Question: Doing a signature with RSA alone on a long message would be too slow. Suppose we could do division quickly. Would it be reasonable
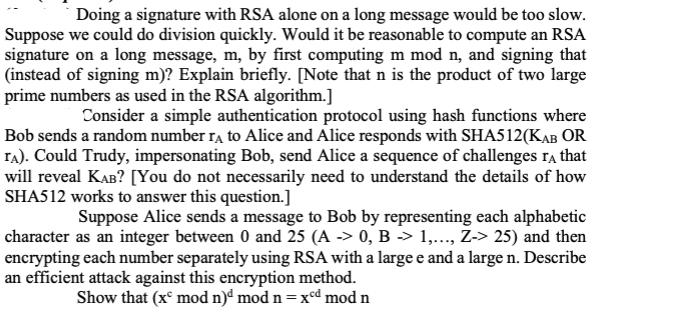
Doing a signature with RSA alone on a long message would be too slow. Suppose we could do division quickly. Would it be reasonable to compute an RSA signature on a long message, m, by first computing m mod n, and signing that (instead of signing m)? Explain briefly. [Note that n is the product of two large prime numbers as used in the RSA algorithm.] Consider a simple authentication protocol using hash functions where Bob sends a random number ra to Alice and Alice responds with SHA512(KAB OR TA). Could Trudy, impersonating Bob, send Alice a sequence of challenges ra that will reveal KAB? [You do not necessarily need to understand the details of how SHA512 works to answer this question.] Suppose Alice sends a message to Bob by representing each alphabetic character as an integer between 0 and 25 (A -> 0, B -> 1,..., Z-> 25) and then encrypting each number separately using RSA with a large e and a large n. Describe an efficient attack against this encryption method. Show that (x mod n)d mod n = xed mod n
Step by Step Solution
There are 3 Steps involved in it
RSA Signature on Long Messages If we could perform division quickly computing an RSA signature on a ... View full answer

Get step-by-step solutions from verified subject matter experts


