Question: Create PHP page named directory_traversal_part1.php in your droplet web root This PHP page will display all files and folders of path that will be
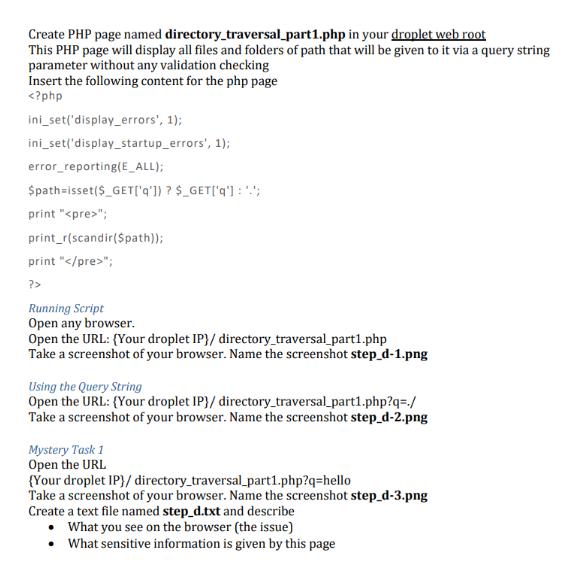
Create PHP page named directory_traversal_part1.php in your droplet web root This PHP page will display all files and folders of path that will be given to it via a query string parameter without any validation checking Insert the following content for the php page
Step by Step Solution
3.40 Rating (153 Votes )
There are 3 Steps involved in it
Solution Code explanation The code sets the error reporting level to display all errors and warnings It retrieves the value of the query string parameter q and assigns it to the variable path It uses ... View full answer

Get step-by-step solutions from verified subject matter experts


