Question: Given the queue shown below, where the numbers represent packets that belong to different flows. Assuming that these packets have arrived and queued in
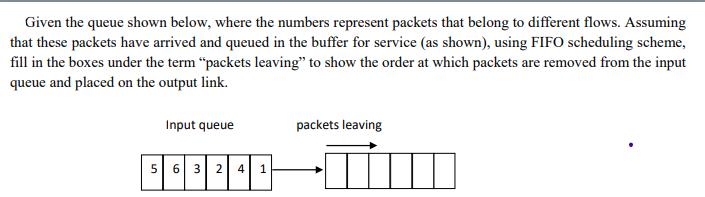
Given the queue shown below, where the numbers represent packets that belong to different flows. Assuming that these packets have arrived and queued in the buffer for service (as shown), using FIFO scheduling scheme, fill in the boxes under the term "packets leaving" to show the order at which packets are removed from the input queue and placed on the output link. 5 Input queue 6 3 2 4 1 packets leaving
Step by Step Solution
There are 3 Steps involved in it
Answer Solution Here all Packets arrived at same time so no need to sa le ... View full answer

Get step-by-step solutions from verified subject matter experts


