Criminals have discovered yet another way to steal money. They are combining phishing attacks, Trojan panies...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
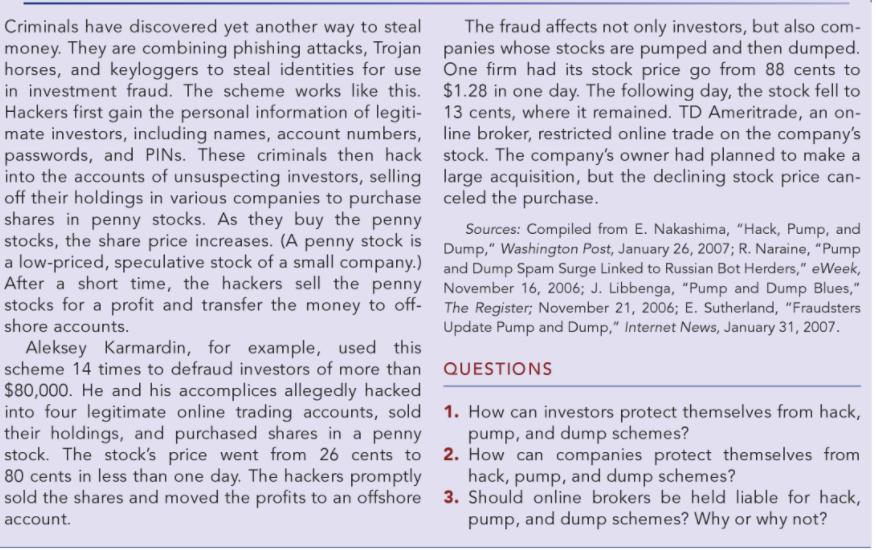
Criminals have discovered yet another way to steal money. They are combining phishing attacks, Trojan panies whose stocks are pumped and then dumped. horses, and keyloggers to steal identities for use One firm had its stock price go from 88 cents to in investment fraud. The scheme works like this. $1.28 in one day. The following day, the stock fell to Hackers first gain the personal information of legiti- 13 cents, where it remained. TD Ameritrade, an on- mate investors, including names, account numbers, line broker, restricted online trade on the company's passwords, and PINS. These criminals then hack stock. The company's owner had planned to make a into the accounts of unsuspecting investors, selling large acquisition, but the declining stock price can- off their holdings in various companies to purchase celed the purchase. shares in penny stocks. As they buy the penny stocks, the share price increases. (A penny stock is Dump," Washington Post, January 26, 2007; R. Naraine, "Pump a low-priced, speculative stock of a small company.) and Dump Spam Surge Linked to Russian Bot Herders," eWeek, After a short time, the hackers sell the penny November 16, 2006; J. Libbenga, "Pump and Dump Blues," stocks for a profit and transfer the money to off- The Register; November 21, 2006; E. Sutherland, "Fraudsters The fraud affects not only investors, but also com- Sources: Compiled from E. Nakashima, "Hack, Pump, and shore accounts. Update Pump and Dump," Internet News, January 31, 2007. Aleksey Karmardin, for example, used this scheme 14 times to defraud investors of more than QUESTIONS $80,000. He and his accomplices allegedly hacked into four legitimate online trading accounts, sold their holdings, and purchased shares in a penny stock. The stock's price went from 26 cents to 2. How can companies protect themselves from 80 cents in less than one day. The hackers promptly sold the shares and moved the profits to an offshore 3. Should online brokers be held liable for hack, 1. How can investors protect themselves from hack, pump, and dump schemes? hack, pump, and dump schemes? account. pump, and dump schemes? Why or why not? Criminals have discovered yet another way to steal money. They are combining phishing attacks, Trojan panies whose stocks are pumped and then dumped. horses, and keyloggers to steal identities for use One firm had its stock price go from 88 cents to in investment fraud. The scheme works like this. $1.28 in one day. The following day, the stock fell to Hackers first gain the personal information of legiti- 13 cents, where it remained. TD Ameritrade, an on- mate investors, including names, account numbers, line broker, restricted online trade on the company's passwords, and PINS. These criminals then hack stock. The company's owner had planned to make a into the accounts of unsuspecting investors, selling large acquisition, but the declining stock price can- off their holdings in various companies to purchase celed the purchase. shares in penny stocks. As they buy the penny stocks, the share price increases. (A penny stock is Dump," Washington Post, January 26, 2007; R. Naraine, "Pump a low-priced, speculative stock of a small company.) and Dump Spam Surge Linked to Russian Bot Herders," eWeek, After a short time, the hackers sell the penny November 16, 2006; J. Libbenga, "Pump and Dump Blues," stocks for a profit and transfer the money to off- The Register; November 21, 2006; E. Sutherland, "Fraudsters The fraud affects not only investors, but also com- Sources: Compiled from E. Nakashima, "Hack, Pump, and shore accounts. Update Pump and Dump," Internet News, January 31, 2007. Aleksey Karmardin, for example, used this scheme 14 times to defraud investors of more than QUESTIONS $80,000. He and his accomplices allegedly hacked into four legitimate online trading accounts, sold their holdings, and purchased shares in a penny stock. The stock's price went from 26 cents to 2. How can companies protect themselves from 80 cents in less than one day. The hackers promptly sold the shares and moved the profits to an offshore 3. Should online brokers be held liable for hack, 1. How can investors protect themselves from hack, pump, and dump schemes? hack, pump, and dump schemes? account. pump, and dump schemes? Why or why not?
Expert Answer:
Answer rating: 100% (QA)
1 Before investing read the document carefully they have to know where the stock trading don... View the full answer

Related Book For 

Posted Date:
Students also viewed these marketing questions
-
In what way is selling an investment for a gain potentially a negative in evaluating quality of earnings?
-
Companies often face a basket purchase situation when they buy real estate, because the acquisition usually involves both the land that is purchased and the building that is located on the land. If...
-
Companies often face a basket purchase situation when they buy real estate, because the acquisition usually involves both the land that is purchased and the building that is located on the land. If...
-
Being able to identify an industry to use for benchmarking yourfirm's results with similar companies is frequently not easy. Choose a type of business and go to www.naics.com. This Web site allows...
-
Explain why we conduct pairwise comparisons of treatment means. Discuss.
-
What is breakup value?
-
Describe the difference between maneuverability and controllability.
-
1. Describe the recovery strategies that were offered by the company to offset the customers complaint. Classify the recovery strategies based on the recovery strategy categories provided in this...
-
Under what circumstances do you think a company would seek private debt ( soliciting from a single party ) rather than public debt ( an open - to - the - public issuance, like a bond ) ?
-
The A-36 steel wires AB and AD each have a diameter of 2 mm and the unloaded lengths of each wire are LAC = 1.60 m and LAB = LAD = 2.00 m. Determine the required diameter of wire AC so that each wire...
-
You are working for an imports export company. In the current financial year, your company has an net income of $851,000 and plans to use a part of it as a retained earnings for a new new project...
-
Bees Company uses the marginal costing system. The company's budgeted and actual production of honey was 30,000 bottles for the period. The standard selling price per unit is $10.00 and actual sales...
-
What are 4 benefits of using recognized specifications for RFQs?
-
The general principle for what to capitalize when acquiring an asset is to include?
-
Your analyst is valuing an equity stake in a company. She estimates that, due to rising interest rates leading to a higher WACC, the company Enterprise Value has fallen to $100 million. She notes...
-
Kenny starts up eSouthPark, an Internet service, and leases office space in a building owned by Cartman. The lease requires Kenny to pay Cartman a base rental of $1,250, plus 10 percent of...
-
Last month, 5 customers of Macland Automotive bought the extended service plan with their purchase of a new car. All of their credit scores are given below. Calculate the standard deviation of this...
-
The percentage of completion and completed contract methods are described in the FASB ASC. Search the codification to find the paragraphs covering these topics, cite them, and copy the results.
-
An unknown element is a nonmetal and has a valence electron configuration of ns2np4. a. How many valence electrons does this element have? b. What are some possible identities for this element? c....
-
Iron is present in the earths crust in many types of minerals. The iron oxide minerals are hematite (Fe2O3) and magnetite (Fe3O4). What is the oxidation state of iron in each mineral? The iron ions...
-
Calculate the values of S and DG for each of the following processes at 298 K: H2O(l,298 K) H2O(g, V = 1000. L/mol) H2O(l,298 K) H2O(g, V = 100. L/mol) The standard enthalpy of vaporization for...
-
Model your car by using analogy approach and stable approach. Which one do you like more and why?
-
Model your dream house by using analogy approach and stable approach. Which one do you like more and why?
-
Try to find 23 scenarios where this pattern can be applicable.

Study smarter with the SolutionInn App