Question: For the initial value problem y' (t) = f(t, y), y(0) = yo, t0, consider the 0-method Yn+1 Yn+h[Of(tns Yn) + (1-0)f(tn+1; Yn+1)], where
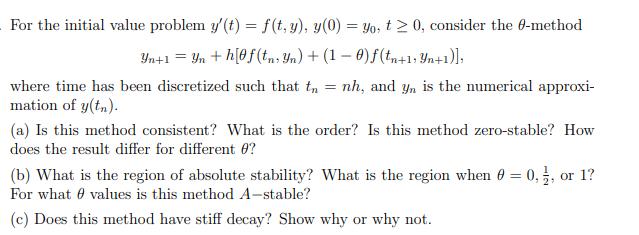
For the initial value problem y' (t) = f(t, y), y(0) = yo, t0, consider the 0-method Yn+1 Yn+h[Of(tns Yn) + (1-0)f(tn+1; Yn+1)], where time has been discretized such that tn = nh, and yn is the numerical approxi- mation of y(tn). (a) Is this method consistent? What is the order? Is this method zero-stable? How does the result differ for different 0? (b) What is the region of absolute stability? What is the region when 0 = 0, 1, or 1? For what values is this method A-stable? (c) Does this method have stiff decay? Show why or why not.
Step by Step Solution
3.39 Rating (152 Votes )
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


