For the EIGamal cryptosystem, let the public key of Alice be (p, g, h), wherep is...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
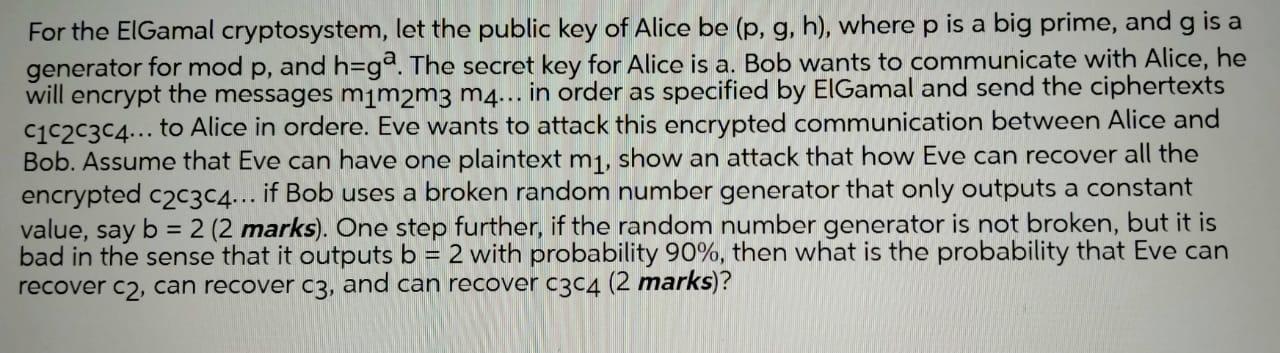
For the EIGamal cryptosystem, let the public key of Alice be (p, g, h), wherep is a big prime, and g is a generator for mod p, and h3gª. The secret key for Alice is a. Bob wants to communicate with Alice, he will encrypt the messages mim2m3 m4... in order as specified by EIGamal and send the ciphertexts C1C2C3C4... to Alice in ordere. Eve wants to attack this encrypted communication between Alice and Bob. Assume that Eve can have one plaintext m1, show an attack that how Eve can recover all the encrypted c2c3c4... if Bob uses a broken random number generator that only outputs a constant value, say b = 2 (2 marks). One step further, if the random number generator is not broken, but it is bad in the sense that it outputs b = 2 with probability 90%, then what is the probability that Eve can recover c2, can recover c3, and can recover c3C4 (2 marks)? %3D For the EIGamal cryptosystem, let the public key of Alice be (p, g, h), wherep is a big prime, and g is a generator for mod p, and h3gª. The secret key for Alice is a. Bob wants to communicate with Alice, he will encrypt the messages mim2m3 m4... in order as specified by EIGamal and send the ciphertexts C1C2C3C4... to Alice in ordere. Eve wants to attack this encrypted communication between Alice and Bob. Assume that Eve can have one plaintext m1, show an attack that how Eve can recover all the encrypted c2c3c4... if Bob uses a broken random number generator that only outputs a constant value, say b = 2 (2 marks). One step further, if the random number generator is not broken, but it is bad in the sense that it outputs b = 2 with probability 90%, then what is the probability that Eve can recover c2, can recover c3, and can recover c3C4 (2 marks)? %3D
Expert Answer:
Answer rating: 100% (QA)
AElGamal Encryption Algorithm ElGamal encryption is an publickey cryptosystem It uses asymmetric key encryption for communicating between two parties ... View the full answer

Related Book For 

Discrete and Combinatorial Mathematics An Applied Introduction
ISBN: 978-0201726343
5th edition
Authors: Ralph P. Grimaldi
Posted Date:
Students also viewed these computer engineering questions
-
Bob wants to communicate with Alice for sending some confidential data over the network. Trudy is an intruder and pretending to be Alice, and in an attempt to intercept traffic between Bob and Alice...
-
Alice wants to communicate with Bob, using public-key cryptography. She establishes a connection to someone she hopes is Bob. She asks him for his public key and he sends it to her in plaintext along...
-
Alice wants to support her son Bob if he looks for work but not otherwise. Bob wants to try to find a job only if Alice does not support his life of indolence. Their payoff matrix is Alice and Bob...
-
Freight and other handling charges on goods out on consignment are part of the cost of goods consigned. What is its appropriate account title in the income statement prepared by the consignor?...
-
In reference to Exercise 6 in Chapter 11, explain why S. 0.
-
The balance sheet of PQ Ltd. on 31 st December 1985 is as under: The preference shares are to be redeemed at 10% premium along with dividend due for 1985. The company issued 45,000 equity shares of...
-
For the composite properties and environmental conditions described in Examples 3.6, 4.7, and 5.3, determine the hygrothermally degraded values of the longitudinal and transverse tensile strengths....
-
Santana Music is a U.S.-based MNC whose foreign subsidiary had pretax income of $55,000; all after-tax income is available in the form of dividends to the parent company. The local tax rate is 40%,...
-
What is performance management systems? Do the companies where you (or others you know) have worked used performance management systems rather than performance appraisal systems? If yes, what kind of...
-
A 2 -year bond with a semiannual coupon rate of \(4 \%\) per annum is trading at par \((100 \%)\). (a) What is its spot semiannual yield? (b) Assume one can borrow at \(3 \%\) p.a. simple interest...
-
Write a Python program that consists of two functions: 1) input_2_numbers(): return the two positive integer. 2) display LCM(x, y): calculate the Least Common Multiple (LCM) of the two integers, and...
-
Suppose a student performed a similar experiment with a different unknown. Given the data in the table, what is the van't Hoff factor of the unknown substance? i = Kr of water freezing point of pure...
-
You own a restaurant. You just read that a recession will cause income to decrease by 10% this year. If this forecast turns out to be true, it will impact your restaurant. Income elasticity is 2.2....
-
WINDHEAD CORP BALANCE SHEET For the year ended December 31, 2023 Cash $41,226 Notes Receivable $16,000 Accounts Receivable $38,300 Less;Allowance for Doubtful Accounts -$5,164 Inventories ...
-
Albert has to clean his room on one of the the next 4 days. Cleaning on Day 1 has a utility cost of 18, cleaning on Day 2 has a utility cost of 30, cleaning on Day 3 has a utility cost of 48, and...
-
It consists of an outer material (like glass), and an inn material(like sand) that flows through the upper chamber do below, and the width of the opening between is adjusted measure the flow of time....
-
Metlock corp is nearing the end of its secA company's bonds currently sell for $1,150. The coupon rate is 10% with semi-annual payments, have a 15-year maturity, with $1,000 par value. The bonds can...
-
Explain briefly what is meant by electronic data interchange (EDI). How does EDI affect a companys audit trail?
-
Find the value of sum after the given program segment is executed. (Here i, j, k, increment, and sum are integer variables.) increment : = 0 sum : = 0 for i := 1 to 10 do for j : = 1 to i do for k :...
-
Determine the sequence generated by each of the following generating functions. (a) f(x) = (2x - 3)3 (b) f(x) = x4/(l - x) (c) f(x) = x3/(l - x2) (d) f(x) = 1/(1 + 3x) (e) f(x) = 1/(3 -x) (f) f(x) =...
-
Let G be the undirected graph in Fig. 11.27(a). (a) How many connected subgraphs of G have four vertices and include a cycle? (b) Describe the subgraph G1 (of G) in part (b) of the figure first, as...
-
Use the code given earlier for R to make this plot. The command would be plot(percentage)
-
Why would you not feel comfortable computing a Pearson correlation on the data in Exercise 9.10? Exercise 9.10 Down syndrome is another problem that psychologists deal with. It has been proposed that...
-
In Exercise 9.1 the percentage of mothers over 40 does not appear to be important, and yet it is a risk factor in other societies. Why do you think that this might be? Exercise 9.1 In Sub-Saharan...

Study smarter with the SolutionInn App