Question: Define a function similar to the built-in reverse function, except that it acts recursively, reversing the order the members of any nested sublists. You
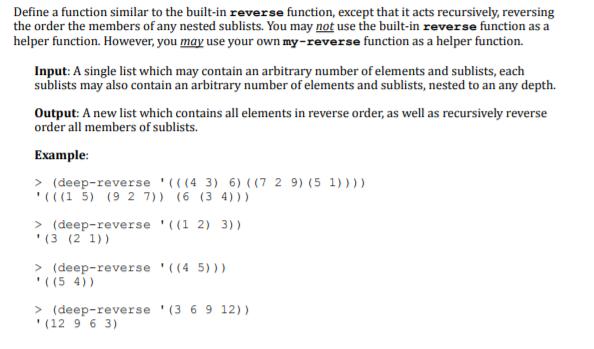
Define a function similar to the built-in reverse function, except that it acts recursively, reversing the order the members of any nested sublists. You may not use the built-in reverse function as a helper function. However, you may use your own my-reverse function as a helper function. Input: A single list which may contain an arbitrary number of elements and sublists, each sublists may also contain an arbitrary number of elements and sublists, nested to an any depth. Output: A new list which contains all elements in reverse order, as well as recursively reverse order all members of sublists. Example: > (deep-reverse '(((43) 6) ((7 2 9) (5 1)))) (((15) (9 2 7)) (6 (34))) > (deep-reverse '((1 2) 3)) (3 (21)) > (deep-reverse ((4.5))) '((54)) > (deep-reverse (3 6 9 12)) (12 9 6 3)
Step by Step Solution
3.31 Rating (145 Votes )
There are 3 Steps involved in it
Heres a recursive function deepreverse that reverses the order of elements in a list including any n... View full answer

Get step-by-step solutions from verified subject matter experts


