Question: Discuss the following DiffieHellman scheme.ls an attack possible? And what would happen? Alice to Bob I'm Alice, (ga mod p Alice Bob to Alice gb
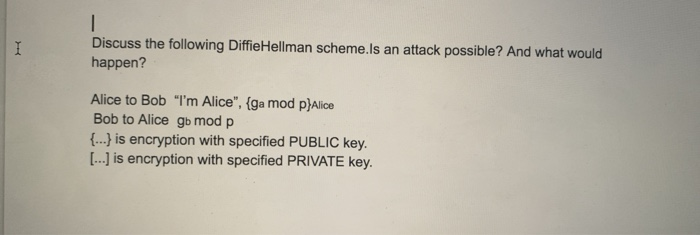
Discuss the following DiffieHellman scheme.ls an attack possible? And what would happen? Alice to Bob "I'm Alice", (ga mod p Alice Bob to Alice gb mod p (.. is encryption with specified PUBLIC key. L..] is encryption with specified PRIVATE key
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


