Question: Get the solution codes for Healthcare service application - springboot --- Required files are uploaded in the below 1. Healthcare Service - Spring Boot You
Get the solution codes for Healthcare service application - springboot --- Required files are uploaded in the below 
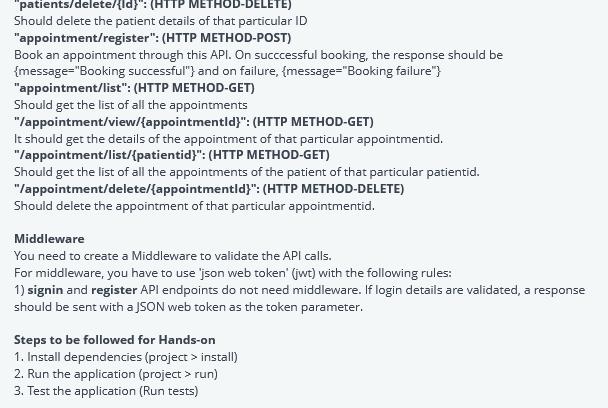

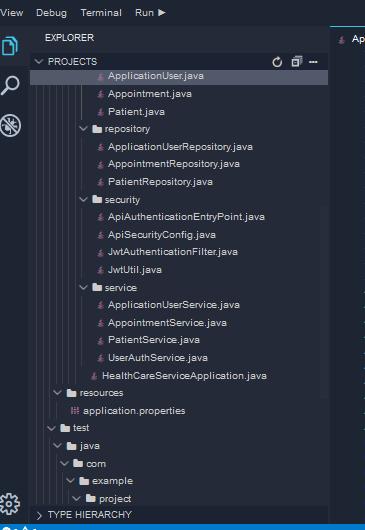
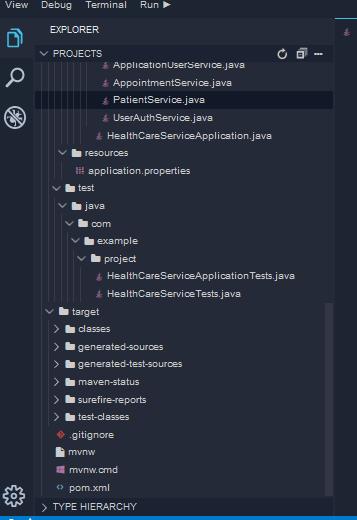
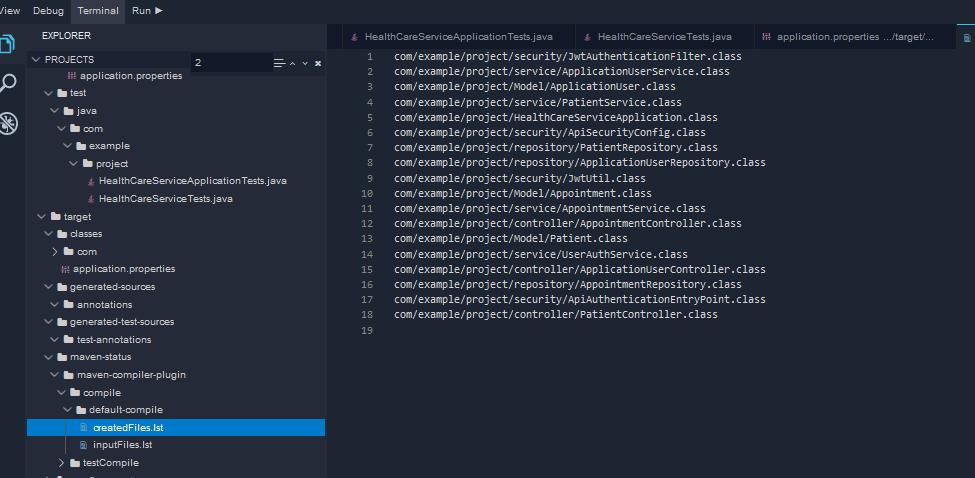
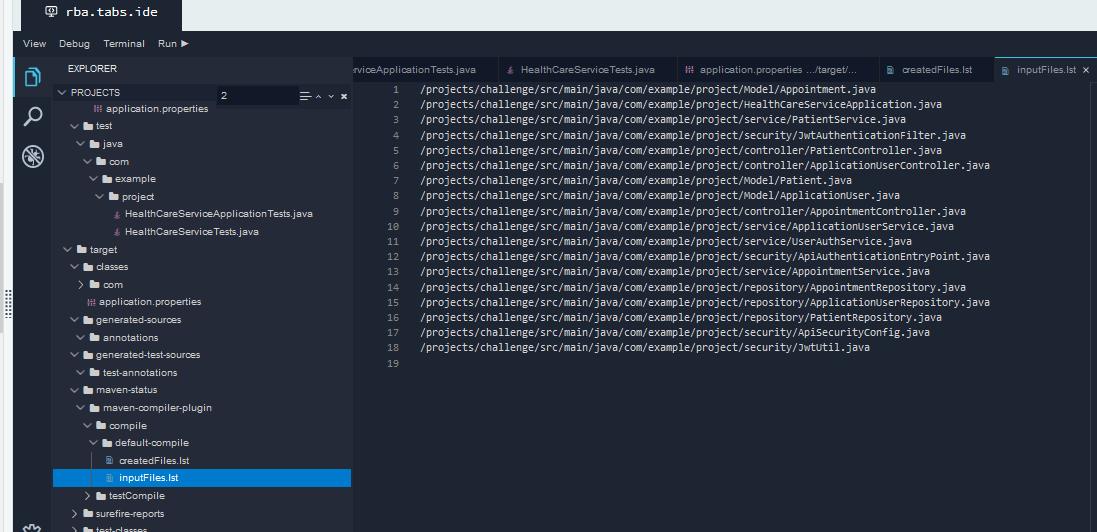

1. Healthcare Service - Spring Boot You have to create an API for a healthcare service. The following are the details of the API endpoints. register: (HTTP METHOD-POST) This endpoint should register the application user. On successful registration, the response should be {message=""Registration successful"") and on failure, the response should be {message="Password or username policy failed"} signin: (HTTP METHOD-POST) Users should be able to sign in through this endpoint by providing their email and password. On successful login, the response should be { message = "Authentication successful!", token = JWTtoken, id=user.ld}; and on failure, the response should be {message="Username or Password is Incorrect."} "viewprofile/{userld}": (HTTP METHOD-GET) This API should return the details of all the application users. "editprofile/{userld}": (HTTP METHOD-GET) This API should allow you to edit the details of an application user. "patients/register": (HTTP METHOD-POST) An application user should register the patient through this API. On succcessful registration, the response should be {message="Registration successful") and on failure, {message="Registration failure"} "patients/list/": (HTTP METHOD-GET) Should return a list of all the patients. "patients/view/{id}": (HTTP METHOD-GET) Should return details of the single user of that particular ID "patients/delete/{id}": (HTTP METHOD-DELETE) Should delete the patient details of that particular ID "appointment/register": (HTTP METHOD-POST) Book an appointment through this API. On succcessful booking, the response should be {message="Booking successful") and on failure, {message="Booking failure"}
Step by Step Solution
3.43 Rating (156 Votes )
There are 3 Steps involved in it
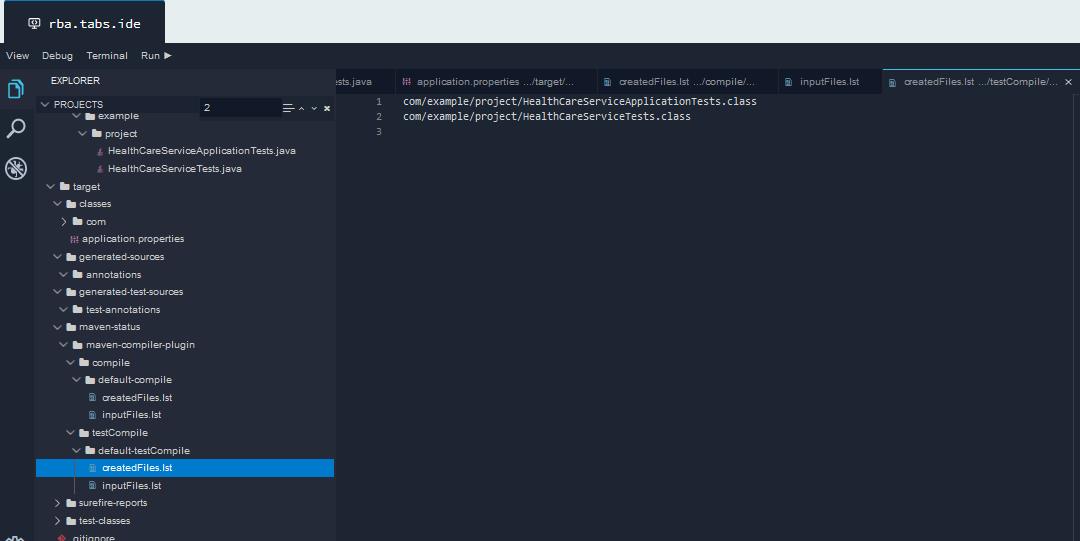
Here are the solution codes for the healthcare service application Java package comexampleproject import orgspringframeworkbootSpringApplication import orgspringframeworkbootautoconfigureSpringBootApp... View full answer

Get step-by-step solutions from verified subject matter experts


