Question: Figure 1 Code snippet An attacker connects and submits this (Figure 2): Hello. What's your name? xebx1fx5ex80x76x68x31xCOx88x46x67x89x46x0cxbexxObx89x63x8dx4ex68x8dx56x0cxcdx80x31xdbx89xd8 *40xcdx80xe8xdcixffixffixff/bin/sh Figure 2 Attacker's input a. Explain what
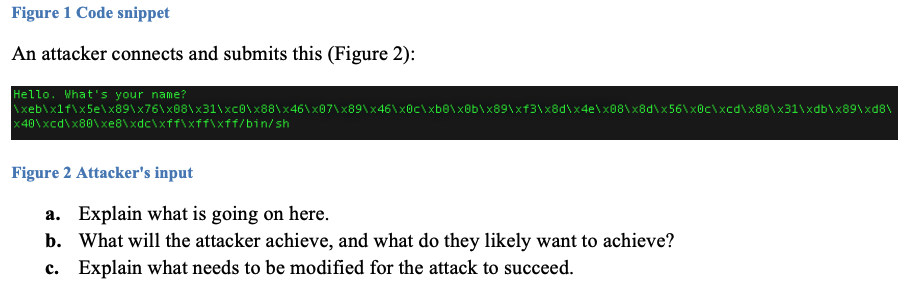
Figure 1 Code snippet An attacker connects and submits this (Figure 2): Hello. What's your name? \xeb\x1f\x5e\x80\x76\x68\x31\xCO\x88\x46\x67\x89\x46\x0c\xbexxOb\x89\x63\x8d\x4e\x68\x8d\x56\x0c\xcd\x80\x31\xdb\x89\xd8\ *40\xcd\x80\xe8\xdcixffixffixff/bin/sh Figure 2 Attacker's input a. Explain what is going on here. b. What will the attacker achieve, and what do they likely want to achieve? c. Explain what needs to be modified for the attack to succeed
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


