Question: Dear experts, pls help me to do as many as you can, i will definitely provide upvotes. Task 1 Critical National Information Infrastructure (CNII) 1.
Dear experts, pls help me to do as many as you can, i will definitely provide upvotes.
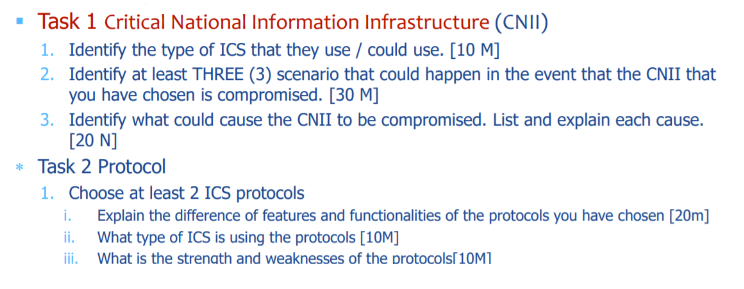
Task 1 Critical National Information Infrastructure (CNII) 1. Identify the type of ICS that they use / could use. [10 m] 2. Identify at least THREE (3) scenario that could happen in the event that the CNII that you have chosen is compromised. [30 M] 3. Identify what could cause the CNII to be compromised. List and explain each cause. [20 N] * Task 2 Protocol 1. Choose at least 2 ICS protocols i. Explain the difference of features and functionalities of the protocols you have chosen [20m] ii. What type of ICS is using the protocols [10M] iii. What is the strength and weaknesses of the protocols[10MI Task 1 Critical National Information Infrastructure (CNII) 1. Identify the type of ICS that they use / could use. [10 m] 2. Identify at least THREE (3) scenario that could happen in the event that the CNII that you have chosen is compromised. [30 M] 3. Identify what could cause the CNII to be compromised. List and explain each cause. [20 N] * Task 2 Protocol 1. Choose at least 2 ICS protocols i. Explain the difference of features and functionalities of the protocols you have chosen [20m] ii. What type of ICS is using the protocols [10M] iii. What is the strength and weaknesses of the protocols[10MI
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


