Question: Details 1. Skill Builder Exercise - Working with PRTK This exercise requires the Mantooth and Washer case. Open the Mantooth case and Washer Case.
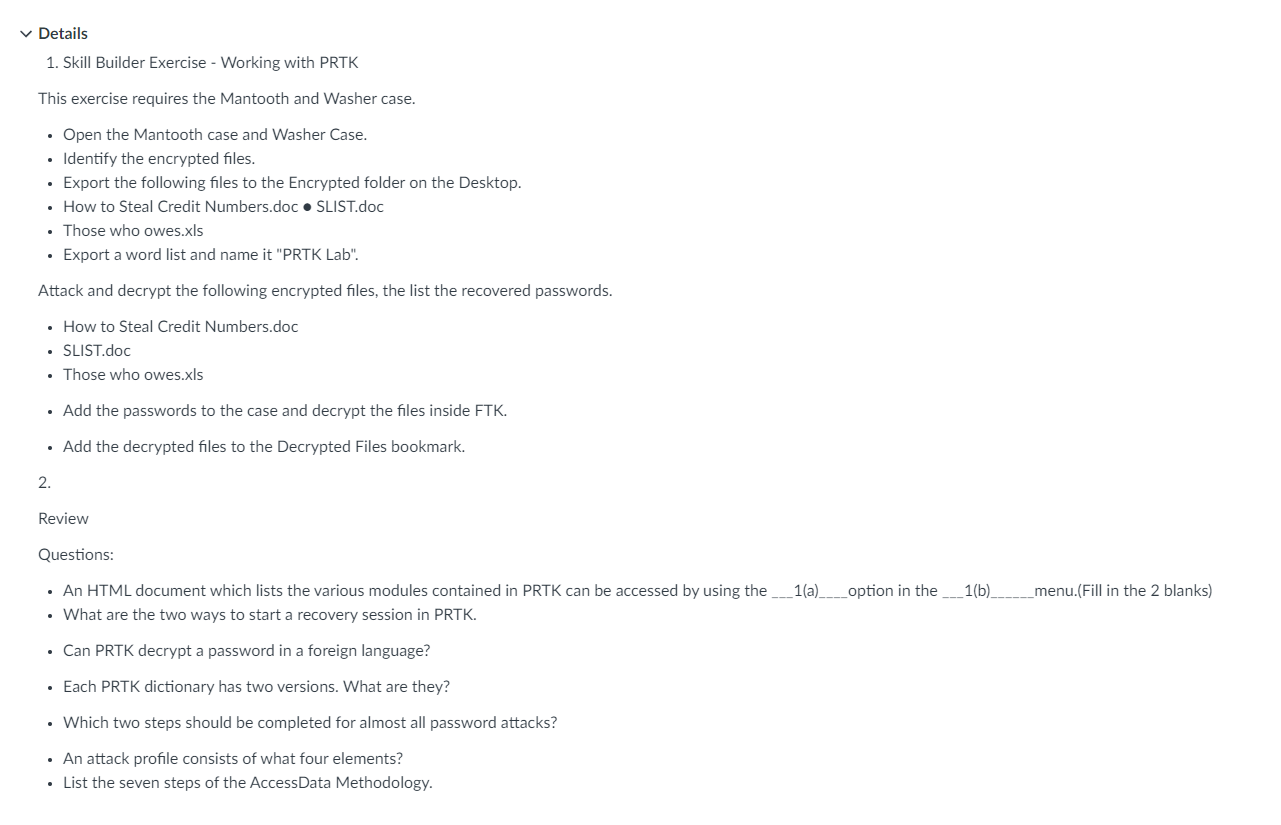
Details 1. Skill Builder Exercise - Working with PRTK This exercise requires the Mantooth and Washer case. Open the Mantooth case and Washer Case. Identify the encrypted files. Export the following files to the Encrypted folder on the Desktop. How to Steal Credit Numbers.doc SLIST.doc Those who owes.xls Export a word list and name it "PRTK Lab". Attack and decrypt the following encrypted files, the list the recovered passwords. How to Steal Credit Numbers.doc SLIST.doc Those who owes.xls Add the passwords to the case and decrypt the files inside FTK. Add the decrypted files to the Decrypted Files bookmark. 2. Review Questions: An HTML document which lists the various modules contained in PRTK can be accessed by using the ____1(a)_______option in the ____1(b)_ What are the two ways to start a recovery session in PRTK. Can PRTK decrypt a password in a foreign language? Each PRTK dictionary has two versions. What are they? Which two steps should be completed for almost all password attacks? An attack profile consists of what four elements? List the seven steps of the AccessData Methodology. __menu.(Fill in the 2 blanks)
Step by Step Solution
There are 3 Steps involved in it
I can see that youve provided a set of tasks and questions related to using PRTK Password Recovery T... View full answer

Get step-by-step solutions from verified subject matter experts


