Question: Create a JAVA program that displays the following information in the format shown below. Your Official name Your programming experience and your expectation from
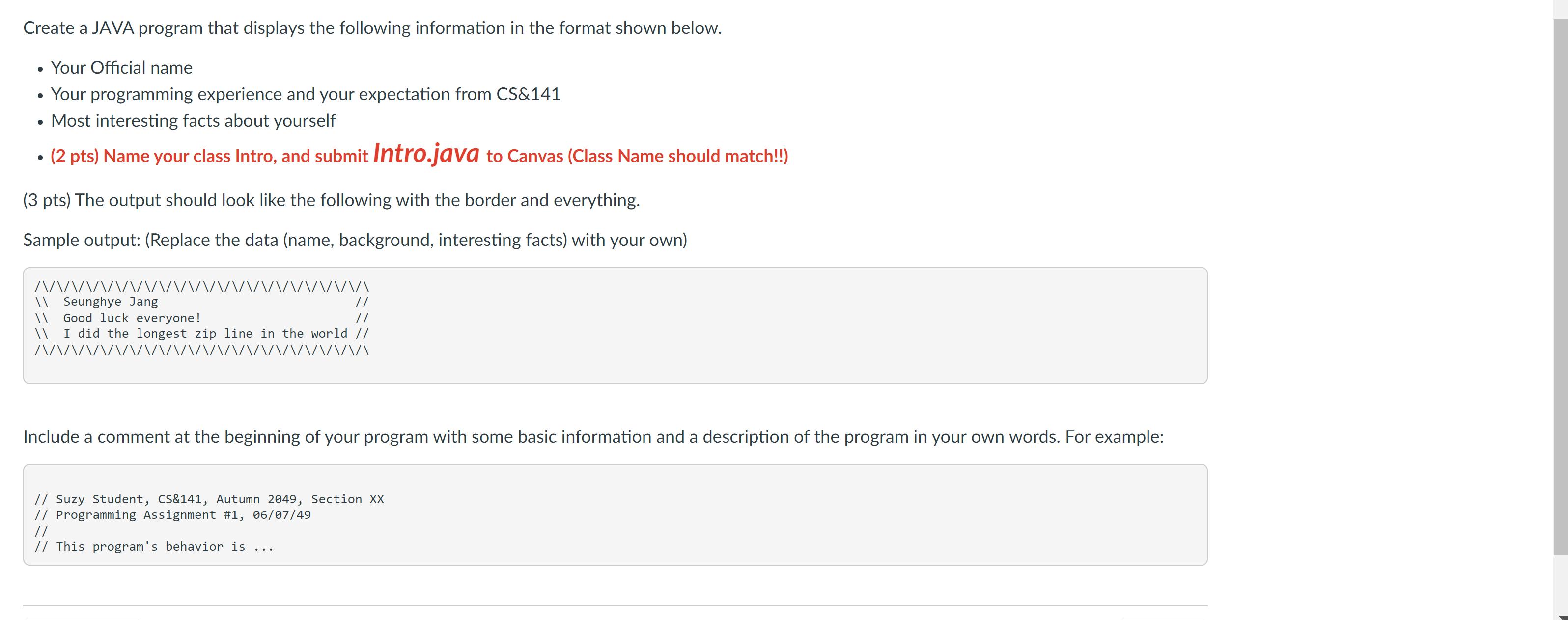
Create a JAVA program that displays the following information in the format shown below. Your Official name Your programming experience and your expectation from CS&141 . Most interesting facts about yourself (2 pts) Name your class Intro, and submit Intro.java to Canvas (Class Name should match!!) (3 pts) The output should look like the following with the border and everything. Sample output: (Replace the data (name, background, interesting facts) with your own) /\/\ \\ Seunghye Jang // // \\ Good luck everyone! \\ I did the longest zip line in the world // \/\/ VVVVVV VVVVX Include a comment at the beginning of your program with some basic information and a description of the program in your own words. For example: // Suzy Student, CS&141, Autumn 2049, Section XX // Programming Assignment #1, 06/07/49 // // This program's behavior is ...
Step by Step Solution
3.45 Rating (148 Votes )
There are 3 Steps involved in it
public class Intro public static void mainString args SystemoutprintlnINNNNNNNNNN... View full answer

Get step-by-step solutions from verified subject matter experts


