/courses/ 672012.1/dl/outline Question 7 Question 8 x What of the following is not a purpose of...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
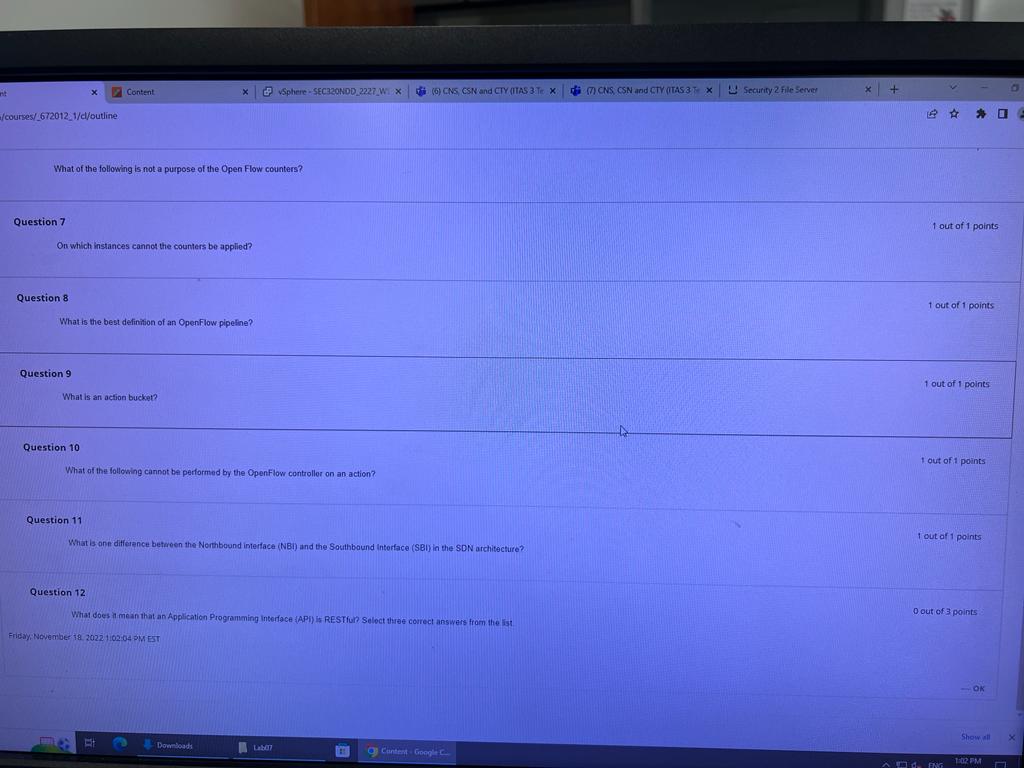
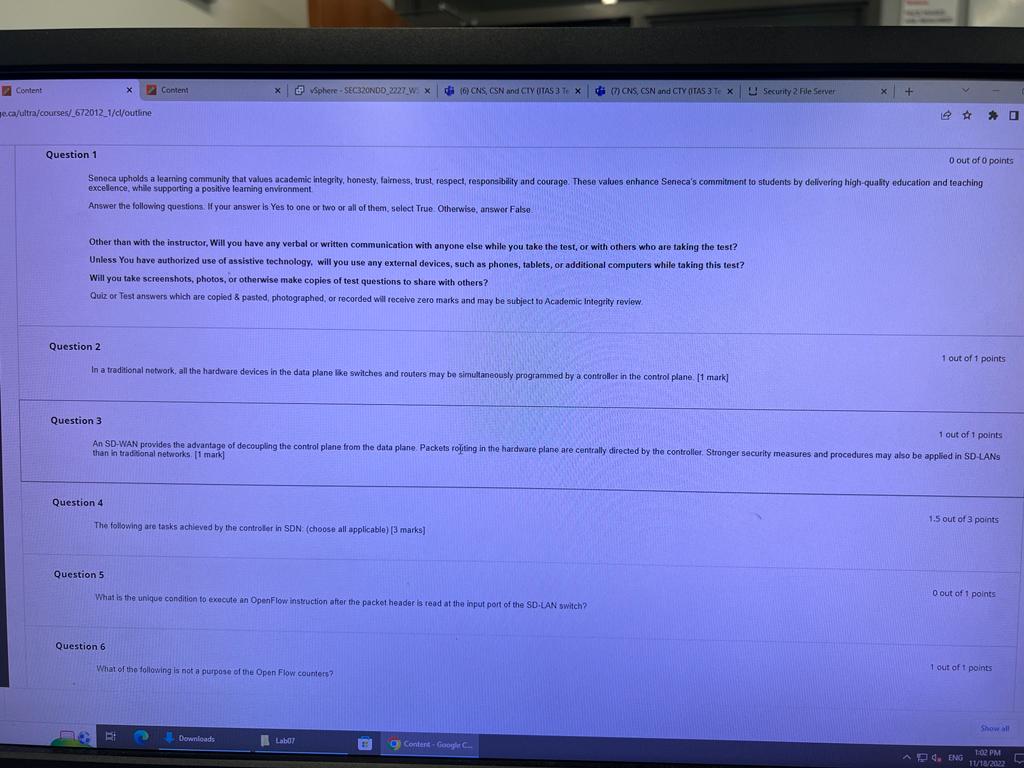
/courses/ 672012.1/dl/outline Question 7 Question 8 x What of the following is not a purpose of the Open Flow counters? On which instances cannot the counters be applied? Question 9 Content What is the best definition of an OpenFlow pipeline? Question 10 What is an action bucket? x What of the following cannot be performed by the OpenFlow controller on an action? B B vSphere-SEC320NDD 2227 W X Question 11 What is one difference between the Northbound interface (NBI) and the Southbound Interface (SBI) in the SDN architecture? Question 12 What does it mean that an Application Programming Interface (API) is RESTful? Select three correct answers from the list Friday, November 18, 2022 1:02:04 PM EST Downloads Lab07 (6) CNS, CSN and CTY (ITAS 3 Te X 111 Content Google C (7) CNS, CSN and CTY (ITAS 3T X Security 2 File Server X + 1 out of 1 points 1 out of 1 points 1 out of 1 points 1 out of 1 points 1 out of 1 points 0 out of 3 points - OK Show all O ^ ENG 1:02 PM d. C X Content e.ca/ultra/courses/_672012_1/cl/outline Content Question 4 X Other than with the instructor, Will you have any verbal or written communication with anyone else while you take the test, or with others who are taking the test? Unless You have authorized use of assistive technology, will you use any external devices, such as phones, tablets, or additional computers while taking this test? Will you take screenshots, photos, or otherwise make copies of test questions to share with others? Quiz or Test answers which are copied & pasted, photographed, or recorded will receive zero marks and may be subject to Academic Integrity review. Question 2 In a traditional network, all the hardware devices in the data plane like switches and routers may be simultaneously programmed by a controller in the control plane. [1 mark] Question 6 Sphere-SEC320NDD_2227_W: X Question 1 0 out of 0 points Seneca upholds a learning community that values academic integrity, honesty, fairness, trust, respect, responsibility and courage. These values enhance Seneca's commitment to students by delivering high-quality education and teaching excellence, while supporting a positive learning environment Answer the following questions. If your answer is Yes to one or two or all of them, select True. Otherwise, answer False The following are tasks achieved by the controller in SDN (choose all applicable) [3 marks] E Question 5 What is the unique condition to execute an OpenFlow instruction after the packet header is read at the input port of the SD-LAN switch? 2 Question 3 1 out of 1 points An SD-WAN provides the advantage of decoupling the control plane from the data plane. Packets rojiting in the hardware plane are centrally directed by the controller. Stronger security measures and procedures may also be applied in SD-LANS than in traditional networks. [1 mark] What of the following is not a purpose of the Open Flow counters? (6) CNS, CSN and CTY (ITAS 3 T X Downloads Lab07 (7) CNS, CSN and CTY (ITAS 3 Te x Security 2 File Server # x Content- Google C + 1 out of 1 points 1.5 out of 3 points 0 out of 1 points 1 out of 1 points 4. ENG O Show all 1:02 PM 11/18/2022 L /courses/ 672012.1/dl/outline Question 7 Question 8 x What of the following is not a purpose of the Open Flow counters? On which instances cannot the counters be applied? Question 9 Content What is the best definition of an OpenFlow pipeline? Question 10 What is an action bucket? x What of the following cannot be performed by the OpenFlow controller on an action? B B vSphere-SEC320NDD 2227 W X Question 11 What is one difference between the Northbound interface (NBI) and the Southbound Interface (SBI) in the SDN architecture? Question 12 What does it mean that an Application Programming Interface (API) is RESTful? Select three correct answers from the list Friday, November 18, 2022 1:02:04 PM EST Downloads Lab07 (6) CNS, CSN and CTY (ITAS 3 Te X 111 Content Google C (7) CNS, CSN and CTY (ITAS 3T X Security 2 File Server X + 1 out of 1 points 1 out of 1 points 1 out of 1 points 1 out of 1 points 1 out of 1 points 0 out of 3 points - OK Show all O ^ ENG 1:02 PM d. C X Content e.ca/ultra/courses/_672012_1/cl/outline Content Question 4 X Other than with the instructor, Will you have any verbal or written communication with anyone else while you take the test, or with others who are taking the test? Unless You have authorized use of assistive technology, will you use any external devices, such as phones, tablets, or additional computers while taking this test? Will you take screenshots, photos, or otherwise make copies of test questions to share with others? Quiz or Test answers which are copied & pasted, photographed, or recorded will receive zero marks and may be subject to Academic Integrity review. Question 2 In a traditional network, all the hardware devices in the data plane like switches and routers may be simultaneously programmed by a controller in the control plane. [1 mark] Question 6 Sphere-SEC320NDD_2227_W: X Question 1 0 out of 0 points Seneca upholds a learning community that values academic integrity, honesty, fairness, trust, respect, responsibility and courage. These values enhance Seneca's commitment to students by delivering high-quality education and teaching excellence, while supporting a positive learning environment Answer the following questions. If your answer is Yes to one or two or all of them, select True. Otherwise, answer False The following are tasks achieved by the controller in SDN (choose all applicable) [3 marks] E Question 5 What is the unique condition to execute an OpenFlow instruction after the packet header is read at the input port of the SD-LAN switch? 2 Question 3 1 out of 1 points An SD-WAN provides the advantage of decoupling the control plane from the data plane. Packets rojiting in the hardware plane are centrally directed by the controller. Stronger security measures and procedures may also be applied in SD-LANS than in traditional networks. [1 mark] What of the following is not a purpose of the Open Flow counters? (6) CNS, CSN and CTY (ITAS 3 T X Downloads Lab07 (7) CNS, CSN and CTY (ITAS 3 Te x Security 2 File Server # x Content- Google C + 1 out of 1 points 1.5 out of 3 points 0 out of 1 points 1 out of 1 points 4. ENG O Show all 1:02 PM 11/18/2022 L
Expert Answer:

Related Book For 

Accounting Information Systems
ISBN: 978-1260153156
2nd edition
Authors: Vernon Richardson, Chengyee Chang, Rod Smith
Posted Date:
Students also viewed these computer network questions
-
A small consulting company wants to make the switch to QuickBooks Online. All of their expenses are paid at the time they are incurred, so there is no need to track bills in the system. There is only...
-
Sugar (C12H22O11) is a molecular compound that stays together inwater, while NaCl and MgSO4?7H2O are ionic compounds that dissociate into cations andanions as illustrated in the NaCl example below:...
-
Choose one of the three following Finance principles: 1: Cash Flow. 2: Time Value of Money 3: Risk Requires a Reward Choose one of the principles that resonates with perspective on financial...
-
Use the Hamiltons Data Set to compute these profitability measures for 2014: a. Rate of return on net sales b. Rate of return on total assets c. Rate of return on common stockholders equity Are these...
-
Consider two binomial assets, each with price equal to 1. The first is a stock that at the end of a period pays either 3 or 0 with probabilities \(p\) and \(1-p\), respectively. The second asset is...
-
Vidi Corporation made the following purchases related to its property, plant, and equipment during its fiscal year ended December 31, 2014. The company uses the straight-line method of depreciation...
-
John is a farmer. In three months, his harvest will be ready and he will sell a big contract of 500,000 pounds of wheat. The spot market price of wheat is now $0.50 per pound but it is likely to...
-
ToyWorks Ltd. is a company that manufactures and sells a single product, which they call a Toodle. For planning and control purposes they utilize a monthly master budget, which is usually developed...
-
Use substitution to solve the system. -5x+4y = 28 y=2x+10 x= HQ X y = G
-
High Desert Potteryworks makes a variety of pottery products that it sells to retailers. The company uses a job - order costing system in which departmental predetermined overhead rates are used to...
-
Risk and Return Suppose you observe the following situation: Security Cooley Inc Moyer Company Beta Expected Return 1.8 22.00% 1.6 20.44 If the risk-free rate is 7%, are these securities correctly...
-
Crane Bucket Co . , a manufacturer of rain barrels, had the following data for 2 0 2 4 : Sales quantity: 2 , 340 barrels Unit selling price: $ 5 0 per barrel Unit variable costs: $53 per barrel Fixed...
-
How do transformational leaders harness visionary foresight, emotional intelligence, and strategic acumen to inspire organizational change, cultivate a shared sense of purpose, and mobilize disparate...
-
When a county receives cash advances under grants from the state, what account should it credit in its governmental-type funds if the grant eligibility requirements have not been met? Select one: A....
-
2. Addison's Disease: chronic adrenal deficiency most commonly caused by an autoim mune disorder that destroys the adrenal cortex. How would this disorder affect levels of CRH. ACTH, cortisol, and...
-
The domain of the variable in the expression x 3/x + 4 is________.
-
Using a brute-force attack, hackers can crack the password to a WEP access point in about 5 minutes and WPA2 in about 2 days. What does this tell you about the security of wireless networks?
-
As chief executive auditor, Mallory Williams heads the internal audit group of a manufacturing company in southern Texas. She would like to purchase a CAAT tool to assist her group in conducting...
-
The benefits of an IT initiative should be measured in comparison to the revenues and costs that will occur if the IT initiative is not implemented. What issues would a project team face when making...
-
Show that the group \(D_{3}\) has two 1D irreps in addition to the 2D irrep found in Problem 5.6 , and construct the character table. Derive the two-dimensional matrix representation Data from...
-
The matrix representation of \(\mathrm{C}_{3 \mathrm{v}}\) given in Eq. (5.14) was constructed with respect to the particular coordinate system defined by the unit vectors \(\boldsymbol{e}_{1}\) and...
-
Prove that the action of the symmetry operations \(\sigma_{b}\) and \(\sigma_{c}\) on the basis vectors \(\boldsymbol{e}_{1}\) and \(\boldsymbol{e}_{2}\) in Fig. 5.10 are given by the matrix...

Study smarter with the SolutionInn App