Create the file /etc/sudoers.d/dbuser1 to configure dbuser1 so that the user can use sudo to run any
Fantastic news! We've Found the answer you've been seeking!
Question:
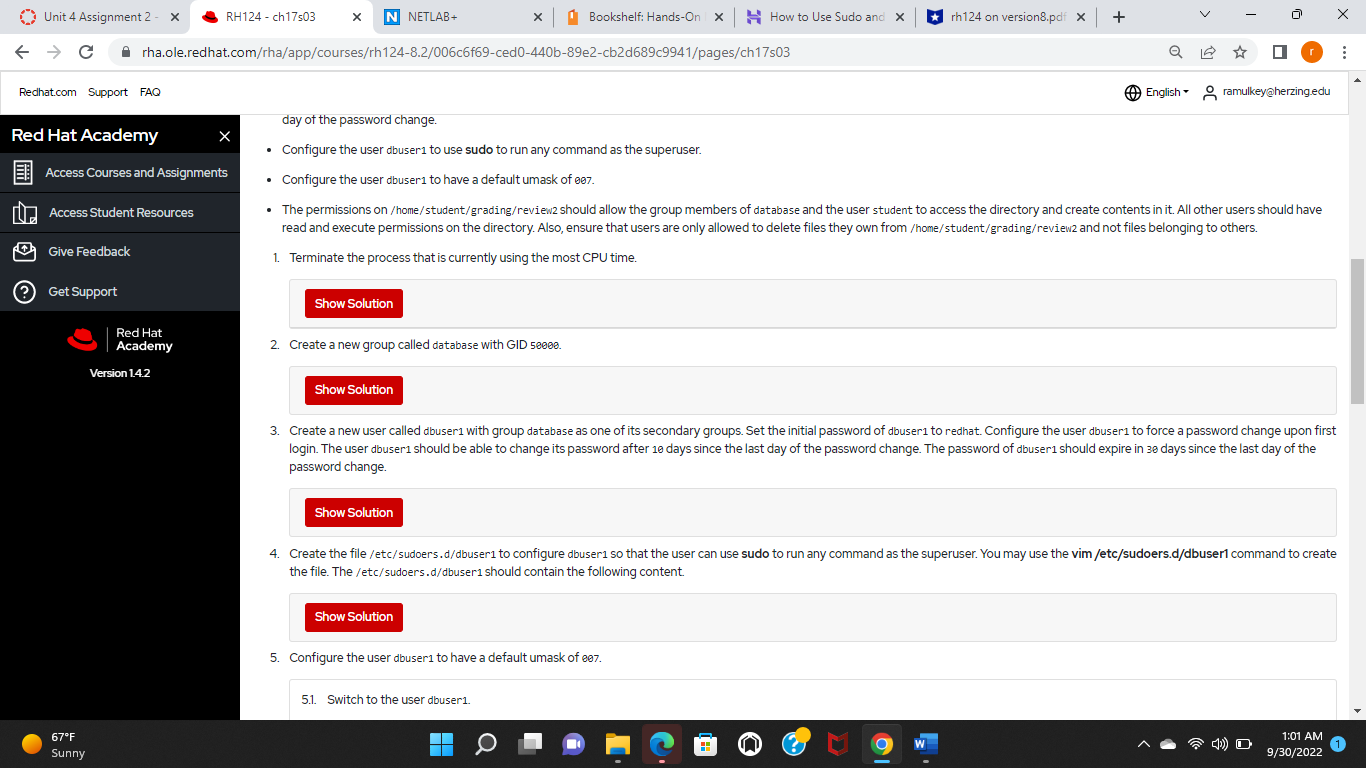
Create the file /etc/sudoers.d/dbuser1 to configure dbuser1 so that the user can use sudo to run any command as the superuser. You may use the vim /etc/sudoers.d/dbuser1 command to create the file. The /etc/sudoers.d/dbuser1 should contain the following content.
Transcribed Image Text:
Unit 4 Assignment 2 - X C Redhat.com Support FAQ !!! Red Hat Academy Access Student Resources Give Feedback Access Courses and Assignments (?) Get Support 67F Sunny RH124 - ch17s03 rha.ole.redhat.com/rha/app/courses/rh124-8.2/006c6f69-ced0-440b-89e2-cb2d689c9941/pages/ch17s03 Red Hat Academy Version 1.4.2 X X N NETLAB+ . Show Solution 2. Create a new group called database with GID 50000. Show Solution x | Show Solution day of the password change. Configure the user abuser 1 to use sudo to run any command as the superuser. Configure the user dbuser1 to have a default umask of 007. The permissions on /home/student/grading/review2 should allow the group members of database and the user student to access the directory and create contents in it. All other users should have read and execute permissions on the directory. Also, ensure that users are only allowed to delete files they own from /home/student/grading/review2 and not files belonging to others. 1. Terminate the process that is currently using the most CPU time. Bookshelf: Hands-On X Show Solution How to Use Sudo and X 5.1. Switch to the user dbuser1. 5. Configure the user dbuser1 to have a default umask of ee7. rh124 on version8.pdf x + 3. Create a new user called dbuser1 with group database as one of its secondary groups. Set the initial password of dbuser1 to redhat. Configure the user dbuser1 to force a password change upon first login. The user dbuser1 should be able to change its password after 10 days since the last day of the password change. The password of abuser1 should expire in 30 days since the last day of the password change. Q 4. Create the file/etc/sudoers.d/dbuser1 to configure dbuser1 so that the user can use sudo to run any command as the superuser. You may use the vim /etc/sudoers.d/dbuser1 command to create the file. The /etc/sudoers.d/dbuser1 should contain the following content. O English ramulkey@herzing.edu 4) O X 1:01 AM 9/30/2022 Unit 4 Assignment 2 - X C Redhat.com Support FAQ !!! Red Hat Academy Access Student Resources Give Feedback Access Courses and Assignments (?) Get Support 67F Sunny RH124 - ch17s03 rha.ole.redhat.com/rha/app/courses/rh124-8.2/006c6f69-ced0-440b-89e2-cb2d689c9941/pages/ch17s03 Red Hat Academy Version 1.4.2 X X N NETLAB+ . Show Solution 2. Create a new group called database with GID 50000. Show Solution x | Show Solution day of the password change. Configure the user abuser 1 to use sudo to run any command as the superuser. Configure the user dbuser1 to have a default umask of 007. The permissions on /home/student/grading/review2 should allow the group members of database and the user student to access the directory and create contents in it. All other users should have read and execute permissions on the directory. Also, ensure that users are only allowed to delete files they own from /home/student/grading/review2 and not files belonging to others. 1. Terminate the process that is currently using the most CPU time. Bookshelf: Hands-On X Show Solution How to Use Sudo and X 5.1. Switch to the user dbuser1. 5. Configure the user dbuser1 to have a default umask of ee7. rh124 on version8.pdf x + 3. Create a new user called dbuser1 with group database as one of its secondary groups. Set the initial password of dbuser1 to redhat. Configure the user dbuser1 to force a password change upon first login. The user dbuser1 should be able to change its password after 10 days since the last day of the password change. The password of abuser1 should expire in 30 days since the last day of the password change. Q 4. Create the file/etc/sudoers.d/dbuser1 to configure dbuser1 so that the user can use sudo to run any command as the superuser. You may use the vim /etc/sudoers.d/dbuser1 command to create the file. The /etc/sudoers.d/dbuser1 should contain the following content. O English ramulkey@herzing.edu 4) O X 1:01 AM 9/30/2022
Expert Answer:

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these computer network questions
-
"internet radios" for streaming audio, and personal video recorders and players. Describe design and evaluation processes that could be used by a start-up company to improve the usability of such...
-
Design a Java class that represents a cache with a fixed size. It should support operations like add, retrieve, and remove, and it should evict the least recently used item when it reaches capacity.
-
In Exercises 6567, consider a scalar function and a vector field F in space. Determine whether the expression is a vector field, a scalar function, or neither. Explain. div[curl()]
-
Rider Auto has developed the following production plan for its new auto part. Each unit passes through two departments before completion. The company has developed the following direct labor...
-
Recall that the 105 ill children in the sample were randomly divided into three groups: those who received a dosage of an over-the-counter cough medicine (DM), those who received a dosage of honey...
-
This appeal involves the validity of a will executed in contravention of an earlier contract to make mutual wills. A husband and wife signed a contract to make mutual wills and then executed those...
-
Major Instrument, Inc. manufactures two products: missile range instruments and space pressure gauges. During April, 50 range instruments and 300 pressure gauges were produced, and overhead costs of...
-
Part A An oxygen atom at a particular site within a DNA molecule can be made to execute simple harmonic motion when illuminated by infrared light. The oxygen atom is bound with a spring-like chemical...
-
Write a program to read names and average grades of students from a text file. Calculate their letter grades, print all the data in a table. Print the counts of each grade at the bottom of the table.
-
Which condition is necessary for a transaction to be considered a hostile takeover? Group of answer choices The target firm must be publicly traded. The target firm must be privately held. The...
-
how to evaluate the changes in loan asset quality and current quality going forward for a bank
-
For this discussion, pretend that you started a new business one year ago (any type of business of your choice) and address the following points: Explain one of these decision types that you might...
-
Case 2 12-shelf unit. 150 inches/shelf. 21,000 inches of current records. 6,000 projected inches needed for future. Calculate the number of filing units to be purchased. Show all calculations.
-
Please help!! Complete a ratio analysis of the top three (3) competitors in the industry using the company's financial statements. You could use financial statements, such as the Managerial Balance...
-
Crabtree corporation net income of $34000 was reported and dividends of $23000 were paid in 2013
-
The May 2014 revenue and cost information for Houston Outfitters, Inc. follow: Sales Revenue (at standard).............. $ 540,000 Cost of Goods Sold (at standard) ..........341,000 Direct Materials...
-
Kathy Kennedy (age 44) is a single taxpayer and she lives at 212 North Pine Way, Payson, AZ 85541. Her Social Security number is 467-98-9784. Kathy's earnings and income tax withholding as the...
-
Cedar Corporation has an S corporation election in effect. During the 2012 calendar tax year, the corporation had ordinary taxable income of $200,000, and on January 15, 2012, the corporation paid...
-
Quince Interests is a partnership with a tax year that ends September 30, 2012. During that year, Potter, a partner, received $3,000 per month as a guaranteed payment, and his share of partnership...
-
Go to https://www.youtube.com/watch?v=Fp9m4GNwGng to view a brief video on the Brazilian Jet manufacturer Embraer and their use of Critical Chain Project Management for maintenance services. How has...
-
It is sometimes argued that state revenue generated by lotteries is different from tax revenue because people choose to buy lottery tickets. Compare three state revenue sources cigarette excise...
-
Suppose that the demand for personalized license plates and the marginal cost of production in a state is as shown in Figure 16.1. If all the profits go to the government and the state wants to...

Study smarter with the SolutionInn App


