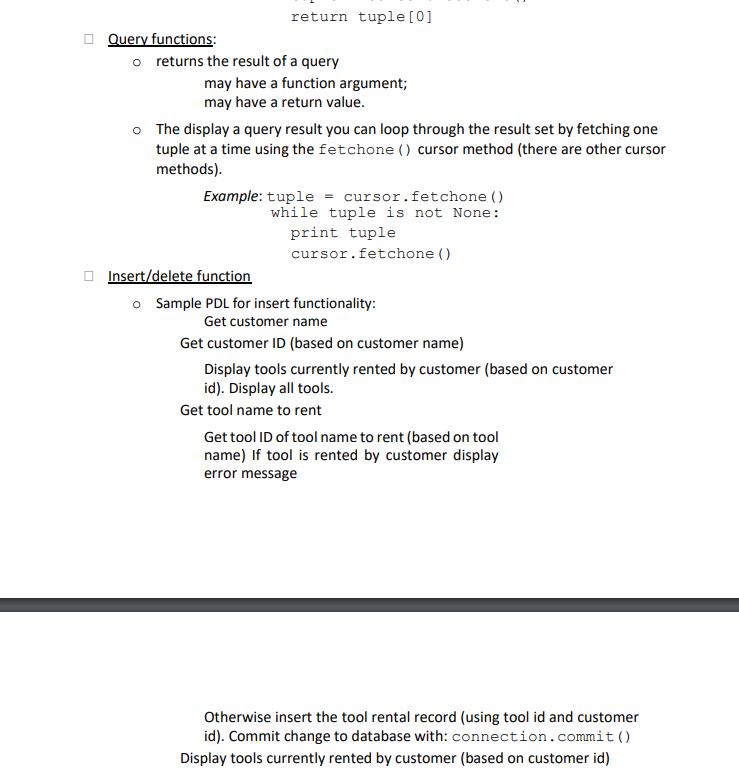
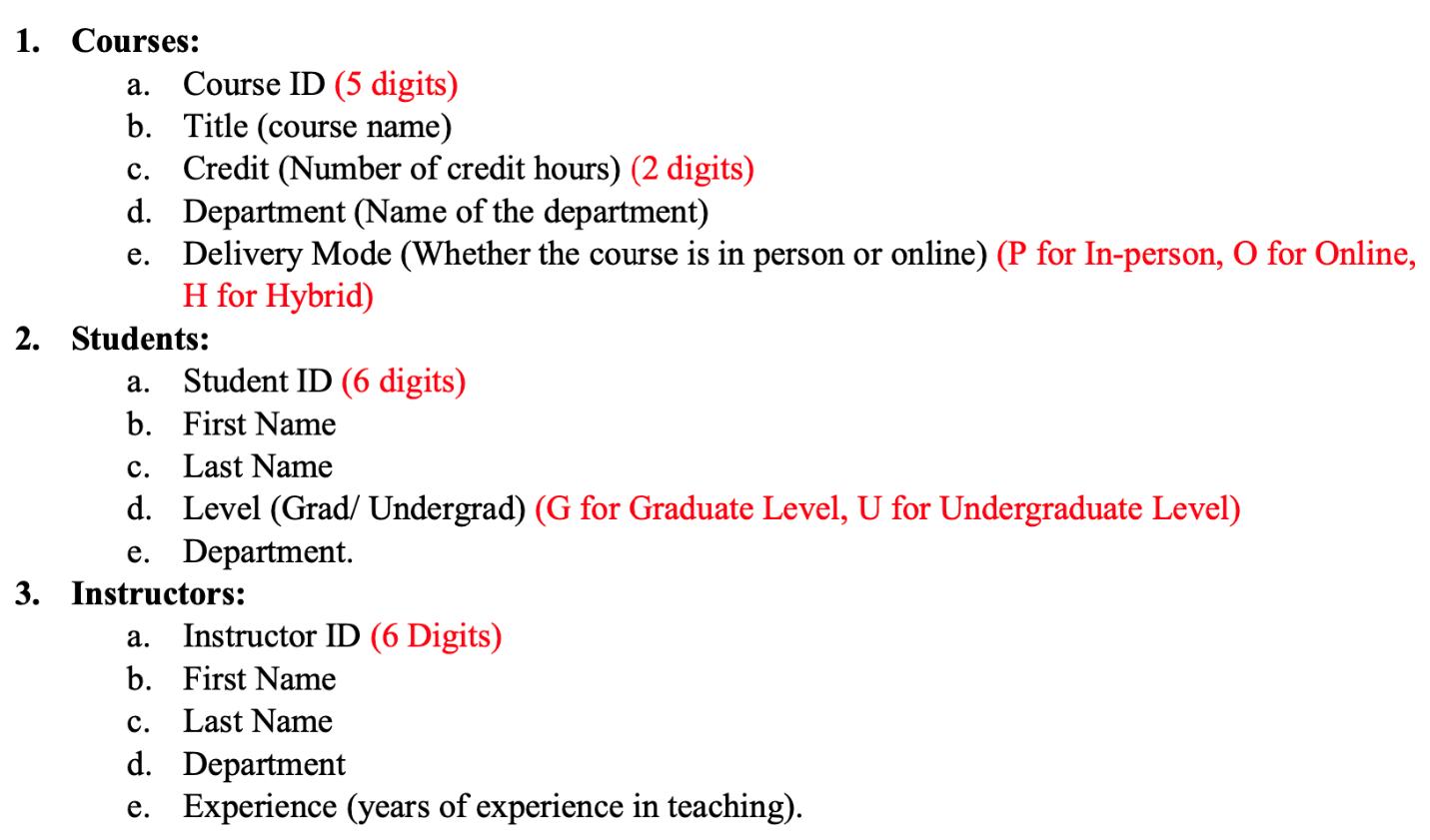
Project: Tools rental store Section A - Setup Python for database connection Project overview The project includes two phases: o Phase #1: Database creation, which includes o Database creation o Table creation. o Table population o Data management: Queries (select), Insert, Delete Submission: Text files with extension *.sql with SQL statements, all required screenshots o Phase #2: Python program to manage database Submission: Python script, demo by providing all required screenshots Phase #1 - Database conceptual design Data requirements The following data has to be managed for the tool rental store: customer information, tools information, rental information. This will require 5 tables.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


