Determine the IP address of the web server. You need to provide a screen capture to justify
Fantastic news! We've Found the answer you've been seeking!
Question:
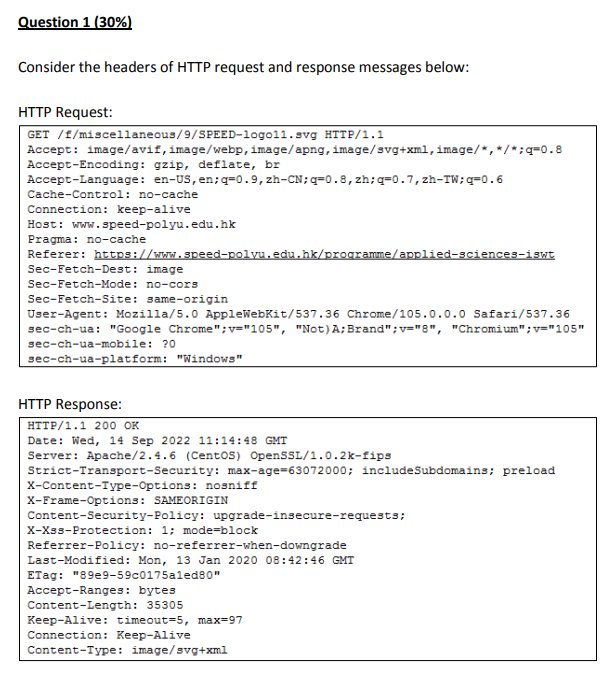
Determine the IP address of the web server. You need to provide a screen capture to justify how you find the answer.
Transcribed Image Text:
Question 1 (30%) Consider the headers of HTTP request and response messages below: HTTP Request: GET /f/miscellaneous/9/SPEED-logo11.svg HTTP/1.1 Accept: image/avif, image/webp, image/apng, image/svg+xml image/*,*/*;q=0.8 Accept-Encoding: gzip, deflate, br Accept-Language: en-US, en;q=0.9, zh-CN;q=0.8, zh;q=0.7, zh-TW;q=0.6 Cache-Control: no-cache Connection: keep-alive Host: www.speed-polyu.edu.hk Pragma: no-cache Referer: https://www.speed-polyu.edu.hk/programme/applied-sciences-iswt Sec-Fetch-Dest: image Sec-Fetch-Mode: no-cors Sec-Fetch-Site: same-origin User-Agent: Mozilla/5.0 AppleWebKit/537.36 Chrome/105.0.0.0 Safari/537.36 sec-ch-ua: "Google Chrome"; v="105", "Not) A; Brand"; v="8", "Chromium"; v="105" sec-ch-ua-mobile: ?0 sec-ch-ua-platform: "Windows" HTTP Response: HTTP/1.1 200 OK Date: Wed, 14 Sep 2022 11:14:48 GMT Server: Apache/2.4.6 (CentOS) OpenSSL/1.0.2k-fips Strict-Transport-Security: max-age=63072000; includeSubdomains; preload X-Content-Type-Options: nosniff X-Frame-Options: SAMEORIGIN Content-Security-Policy: upgrade-insecure-requests; X-XSS-Protection: 1; mode=block Referrer-Policy: no-referrer-when-downgrade Last-Modified: Mon, 13 Jan 2020 08:42:46 GMT ETag: "89e9-59c0175a1ed80" Accept-Ranges: bytes Content-Length: 35305 Keep-Alive: timeout-5, max 97 Connection: Keep-Alive Content-Type: image/svg+xml Question 1 (30%) Consider the headers of HTTP request and response messages below: HTTP Request: GET /f/miscellaneous/9/SPEED-logo11.svg HTTP/1.1 Accept: image/avif, image/webp, image/apng, image/svg+xml image/*,*/*;q=0.8 Accept-Encoding: gzip, deflate, br Accept-Language: en-US, en;q=0.9, zh-CN;q=0.8, zh;q=0.7, zh-TW;q=0.6 Cache-Control: no-cache Connection: keep-alive Host: www.speed-polyu.edu.hk Pragma: no-cache Referer: https://www.speed-polyu.edu.hk/programme/applied-sciences-iswt Sec-Fetch-Dest: image Sec-Fetch-Mode: no-cors Sec-Fetch-Site: same-origin User-Agent: Mozilla/5.0 AppleWebKit/537.36 Chrome/105.0.0.0 Safari/537.36 sec-ch-ua: "Google Chrome"; v="105", "Not) A; Brand"; v="8", "Chromium"; v="105" sec-ch-ua-mobile: ?0 sec-ch-ua-platform: "Windows" HTTP Response: HTTP/1.1 200 OK Date: Wed, 14 Sep 2022 11:14:48 GMT Server: Apache/2.4.6 (CentOS) OpenSSL/1.0.2k-fips Strict-Transport-Security: max-age=63072000; includeSubdomains; preload X-Content-Type-Options: nosniff X-Frame-Options: SAMEORIGIN Content-Security-Policy: upgrade-insecure-requests; X-XSS-Protection: 1; mode=block Referrer-Policy: no-referrer-when-downgrade Last-Modified: Mon, 13 Jan 2020 08:42:46 GMT ETag: "89e9-59c0175a1ed80" Accept-Ranges: bytes Content-Length: 35305 Keep-Alive: timeout-5, max 97 Connection: Keep-Alive Content-Type: image/svg+xml
Expert Answer:

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these computer network questions
-
re Regular Languages and Finite Automata (a) Let L be the set of all strings over the alphabet {a, b} that end in a and do not contain the substring bb. Describe a deterministic finite automaton...
-
Data set Theory Assume an informational record with one association parent including matches (a, b) where a can't try not to be a parent of b. (a) Write a Datalog demand which gives the graph of...
-
Engineers observe that about 90% of graphite samples fracture within five hours when subjected to a certain stress. (a) If the time to fracture is modeled with an exponential distribution, what would...
-
Describe Toyota's underlying concept of ethics for supply chain management. Explain how Toyota's ethical concept ensures quality throughout the supply chain. Define Toyota's quality benchmarks and...
-
(Pension Worksheet - Missing Amounts) Kramer Co. has prepared the following pension worksheet. Unfortunately, several entries in the worksheet are not decipherable. The company has asked your...
-
Continue with ex.3 and record the relevant transactions in the bank book. Ex.3 The organisation maintains a three-column cash book. It submits the details of following cash/bank transactions for the...
-
Using the standard unit costs that you computed in SE and the following actual cost and usage data, compute the direct labor rate and direct labor efficiency variances: Direct labor hours...
-
Suppose that the supply curve of serving in the military is S(P) = P, where Q = S(P) is several hours employed in military service a day. There are only mercenaries in the army (there is no draft). P...
-
A decision analyst is asked to asses a multi attribute utility function for the government that wishes to revise its healthcare policies. The team identified the cost and the quality of care provided...
-
Explain a situation that you have been in where excessive turnover or excessive absenteeism was an issue. How was the situation handled? Do you believe the situation was handled well or what do you...
-
imagine that you are living during one of the time periods we are studying during the semester, and also that you are a close friend of Socrates write a series of diary entries (8-10 entries in all)...
-
AI Rewrite this AI: This article provides valuable insights into the trends and challenges facing the accounting profession, particularly in terms of education and recruitment. It offers data on the...
-
Consider the probability density curve with some areas indicated. Find: a) The proportion of the population is between 0 and 1. b) The probability that a randomly selected value will be between 1 and...
-
Explain the differences between decision-making under certainty, decision-making under risk, and decision-making under uncertainty. Describe the Critical Path method. Identify potential issues...
-
The tree musketeers Alexander Dumas Describe a certain literary piece Explain major scenes out of the given summary of literary piece Imagine an ending twist
-
For the data in Exercise 17-19, use the FIFO method to summarize total costs to account for, and assign these costs to units completed and transferred out, and to units in ending work in process....
-
Consider a virtual-circuit network. Suppose the VC number is a 8-bit field. a) What is the maximum number of virtual circuits that can be carried over a link? b) Suppose a central node determines...
-
Recall the macroscopic description of TCP throughput. In the period of time from when the connection's rate varies from W/(2. RTT) to W/RTT, only one packet is lost (at the very end of the period)....
-
Consider the two basic approaches identified for achieving broadcast, unicast emulation and network-layer (i.e., router-assisted) broadcast, and suppose spanning-tree broadcast is used to achive...
-
The following are summaries of the cash book and bank accounts of J. Duncan who does not keep his books using the double entry system. You are required to: (a) Calculate the value of J. Duncan's...
-
Read the following and answer the questions below. On 31 December 2015 the bank column of C. Tench's cash book showed a debit balance of 1,500. The monthly bank statement written up to 31 December...
-
The bank columns in the cash book for June 2016 and the bank statement for that month for D. Hogan are as follows: You are required to: () Write the cash book up to date to take the above into...

Study smarter with the SolutionInn App


